 Table of Contents
Table of Contents
- CMMC vs NIST 800-53: Key Differences for Defense Contractors
- CMMC Maturity Levels and the 800-53/800-171 Relationship
- Key Differences in Approach and Scope
- CMMC vs NIST 800-53: Side-by-Side Comparison Table
- If You Need CMMC, You Need to Understand NIST 800-53
- How Isora GRC Simplifies CMMC and NIST 800-53 Compliance
- Key Takeaways
- CMMC vs NIST 800-53 FAQs
CMMC vs NIST 800-53: Key Differences for Defense Contractors
The Cybersecurity Maturity Model Certification (CMMC) and NIST Special Publication 800-53 Revision 5 are both central to federal cybersecurity, but they serve different functions in the compliance landscape.
- CMMC is a DoD-specific certification program that defense contractors must achieve to win and retain contracts. It prescribes a fixed set of security practices across three maturity levels, each tied to the type of information a contractor handles.
- NIST 800-53 is a comprehensive catalog of 1,196 security and privacy controls that federal agencies use to secure their information systems. It is the foundational source from which CMMC’s required controls are derived, particularly at Levels 2 and 3.
Defense contractors handling Federal Contract Information (FCI) or Controlled Unclassified Information (CUI) must achieve a specific CMMC level, while NIST 800-53 applies to all federal information systems. For contractors evaluating both: CMMC defines what contractors must certify to. NIST 800-53 defines where those requirements come from.
