-
Product Capabilities
-
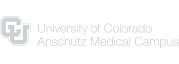
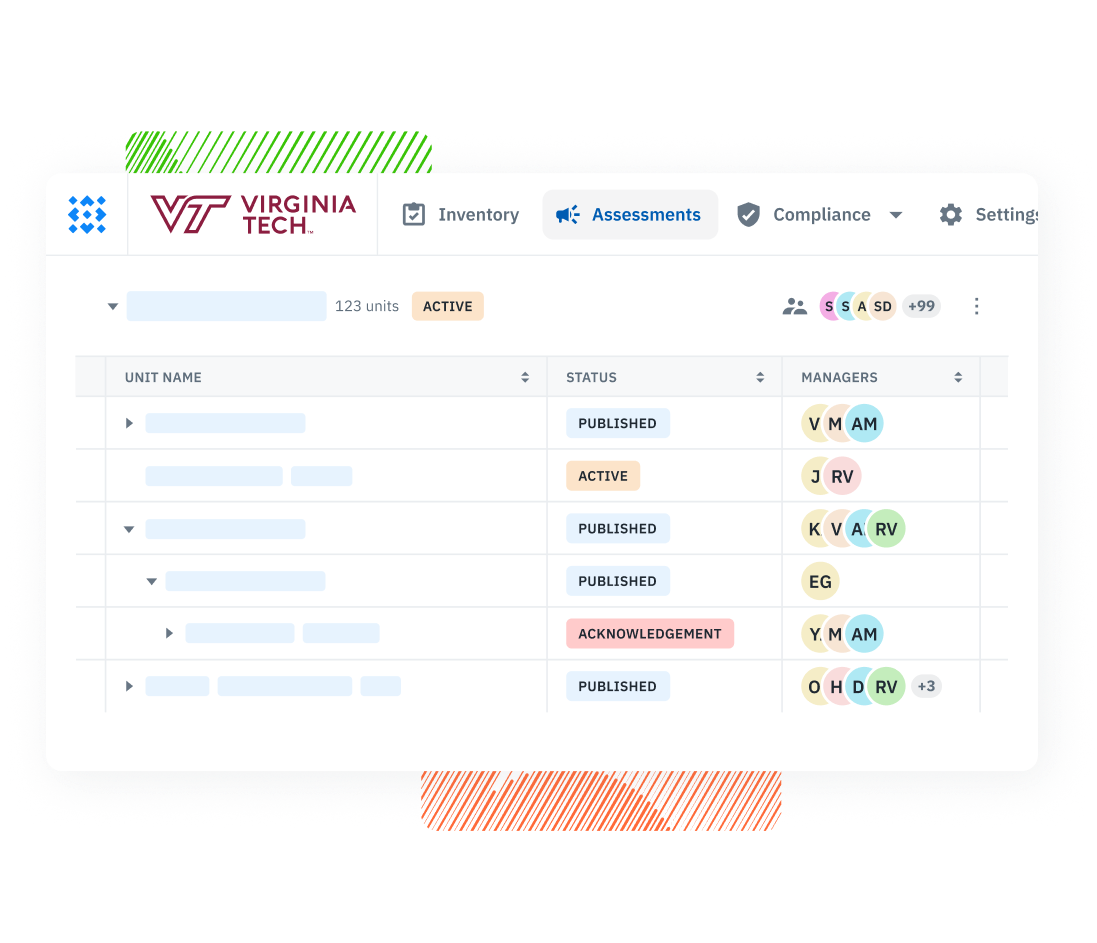
Assessment Management Run structured security assessments across systems, teams, and vendors—all from one place.
