 Table of Contents
Table of Contents
- NIST 800-53 Audit: What It Involves and How to Prepare
- What Is a NIST 800-53 Audit?
- NIST 800-53 Audit Types
- The AU (Audit and Accountability) Control Family
- How to Prepare for a NIST 800-53 Audit
- Audit Tools and Automation
- Key Takeaways
-
NIST 800-53 Audit FAQs
- What is a NIST 800-53 audit?
- How do you prepare for a NIST 800-53 audit?
- What are the AU family controls in NIST 800-53?
- Is a NIST 800-53 audit mandatory?
- How often are NIST 800-53 audits conducted?
- What is the difference between a NIST 800-53 audit and a NIST 800-53 assessment?
- What is a Security Assessment Report (SAR)?
- What happens after a NIST 800-53 audit?
NIST 800-53 Audit: What It Involves and How to Prepare
A NIST 800-53 audit is the systematic evaluation of whether an organization’s NIST SP 800-53 Rev 5 security and privacy controls are implemented properly, operating as intended, and producing the desired security outcomes. By reviewing documented control implementation and testing it against real-world evidence, organizations can determine whether NIST 800-53 requirements are met and where gaps still exist.
This guide covers the two types of NIST 800-53 audits (internal and independent), the AU (Audit and Accountability) control family, a step-by-step preparation guide, and the tools that simplify audit readiness. This guide is part of our NIST 800-53 compliance series, which covers the full 800-53 compliance process from baseline selection through continuous monitoring.
What Is a NIST 800-53 Audit?
A NIST 800-53 audit evaluates whether an organization’s security and privacy controls are effective. Today, NIST 800-53 audits apply to federal agencies under the Federal Information Security Modernization Act (FISMA), cloud service providers pursuing Federal Risk and Authorization Management Program (FedRAMP) authorization, and any other organizations using NIST 800-53 as its control framework.
NIST SP 800-53 Rev 5 audits are the systematic review of an organization’s security and privacy controls to determine whether they are properly implemented, operating as intended, and producing the desired security outcomes. The goal of an 800-53 audit is to assess how effectively the organization is meeting its requirements for security and privacy controls.
NIST 800-53 audits are conducted internally by the organization’s own security team for ongoing compliance monitoring and audit preparation, or independently by a qualified third-party assessor issuing formal authorization decisions such as an ATO or FedRAMP. Under FISMA, federal agencies must undergo both types.
NIST 800-53 Audit Types
NIST 800-53 audits fall into two categories: internal audits conducted by the organization’s own team, and independent audits performed by external assessors. Both evaluate the same controls, but each serve a different purpose in NIST SP 800-37’s Risk Management Framework (RMF), the structured process for managing security and privacy risk across the system lifecycle.
Internal Audits
Internal audits, sometimes called self-assessments, are conducted by the organization’s own security team or internal audit function. They often incorporate self-assessment methods, including questionnaires, documentation reviews, and evidence collection.
Their primary purpose is continuous monitoring: identifying control gaps, tracking remediation progress, and maintaining audit readiness between formal evaluations. Within the RMF, internal audits map to Step 5 (Assess) in the continuous monitoring mode.
Internal audits are less formal than independent assessments, but they are essential. Organizations that conduct regular internal reviews catch weaknesses before external assessors do, reducing the risk of unfavorable findings during a formal audit. A quarterly or semi-annual cadence is common among mature federal programs.
For a broader look at assessment types and methodologies, see our NIST 800-53 assessment guide.
Independent Audits
Independent audits are conducted by qualified external assessors. Unlike internal audits, an independent audit cannot be substituted by an internal review where formal authorization is required.
For FedRAMP, this means an accredited Third-Party Assessment Organization (3PAO). A list of FedRAMP-recognized 3PAOs can be found on the FedRAMP Marketplace under the “Assessors” tab. For FISMA, it involves independent assessors or the agency’s Inspector General (IG), who report results annually to the Office of Management and Budget (OMB).
Independent audits follow the assessment procedures defined in NIST SP 800-53A:
- The process begins with a Security Assessment Plan (SAP), a document developed collaboratively between the assessor and the organization.
- The SAP defines the scope, methodology, rules of engagement, and the specific controls to be tested. It sets out what will be tested, how it will be tested, and who is responsible for each part of the assessment.
- Using the SAP as a guide, the assessor applies the three SP 800-53A assessment methods: examining documentation and system configurations, interviewing personnel responsible for control implementation, and testing controls directly through vulnerability scans, penetration testing, and configuration validation.
- At the conclusion of the assessment, the assessor produces a formal Security Assessment Report (SAR).
- The SAR documents each control as satisfied, other than satisfied, or not applicable.
- Findings classified as “other than satisfied” require remediation and are tracked through a Plan of Action and Milestones (POA&M), a structured document that records each gap, its planned remediation action, the responsible party, and the target completion date..
- The SAR is a required component of the Authorization to Operate (ATO) package.