This comparison is part of our NIST 800-53 framework comparisons resource. It covers the derivation chain from 800-53 to CMMC, key differences in scope and certification approach, and what defense contractors need to know about both frameworks.
CMMC Maturity Levels and the 800-53/800-171 Relationship
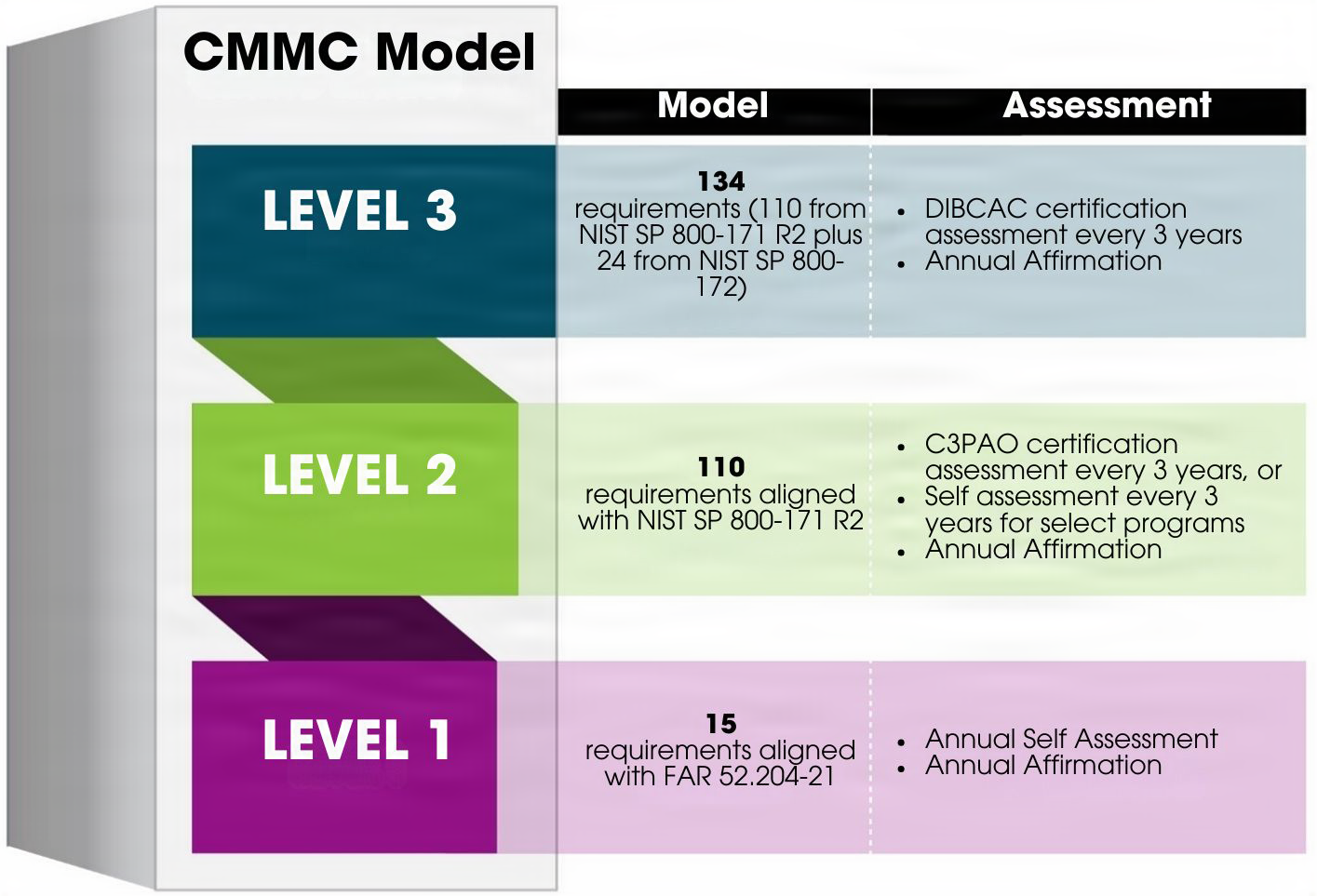
CMMC organizes its requirements across three maturity levels. Level 1 covers basic safeguarding practices and protects Federal Contract Information (FCI). Levels 2 and 3 protect Controlled Unclassified Information (CUI) and require progressively more rigorous controls and assessment types.
Note: Proposed FAR changes may rename Federal Contract Information (FCI) to Covered Federal Information (CFI). This article uses FCI to refer to non-public information provided by or generated for the government under a contract.
For a complete overview of CMMC requirements, certification levels, and implementation steps, see our complete CMMC guide.
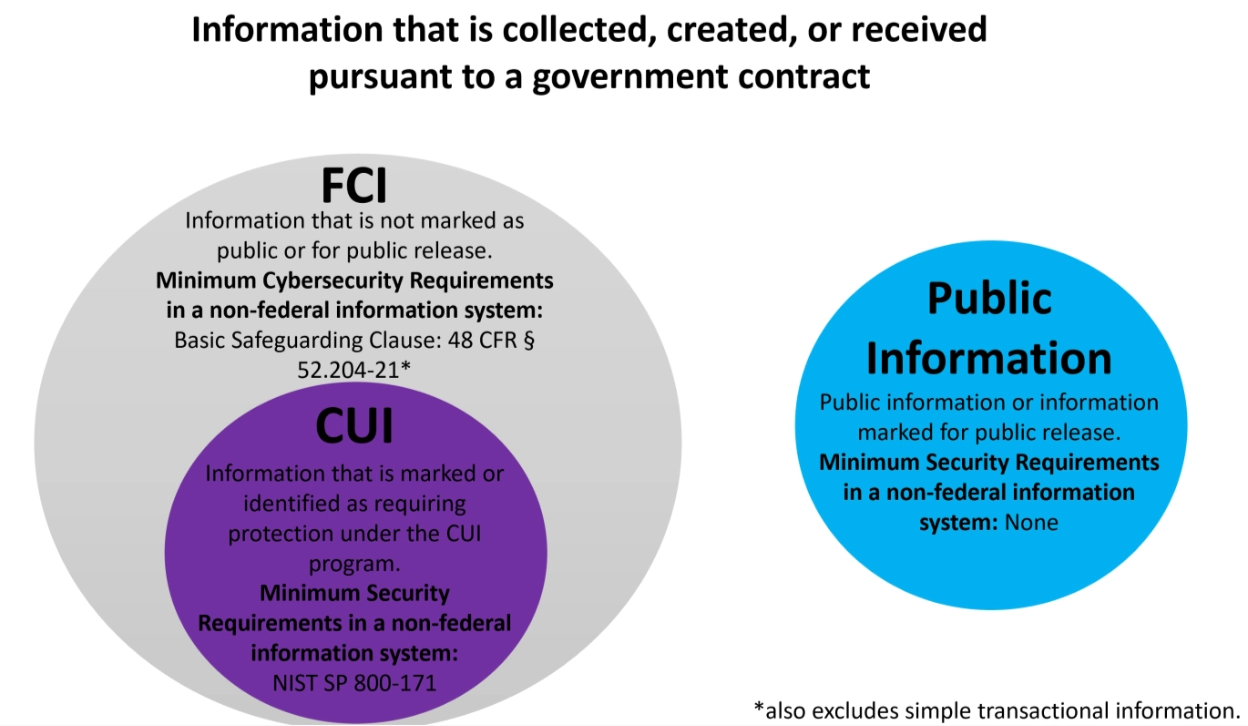
FCI and CUI, what is the difference? CUI Program Blog, National Archives
How CMMC Relates to NIST 800-53
CMMC Levels 2 and 3 directly draw from different NIST publications, all of which trace back to NIST 800-53 as the source catalog.
