 Table of Contents
Table of Contents
- NIST 800-53 Vendor Management: How to Manage Third-Party Risk
- Third-Party Risk Controls in NIST 800-53
- Supply Chain Risk Management (SR Family)
- How to Assess Vendors Against NIST 800-53 Controls
- Building a Vendor Compliance Program
- How to Simplify NIST 800-53 Vendor Management
- Key Takeaways
-
NIST 800-53 Vendor Management FAQs
- What NIST 800-53 controls apply to vendor management?
- Is the SR family new in NIST 800-53 Rev 5?
- How do you assess a vendor against NIST 800-53?
- Does NIST 800-53 require continuous vendor monitoring?
- What is the difference between the SA and SR families for vendor risk?
- How many SR controls are in the Moderate baseline?
NIST 800-53 Vendor Management: How to Manage Third-Party Risk
NIST 800-53 vendor management uses the NIST 800-53 System and Services Acquisition (SA) and Supply Chain Risk Management (SR) control families to govern third-party risk across the vendor lifecycle, from acquisition through monitoring and disposal. Third-party breaches drive a growing share of security incidents, and these 28 controls define what organizations must do in response.
NIST Special Publication 800-53 Rev 5, the federal government’s primary security and privacy control catalog, required under the Federal Information Security Modernization Act (FISMA) and referenced by FedRAMP, dedicates two control families to third-party risk: System and Services Acquisition (SA) with 16 controls and Supply Chain Risk Management (SR) with 12 controls.
The SR family is new in Rev 5, carved out of SA-12 (Rev 4) to give supply chain risk its own policy, assessment, and monitoring requirements. Together, SA and SR account for 28 of the standard’s 1,196 controls across 20 families, all focused on how organizations acquire, assess, and monitor external providers.
This guide is part of our NIST 800-53 complete resource center and covers both the SA and SR control families in detail. It also includes a step-by-step vendor assessment process, guidance on building a tiered vendor compliance program, and practical implementation advice aligned to SA and SR requirements.
Third-Party Risk Controls in NIST 800-53
NIST 800-53 addresses third-party risk through two control families: System and Services Acquisition (SA), with 16 controls, and Supply Chain Risk Management (SR), with 12 controls added in Rev 5.
NIST 800-53 vendor management is the practice of using NIST 800-53 security and privacy controls to govern third-party risk. The System and Services Acquisition (SA) family (16 controls) and the Supply Chain Risk Management (SR) family (12 controls) set the requirements for how organizations acquire, assess, and monitor external service providers.
SA Family: Acquisition and Procurement
The SA family governs how organizations bring vendors in. It covers the system development lifecycle, acquisition processes, external system services, developer security requirements, and supply chain protections.
Two SA controls are central to vendor management:
- SA-04 (Acquisition Process): Requires organizations to include security and privacy requirements in vendor contracts before any work begins. Vendors agree to those controls upfront, making accountability part of the procurement record. For federal software acquisitions, those requirements typically reference NIST SP 800-218 (Secure Software Development Framework), the SSDF that OMB M-22-18 required software producers to attest conformance with. OMB M-26-05 superseded that mandate in January 2026 with a risk-based, agency-tailored approach.
- SA-09 (External System Services): Organizations must define security requirements for external service providers, assign oversight responsibilities, and monitor vendor compliance on an ongoing basis. This keeps the relationship auditable over the life of the contract.
SR Family: Dedicated Supply Chain Controls (New in Rev 5)
The SR family governs how organizations manage vendors once they are in. Carved out of the SA family in Rev 5, its 12 controls cover supply chain policy, risk planning, acquisition strategies, supplier assessments, and component disposal. For a broader view, see the third-party risk management guide.
Four SR controls are central to vendor management:
- SR-2 (Supply Chain Risk Management Plan): Organizations must document how they will manage supply chain risks across the system lifecycle, from design and acquisition through disposal. The plan must be reviewed regularly and protected from unauthorized changes.