-
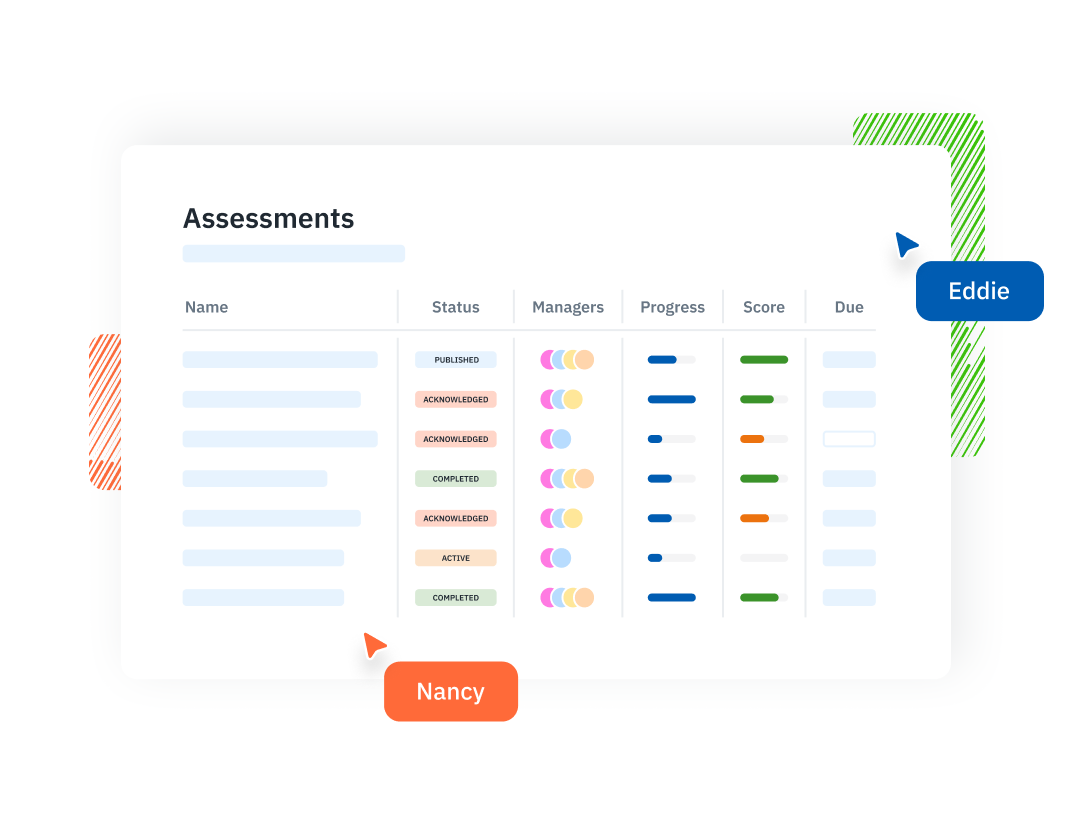
Questionnaires & Surveys Launch structured questionnaires and collect evidence from the people closest to each control.