NIST 800-53 contains 1,196 controls organized into 20 families. From that master catalog, NIST selected 110 controls relevant to protecting Controlled Unclassified Information (CUI), adapted them for DoD-related environments, and published them as NIST SP 800-171. The control language was adjusted to better reflect CUI protection requirements. CMMC Level 2 maps directly to those 110 NIST 800-171 requirements. CMMC Level 3 goes further, adding requirements from NIST 800-172, beyond what 800-171 covers.
CMMC (Cybersecurity Maturity Model Certification) 2.0 is a DoD-specific cybersecurity certification program with three maturity levels required for defense contractors. NIST 800-53 Rev 5 is a comprehensive federal catalog of 1,196 security and privacy controls across 20 families. CMMC is rooted in 800-53: Level 2 draws from NIST 800-171, and Level 3 draws from both NIST 800-171 and NIST 800-172.
For a detailed comparison of 800-53 and 800-171, see our NIST 800-53 vs 800-171 comparison. For guidance on scoping CUI and FCI for CMMC, see our dedicated guide.
How Each CMMC Level Maps to NIST Standards
- CMMC Level 1: Covers 15 basic safeguarding requirements from Federal Acquisition Regulation (FAR) 52.204-21 to protect FCI and requires an annual self-assessment. These requirements apply to all federal contractors. FAR 52.204-21 shares common security themes with NIST 800-53 but has no direct connection.
- CMMC Level 2: Covers 110 security requirements aligned to NIST 800-171 Rev 2, which was derived from NIST 800-53. It protects CUI and requires a third-party assessment by a Certified Third-Party Assessment Organization (C3PAO) every three years. NIST has since published 800-171 Rev 3, but CMMC currently remains aligned with Rev 2. Contractors should begin preparing for future updates.
- CMMC Level 3: Covers 134 requirements. It builds on the full 800-171 Rev 2 control set and adds 24 requirements from NIST 800-172, a dedicated publication designed to protect high-value CUI against advanced persistent threats. Level 3 requires a government-led assessment by the Defense Industrial Base Cybersecurity Assessment Center (DIBCAC) every three years.
Overview of the CMMC Program, Department of War Chief Information Officer (DoW CIO)
Key Takeaway: NIST 800-53 is the source catalog. NIST 800-171 is a CUI-specific subset. CMMC Level 2 wraps 800-171 into an assessable, certifiable framework. Level 3 extends that further with 800-172.
For a broader view of NIST 800-53 and how its control families work, see our NIST 800-53 complete guide. You can also review the NIST 800-171 basic assessment guide for assessment-specific guidance.
Key Differences in Approach and Scope
CMMC and NIST 800-53 differ in scope, certification approach, and intended audience.
- CMMC is narrow and prescriptive, designed to certify DoD contractors.
- NIST 800-53 is broad and adaptable, designed as the master control catalog for all federal and federal-adjacent systems.
Scope. CMMC applies only to DoD contractors in the Defense Industrial Base (DIB). NIST 800-53 applies to all federal information systems, organizations pursuing FedRAMP authorization, and those adopting it voluntarily as a security baseline.
Certification. CMMC is certifiable. Level 2 requires third-party assessment by a C3PAO, and Level 3 requires a government-led assessment by DIBCAC. NIST 800-53 has no direct certification. Instead, organizations receive an authorization to operate through the Risk Management Framework (RMF) process. CMMC certification confirms a contractor meets a defined maturity level, while NIST 800-53 authorization confirms a system’s risks are understood and accepted.
Control selection. CMMC prescribes a fixed set of controls per maturity level. Contractors must implement all required practices for their level, with no tailoring permitted at Level 1 or Level 2. NIST 800-53 follows a similar logic for federal systems, with controls selected based on system impact level: Low (149 baseline controls), Moderate (287 baseline controls), or High (370 baseline controls). The key difference is that non-federal organizations can voluntarily adopt and tailor 800-53 controls to fit their environment. CMMC offers no such flexibility, as compliance is assessed against a fixed standard.