- SR-3 (Supply Chain Controls and Processes): Requires organizations to identify weaknesses in the supply chain, implement controls to address them, and document those controls in the security plan or supply chain risk management plan.
- SR-5 (Acquisition Strategies, Tools, and Methods): Organizations must use procurement methods that reduce supply chain risk, including tamper-evident packaging, trusted distribution channels, and contract terms that prohibit counterfeit or tainted components.
- SR-6 (Supplier Assessments and Reviews): Organizations must assess and review suppliers and contractors on a regular schedule, covering their security practices, any foreign ownership or influence, and how well they manage their own downstream vendors.
The following table maps key SA and SR controls to vendor management activities:
| Family | Control | Vendor Management Activity |
| SA | SA-4 | Include security requirements in vendor contracts |
| SA | SA-9 | Define and monitor external service provider requirements |
| SR | SR-2 | Develop supply chain risk management plan |
| SR | SR-3 | Establish supply chain controls and processes |
| SR | SR-5 | Define acquisition review strategies for supply chain risk |
| SR | SR-6 | Conduct supplier assessments and reviews |
These six controls follow the vendor lifecycle from acquisition through ongoing oversight:
- SA-4 locks security requirements into contracts before work begins
- SR-5 requires procurement methods that reduce supply chain risk from the start
- SA-9, SR-2, and SR-3 establish ongoing oversight, keeping external service relationships auditable, supply chain risks documented, and controls managed across the vendor lifecycle.
- SR-6 closes the loop by requiring formal assessments and reviews of suppliers on a defined schedule, confirming vendors meet their obligations.
Supply Chain Risk Management (SR Family)
The Supply Chain Risk Management (SR) family is a 12-control family in NIST 800-53 Rev 5 covering supply chain policy, planning, controls, provenance, supplier assessments, and component integrity from acquisition through disposal. New in Rev 5, the family consolidates protections previously scattered across SA-12 and related enhancements into a dedicated set running from SR-1 (Policy and Procedures) through SR-12 (Component Disposal).
Executive Order 14028 (May 2021) on Improving the Nation’s Cybersecurity elevated supply chain security as a federal priority, accelerating adoption of SR family controls. Executive Order 14117 (February 2024), implemented through the DOJ Final Rule effective April 2025, extended federal vendor management into national security by restricting bulk sensitive data transactions with vendors linked to countries of concern, reinforcing SR-2, SR-5, and SR-11.
The 12 SR controls cover the supply chain lifecycle:
| Control | Control Name | Requirement | Lifecycle Stage | Purpose | Frequency |
| SR-1 | Policy and Procedures | Establish, document, approve, and maintain a supply chain risk management policy. Assign an accountable owner and review it regularly. | Governance | Creates the foundation for consistent vendor risk management | At least annually |
| SR-2 | SCRM Plan | Develop and maintain a supply chain risk management plan covering the full system lifecycle. Protect it from unauthorized changes. | Governance / All stages | Translates policy into an actionable program | At least annually or upon major changes |
| SR-3 | SC Controls and Processes | Identify supply chain risks and implement documented controls to mitigate them in security plans or SCRM plans. | All stages | Ensures risks are actively managed, not just identified | Continuous, with periodic review |
| SR-4 | Provenance | Track and maintain origin, ownership, and change history of systems, components, and data across the lifecycle. | Design → Disposal | Enables traceability and detection of unauthorized changes | Continuous |
| SR-5 | Acquisition Strategies, Tools, and Methods | Implement secure procurement practices, including trusted suppliers, tamper-resistant packaging, and contractual safeguards. | Acquisition | Reduces risk before components enter the environment | Per procurement |
| SR-6 | Supplier Assessments and Reviews | Assess suppliers and their downstream dependencies for security practices, ownership risks, and control effectiveness. | Acquisition / Ongoing | Prevents high-risk vendors from introducing vulnerabilities | Before onboarding and periodically thereafter |
| SR-7 | SC Operations Security | Protect supply chain-related information (e.g., configurations, supplier data, requirements) from unauthorized exposure. | Operations | Limits adversary insight into systems and vendors | Continuous |