-
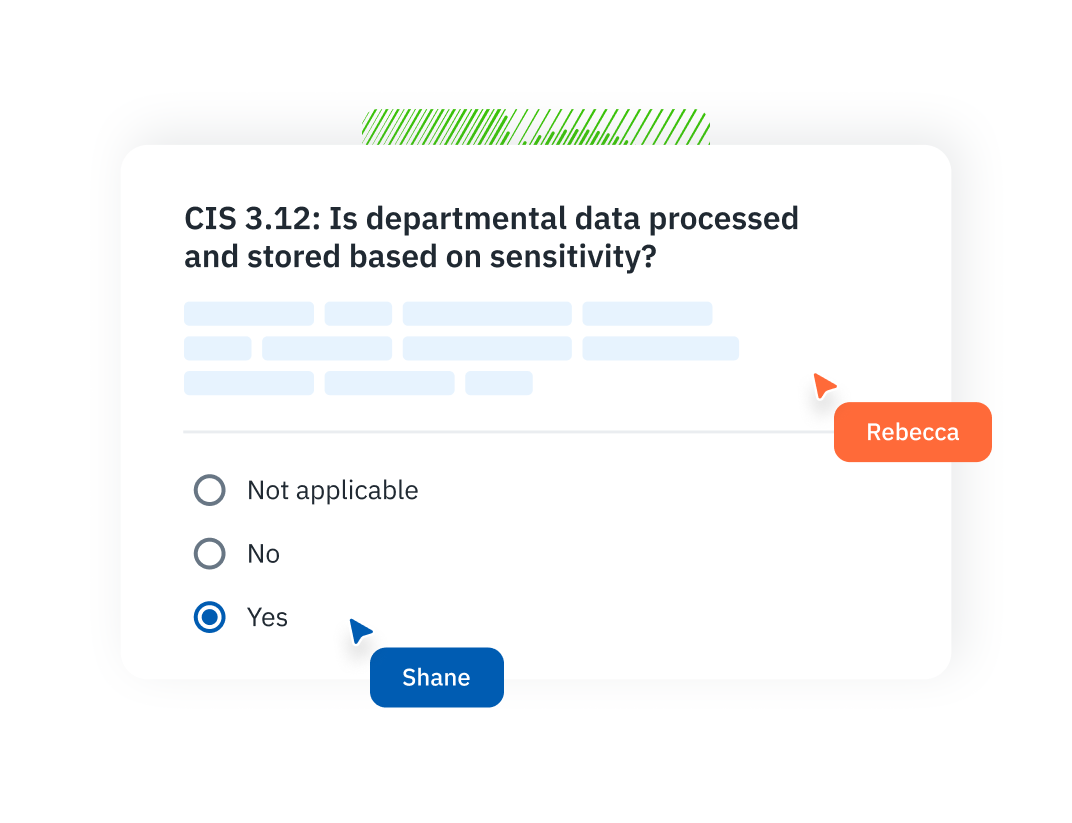
Reports & Scorecards Turn assessments into audit-ready reports and actionable insights your team can actually use.
-
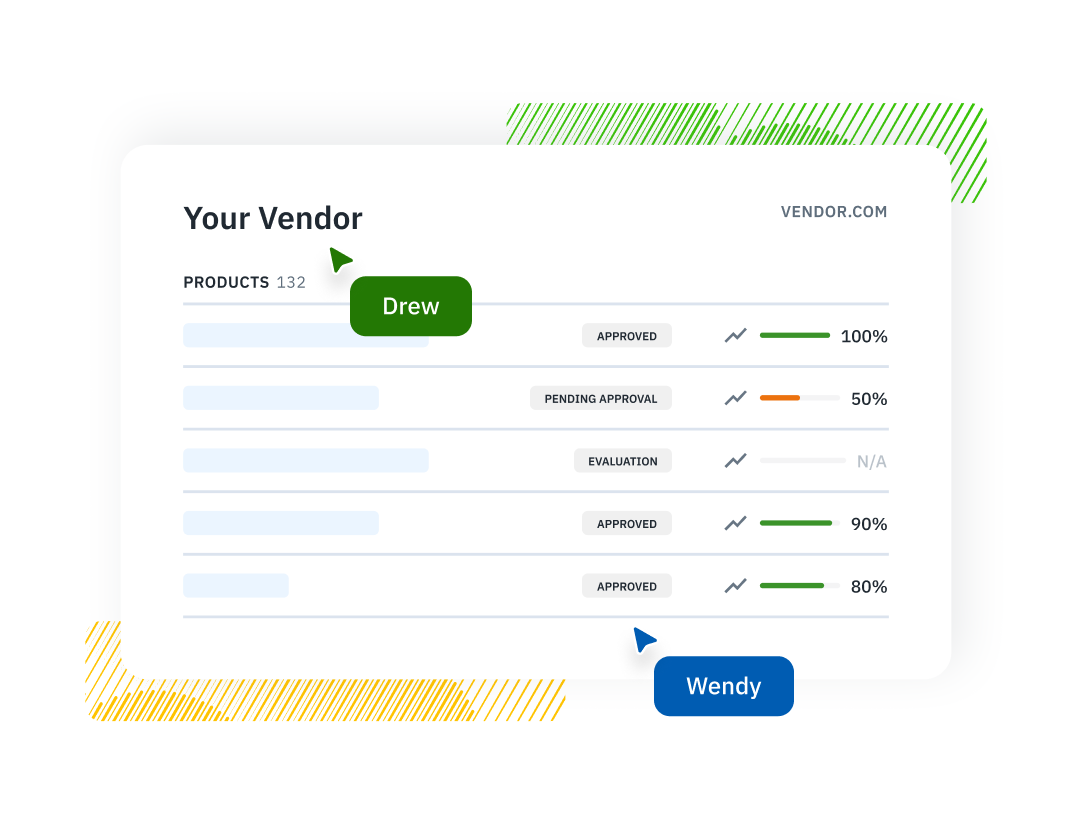
Inventory Management Maintain a connected inventory of vendors, assets, and systems linked to assessments and risks.