Maturity model. CMMC introduces maturity levels that assess both control implementation and process maturity. NIST 800-53 does not include maturity levels. It focuses purely on control selection and implementation. For a comprehensive overview of CMMC requirements, see our complete CMMC guide.
CMMC vs NIST 800-53: Side-by-Side Comparison Table
The following table summarizes the key differences between CMMC and NIST 800-53 across purpose, scope, certification, and control structure.
| Attribute | CMMC 2.0 | NIST 800-53 Rev 5 |
|---|---|---|
| Purpose | DoD contractor cybersecurity certification | Comprehensive federal security and privacy control catalog |
| Scope | Defense Industrial Base (DIB) contractors only | All federal information systems; voluntary for others |
| Number of Controls | Level 1: 15 Level 2: 110 Level 3: 134 |
1,196 controls across 20 families |
| Certifiable? | Yes. Third-party (Level 2) or government-led (Level 3) assessment | No direct certification. Authorization to operate via RMF process. Authority to Operate (ATO) via FedRAMP |
| Required For | DoD contractors handling FCI/CUI | Federal agencies under FISMA; FedRAMP cloud service providers |
| Maturity Levels | Three levels | None. Uses impact-based baselines (Low, Moderate, High) |
| Assessment Type | Self (L1), C3PAO (L2), DIBCAC (L3) | Agency self-assessment or independent assessor via RMF; third-party assessment (3PAO) for FedRAMP authorization |
| Relationship | Draws controls FROM 800-53 (via 800-171 and 800-172) | Source catalog for NIST 800-171 and 800-172 controls |
If You Need CMMC, You Need to Understand NIST 800-53
Defense contractors pursuing CMMC certification at Levels 2 and 3 benefit from understanding NIST 800-53 because CMMC controls trace back to it. Although contractors implement controls through NIST 800-171 and 800-172, the original control language and implementation guidance come from NIST 800-53.
The table below identifies the key NIST publications relevant to each CMMC certification scenario and what contractors should focus on during implementation.
| Scenario | Relevant Publication | What It Is | How It Helps | What to Pay Attention To |
|---|---|---|---|---|
| CMMC understanding | NIST SP 800-53 Rev 5 Moderate Baseline | Security control baseline for federal systems handling moderate impact data | Shows how NIST selected the controls that later became 800-171 requirements | Control intent, baseline tailoring, and requirement derivation |
| CMMC implementation | NIST SP 800-53 Rev 5 | Comprehensive catalog of federal security and privacy controls | Provides the original control language and guidance behind CMMC-derived requirements | Control descriptions, supplemental guidance, and control enhancements |
| Program rules and certification | 32 CFR Part 170 (CMMC Final Rule) | DoD regulation establishing the CMMC program | Explains how certification works and when it applies to DoD contracts | Certification scope, assessment structure, and C3PAO requirements |
| Level 1 compliance | FAR 52.204-21 | 15 basic safeguarding requirements for protecting FCI | Defines the baseline practices contractors must implement for Level 1 annual self-assessment | FCI scoping, annual self-assessment procedures, and basic safeguarding requirements |
| Level 2 preparation | NIST SP 800-171 Rev 2 | 110 security requirements across 14 control families protecting CUI | Helps contractors implement controls with proper context and depth | CUI system scoping, requirement implementation, and supporting policies |
| Assessment preparation | NIST SP 800-171A | Assessment procedures for each 800-171 requirement | Shows how auditors verify control implementation during assessments | Assessment objectives, evidence expectations, and testing methods |
| Level 3 requirement | NIST SP 800-172 | Enhanced security requirements for protecting CUI from advanced threats | Identifies additional protections required for CMMC Level 3 environments | Advanced monitoring, threat detection, and enhanced incident response |
| Future proofing | NIST 800-53, 800-171, and 800-172 | Three core NIST publications used in the CMMC ecosystem | Helps contractors anticipate future CMMC updates as NIST revises these standards | New revisions, changes to control language, newly derived requirements, and alignment between the three publications |
Universities with DoD-funded research face a unique challenge: they must meet CMMC requirements for systems handling CUI while potentially managing broader 800-53 compliance across the institution. Understanding the 800-53 foundation helps scope these obligations accurately. For higher education CMMC guidance, see our CMMC compliance for higher education guide.
How Isora GRC Simplifies CMMC and NIST 800-53 Compliance
Defense contractors managing both CMMC certification and NIST 800-53 compliance face overlapping assessment requirements across multiple frameworks. Isora GRC provides one shared workspace to streamline compliance across the 800-53 to 800-171 to CMMC derivation chain.