| SR-8 | Notification Agreements | Establish contractual requirements for suppliers to notify the organization of incidents, breaches, or risks in a defined timeframe. | Operations | Enables timely incident response and risk mitigation | Ongoing (enforced via contracts) |
| SR-9 | Tamper Resistance and Detection | Implement measures to prevent tampering, reverse engineering, or substitution of components during delivery and use. | Distribution / Use | Protects integrity of hardware and systems | Continuous |
| SR-10 | Inspection of Systems and Components | Conduct inspections of systems and components to detect tampering or anomalies (e.g., packaging, origin changes). | Distribution / Use | Provides verification and early detection of compromise | Random and/or scheduled |
| SR-11 | Component Authenticity | Implement anti-counterfeit processes to verify authenticity of components and report counterfeit findings. | Acquisition / Use | Prevents compromised or fake components from entering systems | Continuous |
| SR-12 | Component Disposal | Dispose of systems, components, and data using secure, defined methods to prevent reuse or exposure. | Disposal | Reduces risk of data leakage and gray market reuse | Per disposal event |
NIST SP 800-161 Rev 1 (Cybersecurity Supply Chain Risk Management Practices for Systems and Organizations) provides additional implementation guidance for the SR family controls. However, not all SR controls apply at every baseline.
How to Assess Vendors Against NIST 800-53 Controls
Assessing vendors against NIST 800-53 controls requires mapping each third party’s service scope to the specific SA and SR controls that apply, then verifying implementation through questionnaires, evidence collection, and ongoing monitoring.
For a comprehensive guide to running this process end to end, see our third-party risk assessment guide. For broader NIST 800-53 compliance requirements beyond vendor management, see the NIST 800-53 compliance guide.
Step 1: Scope the vendor relationship.
Identify which systems, data, and services the vendor touches. This determines which control families apply. SA and SR are the primary families for vendor risk, but depending on the vendor’s level of access, Access Control (AC), Audit and Accountability (AU), and System and Communications Protection (SC) may also apply.
Assess vendor criticality at this stage, scoring data sensitivity, operational dependency, and product or service delivery impact. This vendor-level scoring complements the broader NIST 800-53 risk assessment process at the system level.
Step 2: Map applicable controls.
Use FIPS 199 categorization of the data the vendor handles to determine whether Low, Moderate, or High baseline controls apply. A vendor handling Moderate-impact data must be assessed against Moderate baseline controls. Most SR controls apply at the Low baseline, except for SR-6, which is required at Moderate and High.
For a comprehensive approach, see our third-party risk assessment guide.
Step 3: Assess implementation.
Distribute control-specific questionnaires to vendors, collect implementation evidence, and review the vendor’s existing compliance certifications, such as FedRAMP authorization, SOC 2 reports, HECVAT v4 responses (the EDUCAUSE-maintained vendor assessment standard for higher education), or ISO 27001 certification. The CISA / ICT SCRM Task Force Software Acquisition Guide for Government Enterprise Consumers provides additional vendor attestation, SBOM, and lifecycle assurance criteria for federal software acquisitions, mapped to SR-3, SR-4, SR-5, and SR-6.
SR-6 (Supplier Assessments and Reviews) is the primary control here, requiring organizations to assess and review supply chain risks tied to suppliers and the systems or services they provide. SA-9 supports this by requiring ongoing monitoring of external service providers. FedRAMP authorization can serve as a shortcut for cloud service providers, as FedRAMP baselines map to NIST 800-53; the FedRAMP Continuous Monitoring Playbook (Rev 5) sets the annual independent assessment, third-party service oversight, and incident reporting expectations CSPs must meet against SA-9 and the SR family.
For Department of Defense contractors, 32 CFR Part 170 (the CMMC Final Rule), effective December 2024, requires third-party certification of NIST 800-171 controls (which trace back to NIST 800-53 SA/SR) across the DoD supply chain, with subcontract flowdown that mirrors SR-3 (see CMMC vs NIST 800-53). For a deeper look at internal control assessments at the organizational level, see the NIST 800-53 assessment guide.