-
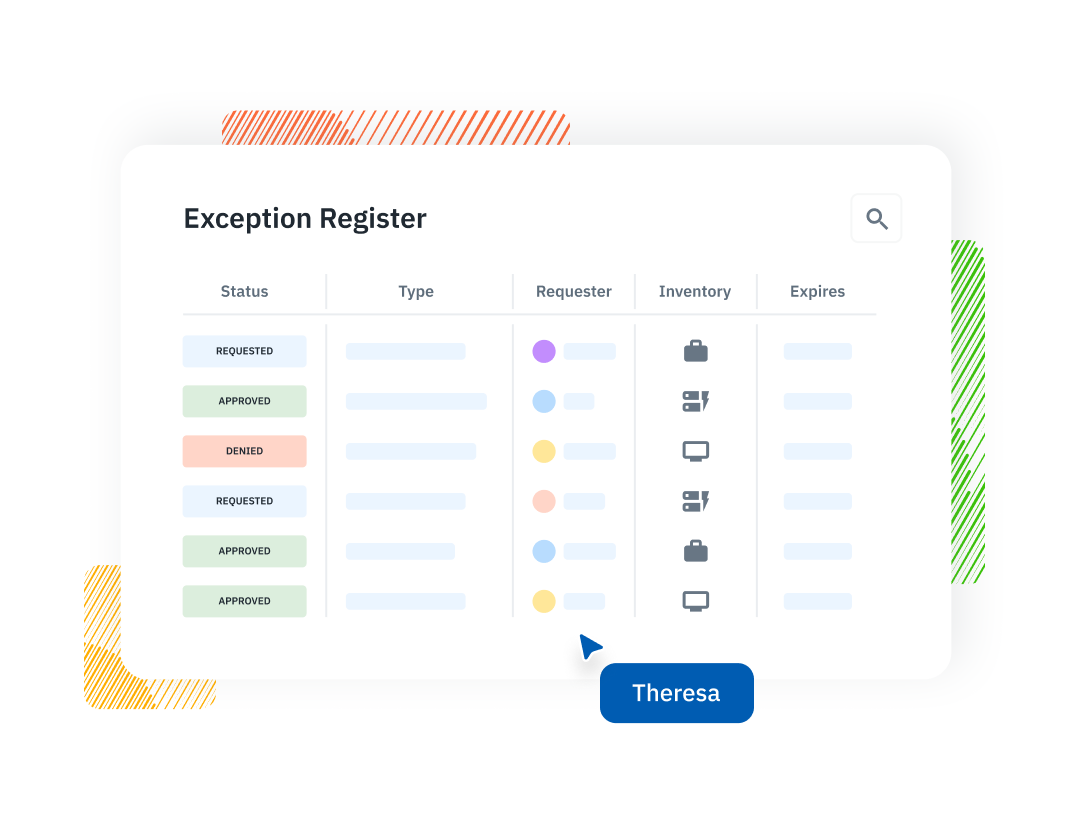
Exception Management Log, track, and resolve policy exceptions so nothing falls through the cracks during audits.