Assessment Management
Organize assessments by compliance goal — whether tracking CMMC maturity level requirements or NIST 800-53 control implementation — and monitor progress across departments from a single dashboard. Assessment grouping by series allows defense contractors to separate CMMC Level 2 campaigns from broader 800-53 assessments while maintaining visibility into both.
Questionnaires & Surveys
Distribute framework-aligned questionnaires to unit owners and track completion in real time. Isora includes prebuilt questionnaires for NIST 800-53, NIST 800-171, and other frameworks, reducing the time defense contractors spend building and managing assessments across multiple standards.
Reports & Scorecards
Automated scoring and category comparisons free up time for strategic remediation instead of manual reporting. Defense contractors can drill down from summary scores to individual responses, identifying compliance gaps before formal C3PAO or DIBCAC assessment.
Explore NIST 800-53 compliance software and CMMC compliance software to see how Isora GRC supports defense contractors managing both frameworks, or request a demo to see Isora in action.
Key Takeaways
CMMC and NIST 800-53 are not competing frameworks. CMMC is a DoD certification program built on controls derived from 800-53. Level 2 implements controls through NIST 800-171, and Level 3 extends them through NIST 800-172. Both trace back to 800-53 as the source catalog.
CMMC is certifiable through formal third-party or government-led assessment. NIST 800-53 has no direct certification pathway — organizations receive authorization through the RMF process or an Authority to Operate via FedRAMP. Defense contractors benefit from understanding 800-53 because it provides the original control language and implementation guidance behind every CMMC requirement.
CMMC phased implementation began November 10, 2025. Full implementation is expected by November 10, 2028, when all applicable DoD contracts will require certification as a condition of award. Start by understanding the derivation chain from 800-53 to 800-171 to CMMC, then identify which controls apply at the target maturity level. From there, use NIST 800-53’s supplemental guidance to inform implementation depth beyond what 800-171 prescribes.
Explore more NIST 800-53 framework comparisons in our comparison guide, or see how Isora GRC helps defense contractors manage CMMC and NIST 800-53 compliance in one place.
CMMC vs NIST 800-53 FAQs
What is the difference between CMMC and NIST 800-53?
CMMC is a DoD-specific cybersecurity certification program with three maturity levels required for defense contractors. NIST 800-53 is a comprehensive catalog of 1,196 security and privacy controls used across all federal agencies. CMMC draws its controls from 800-53 (via 800-171 and 800-172), and adds a certifiable assessment framework on top.
Does CMMC replace NIST 800-53?
No. CMMC does not replace NIST 800-53. CMMC is built on controls derived from 800-53. NIST 800-53 remains the master control catalog for federal information systems, while CMMC specifically certifies DoD contractors. Organizations may need to comply with both depending on their contracts.
What CMMC level requires NIST 800-53 controls?
Both Level 2 and Level 3 are informed by NIST 800-53, but through dedicated publications. Level 2 aligns to NIST 800-171‘s 110 controls, which were derived from 800-53 and adapted for CUI and DoD contractor environments. Level 3 builds on 800-171 and adds requirements from NIST 800-172, which also draws from 800-53. Level 1 covers 15 basic safeguarding practices from FAR 52.204-21.
Do DoD contractors need NIST 800-53?
DoD contractors need CMMC, which draws its controls from NIST 800-53 through NIST 800-171 (Level 2) and NIST 800-172 (Level 3). Understanding the source catalog helps contractors implement requirements with proper context and depth.
How does CMMC relate to NIST 800-171?
CMMC Level 2 directly aligns to NIST 800-171’s 110 security requirements, which were derived from NIST 800-53’s moderate baseline. CMMC wraps 800-171 into a certifiable framework with third-party assessment requirements. Level 3 extends beyond 800-171 by adding controls from 800-172.
Is CMMC mandatory?
Yes. CMMC is mandatory for DoD contractors handling Federal Contract Information (FCI) or Controlled Unclassified Information (CUI). The CMMC Final Rule (32 CFR Part 170) became effective in December 2024, with phased implementation beginning November 10, 2025. CMMC requirements will be phased into DoD contracts, with full implementation expected by 2028.
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.
Dive into our research-backed resources–from product one pagers and whitepapers, to webinars and more–and unlock the transformative potential of powerfully simple GRC.
Learn More


















 Other Relevant Content
Other Relevant Content