Step 4: Risk-rate and document.
Score assessment findings against a risk matrix, document gaps, and create remediation plans.
At this stage, it is also worth checking whether the organization has correctly implemented its own SA and SR controls, such as whether SR-6 is documented and followed, or whether SA-9 oversight responsibilities are properly assigned. NIST SP 800-53A Rev 5 (Assessing Security and Privacy Controls) provides the formal procedures for doing that.
This is an internal check on the organization’s compliance program, not a substitute for the vendor-facing assessments that SR-6 and SA-9 require.
Building a Vendor Compliance Program
Building a NIST 800-53 vendor compliance program requires four elements: a documented supply chain risk management policy, risk-based vendor tiering, a defined assessment cadence per tier, and continuous monitoring between formal reviews. Individual vendor assessments are a starting point; without those structures, gaps accumulate over time. A mature NIST 800-53 vendor management practice depends on all four working together.
Documented SCRM Policy
Every vendor compliance program starts with SR-1 (Policy and Procedures), which requires organizations to establish and maintain a formal supply chain risk management policy. This policy sets the rules for everything that follows: who owns vendor risk, how vendors are classified, what assessment requirements apply by tier, what constitutes acceptable risk, and how exceptions and escalations are handled. Without it, vendor assessments are ad hoc and audit evidence is inconsistent. NISTIR 8276 (Key Practices in Cyber Supply Chain Risk Management) distills eight foundational practices and 24 recommendations for implementing SR-1 and SR-2 at the program level.
Vendor Tiering Based on Risk
Vendor tiering classifies vendors by risk so assessment effort is proportional to the threat each one represents, based on data access, system integration depth, and business criticality. Not all vendors carry the same risk, and a tiered model focuses assessment resources where they matter most. A common NIST 800-53 vendor program uses four tiers:
| Vendor Tier | Description | Business Impact (If Compromised) | Frequency |
| Low | Vendors with no data access and minimal integration | Minimal to no operational or data impact | Periodic review with self-attestation |
| Moderate | Vendors with limited access or low integration | Minor operational impact, low likelihood of sensitive data exposure | Every 2-3 years |
| High | Vendors with moderate data access or integration | Limited service disruption, potential exposure of internal or customer data, moderate compliance risk | Every 18-24 months |
| Critical | Vendors with direct access to sensitive systems or data, or essential to operations | Major operational disruption, sensitive data breach, regulatory exposure, significant financial/reputational damage | Annual (or more frequent) |
Assessment Cadence Based on Vendor Tier
SR-6 (Supplier Assessments and Reviews) requires formal assessments on a defined schedule that reflects vendor risk tier. Document that cadence in the supply chain risk management plan required by SR-2 so it is auditable and consistently enforced.
Continuous Monitoring
Continuous monitoring is the ongoing tracking of vendor security posture, incident reports, and compliance status between formal assessment cycles, required by both SR-3 (Supply Chain Controls and Processes) and SA-9 (External System Services). Risk does not wait for the next scheduled review, so these workflows catch changes as they happen and keep vendor risk visible between formal NIST 800-53 audit cycles.
For additional approaches, see our guides to building a TPRM program and the VRM program guide.
Integration with Broader GRC
The vendor compliance program should feed into the organization’s Risk Management Framework (RMF) process. Vendor risks should be documented in organizational risk registers and reflected in the System Security Plan (SSP) and Plan of Action and Milestones (POA&M). ISO 27036 and NIST 800-161 provide additional vendor management framework references.
Sector overlays extend SA-9 and SR-6 obligations beyond the federal baseline. Banks and credit unions follow the Interagency Guidance on Third-Party Relationships: Risk Management (FDIC FIL-29-2023, FRB SR 23-4, OCC Bulletin 2023-17), which replaced prior agency-specific guidance with a unified third-party lifecycle framework.