-
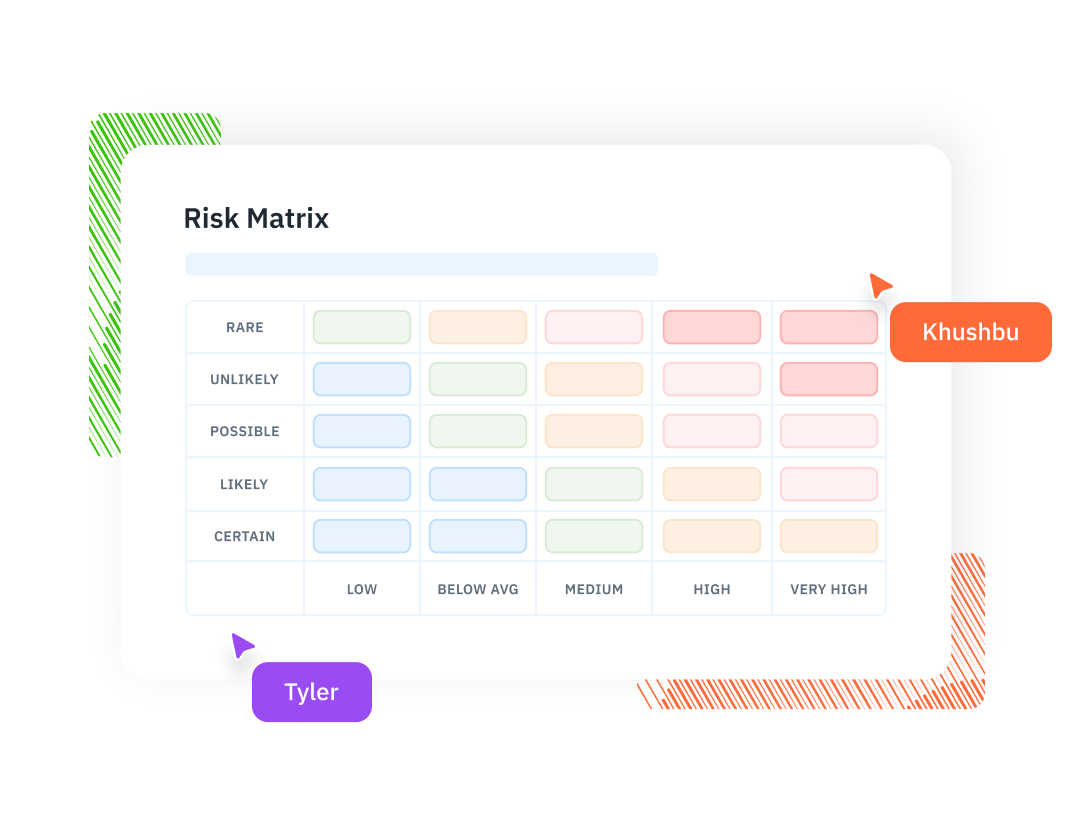
Risk Management Turn assessment findings into a living risk register with owners, remediation plans, and full lineage.
Use Cases-
Information Security Risk Management (ISRM) Run assessments across units and systems, maintain IT asset inventories, and collaborate on a shared risk register—all in one place.
-
Third-Party Security Risk Management (TPSRM) Track vendors, send security questionnaires, and manage third-party risk with built-in workflows and a centralized inventory.
This guide contains everything you need to know about conducting an information security risk assessment questionnaire at your organization.
-
-
Solutions FrameworksIndustries
-
Insights Latest ContentLatest ContentLatest content
- Customer Stories