Healthcare entities should track the HHS OCR HIPAA Security Rule NPRM (December 2024), which would require annual written verification of business associate technical safeguards. Public companies face SEC Regulation S-K Item 106(b), which requires annual disclosure of processes for overseeing third-party cybersecurity risk.
How to Simplify NIST 800-53 Vendor Management
Isora GRC by SaltyCloud simplifies NIST 800-53 vendor management by giving security teams one shared workspace to centralize vendor inventories, run SA and SR-aligned assessments, and track vendor risks end to end. As the collaborative GRC Assessment Platform™, it replaces the spreadsheets and inboxes that break down once a vendor portfolio grows, where SR-6 reviews and SA-9 monitoring become inconsistent and hard to evidence at audit time.
Inventory Management
Centralize vendors, assets, and applications in one connected inventory, with deployment tracking, owning units, and data classifications on every record. Vendor records link directly to assessments, exceptions, and risks, supporting SA-4 scoping and the relationship visibility that SR-6 reviews require. The result is reduced time spent reconciling vendor data across spreadsheets and a single live source for third-party oversight.
Assessment Management
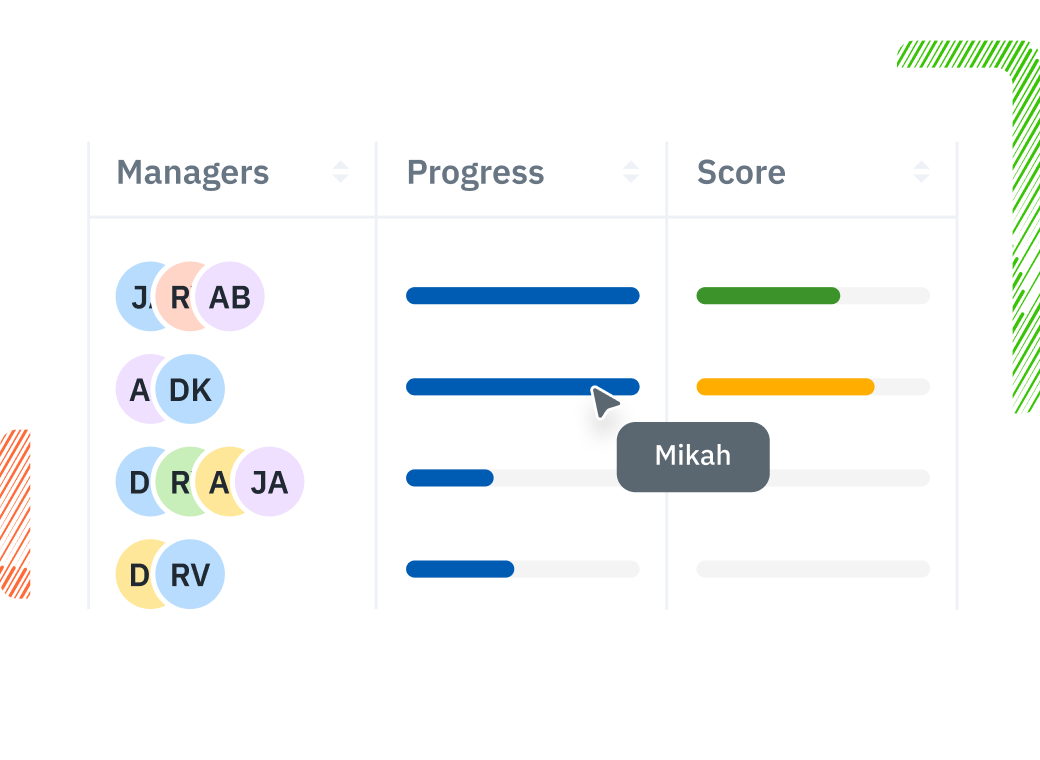
Organize vendor assessments by SA or SR compliance goal and track them from a centralized dashboard with live progress, deadline reminders, and per-vendor scoring. Customizable questionnaires mapped to NIST 800-53 controls let teams adjust assessment depth by vendor risk tier and route findings through evidence collection and approval. Multiple contributors can collaborate inside a single assessment, streamlining the SR-6 supplier review cycle.
Risk Management
Publish risks directly from vendor assessment findings into a connected risk register, with assigned owners, deadlines, and remediation tracking. Each risk record links back to the vendor, the underlying assessment, and any related exceptions, keeping SA-9 and SR-3 monitoring auditable between formal review cycles. Audit-ready scorecards and PDF or CSV exports support SSP, POA&M, and SR-6 documentation without manual reformatting.
Streamline NIST 800-53 third-party risk with Isora GRC’s NIST 800-53 compliance software or explore the dedicated vendor risk management software. For a broader look at platforms that support NIST 800-53 implementation, see NIST 800-53 tools and solutions.
Key Takeaways
NIST 800-53 addresses vendor risk through two dedicated control families: System and Services Acquisition (SA) with 16 controls governing how organizations procure systems and services, and Supply Chain Risk Management (SR) with 12 controls governing how organizations manage supply chain risk after acquisition. SA-9 (External System Services) and SR-6 (Supplier Assessments and Reviews) are the anchor controls for vendor management.
A mature program builds outward from those anchors with a documented SCRM policy (SR-1), a tiered vendor model, defined assessment cadences, and continuous monitoring. Assessment cadence is the mechanism that keeps vendor risk visible, documented, and auditable between formal review cycles. For a broader view, see the third-party risk management guide and the NIST 800-53 complete guide.
Streamline your NIST 800-53 vendor management with Isora GRC NIST 800-53 compliance software.
NIST 800-53 Vendor Management FAQs
What NIST 800-53 controls apply to vendor management?
The two control families for NIST 800-53 vendor management are System and Services Acquisition (SA) with 16 controls and Supply Chain Risk Management (SR) with 12 controls. Key individual controls include SA-4 (Acquisition Process), SA-9 (External System Services), SR-5 (Acquisition Strategies), and SR-6 (Supplier Assessments and Reviews).
Is the SR family new in NIST 800-53 Rev 5?
Yes. The Supply Chain Risk Management (SR) family was introduced in NIST 800-53 Rev 5 as a standalone family with 12 controls, carved out of SA-12 in Rev 4 to give supply chain risk dedicated policy, assessment, and monitoring requirements. For what changed in Rev 5, see the NIST 800-53 Rev 4 vs Rev 5 guide.
How do you assess a vendor against NIST 800-53?
Assess a vendor against NIST 800-53 by first reviewing their existing attestation reports, such as FedRAMPauthorizations, SOC 2 reports, or ISO 27001 certifications, then layering targeted questionnaires for critical vendors focused on the SA and SR controls most relevant to their service scope. Most organizations do not assess vendors against all of NIST 800-53; full baseline assessments are reserved for the highest-risk relationships.
Does NIST 800-53 require continuous vendor monitoring?
Yes. Controls SA-9 and SR-3 require ongoing monitoring of external service providers and supply chain processes. Organizations must establish processes for monitoring vendor compliance on a recurring basis and responding to changes in vendor security posture.
What is the difference between the SA and SR families for vendor risk?
SA governs how vendors enter the environment, covering vendor selection, contract requirements, and developer security. SR governs ongoing supply chain risk management once vendors are in, including supplier assessments, monitoring, and component integrity. The families overlap in places. SA-5 (Acquisition Strategies, Tools, and Methods), for example, addresses acquisition rules that also fall within the SR family scope.
How many SR controls are in the Moderate baseline?
The Moderate baseline includes SR-1, SR-2, SR-3, SR-5, SR-6, SR-8, SR-10, SR-11, and SR-12, for 9 SR controls in total. These provide the core supply chain risk management capabilities most organizations need, covering policy, planning, controls, acquisition strategies, supplier assessments, notification agreements, component authenticity, and disposal.
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.


