Internal Audit vs Independent Audit
| Dimension | Internal Audit | Independent Audit |
|---|---|---|
| Conducted by | Organization’s own team | Qualified external assessor (3PAO, IG) |
| Purpose | Continuous monitoring, gap identification | Formal ATO or reauthorization |
| Frequency | Ongoing / quarterly | Every 1-3 years |
| Output | Internal findings report | Security Assessment Report (SAR) |
| Required for | Best practice | ATO, FISMA, FedRAMP |
Both audit types ultimately evaluate the same thing: whether your controls work. Each serves a distinct role in keeping that answer current and defensible.
How often that answer is tested matters as much as the audit itself. Gaps in your audit cadence mean gaps in your visibility. Federal agencies under FISMA typically undergo independent assessment every three years, with continuous monitoring running between cycles. FedRAMP requires annual assessment by a 3PAO. Internal audits should run quarterly or on an ongoing basis to maintain readiness between formal evaluations.
The quality of any audit depends on the evidence available to assessors. The AU (Audit and Accountability) control family governs how that evidence is created, captured, and retained.
The AU (Audit and Accountability) Control Family
NIST 800-53 Rev 5 organizes its 1,196 controls into 20 families. Each family addresses a different security domain and describes what to protect. The AU (Audit and Accountability) family governs how organizations generate, protect, review, and retain the audit records that form the evidence auditors evaluate. AU is the only control family whose primary function is creating the evidence base that makes audits possible. Without proper AU implementation (event logging, record generation, log review) there is no audit trail for assessors to evaluate.
Key AU Controls
Four AU controls are required across every baseline, Low, Moderate, and High, making them universally applicable regardless of how a system is categorized.
| Control | Name | Purpose | Baseline Inclusion |
|---|---|---|---|
| AU-2 | Event Logging | Defines which events the system must log (e.g., login attempts, privilege escalation, data access) | Low, Moderate, High |
| AU-3 | Content of Audit Records | Specifies what each audit record must contain: what happened, when, where, source, outcome, and identity | Low, Moderate, High |
| AU-6 | Audit Record Review, Analysis, and Reporting | Requires regular review and analysis of audit logs for inappropriate or unusual activity | Low, Moderate, High |
| AU-12 | Audit Record Generation | Requires systems to generate audit records for the events defined in AU-2 at specified components | Low, Moderate, High |
AU-2 (Event Logging) is the starting point. It requires organizations to define which events must be logged, which includes failed authentication attempts, changes to user privileges, access to sensitive data, and system errors, among others. AU-2 is what gives an organization its logging policy.
AU-3 (Content of Audit Records) specifies the minimum information each log entry must contain. Auditors look for completeness: what event occurred, when it occurred, where in the system it occurred, the source of the event, the outcome (success or failure), and the identity of the user or process involved.
AU-6 (Audit Record Review) requires regular review and analysis of audit logs through a combination of automated and manual methods. This control is where many organizations fall short. Producing logs is straightforward. Reviewing them consistently for anomalies, unauthorized access, or policy violations requires deliberate process. Auditors will ask for evidence that log reviews happen and findings are acted upon.
AU-12 (Audit Record Generation) requires that systems are technically configured to produce audit records for the events defined in AU-2. This is the implementation counterpart to AU-2’s policy requirement.
AU in Context
A comprehensive NIST 800-53 audit evaluates controls across all 20 families based on the applicable baseline. The AU family ensures your organization has the logging and accountability foundation that auditors depend on. The remaining 19 families cover the security domains (access control, incident response, physical protection, and so on) that the audit evaluates.
In August 2025, NIST issued Release 5.2.0, which updated the related controls cross-references for AU-2 and AU-3 to reflect two newly added controls, SA-15(13) and SI-02(07). The core requirements of both controls remain unchanged. Organizations should verify they are working from the latest version.
Now that you understand what auditors look for, here is how to prepare.
How to Prepare for a NIST 800-53 Audit
Preparing for a NIST 800-53 audit requires a structured approach: identify your applicable baseline, document control implementation, gather evidence, conduct a gap analysis, remediate findings, and perform a dry run before the formal assessment.
The following six steps apply whether you face an internal self-assessment or a formal independent audit.
Step 1: Identify your baseline. Determine your system’s FIPS 199 categorization across confidentiality, integrity, and availability as Low, Moderate, or High impact. The highest impact score across those three objectives sets your overall system categorization and dictates which of the 1,196 controls apply. The Low baseline includes 149 controls, Moderate includes 287, and High includes 370. Most federal systems operate at Moderate.
Use NIST SP 800-60 to map your information types to impact levels, and confirm the final categorization with your system owner and authorizing official before scoping your audit.
Step 2: Document control implementation. For each applicable control, document how it is implemented in your environment. Record the implementation status (implemented, partially implemented, planned, or not applicable), the responsible parties, and a description of how the control operates. This documentation forms the core of your System Security Plan (SSP), which auditors will review line by line.
Controls inherited from a shared service provider or cloud platform should be documented as such, with clear boundaries between what the provider is responsible for and what the organization owns.
Step 3: Collect audit evidence. Gather artifacts that demonstrate each control is operating effectively. Evidence types include policies, procedures, configuration screenshots, log samples, training records, incident response plans, access control lists, and change management records. For system-level configuration and log evidence in particular, each artifact should document who gathered it, when it was gathered, how it was gathered, and from which system. Evidence that cannot answer those four questions is difficult to defend in a formal audit context.
Organize evidence by control family so assessors can find what they need quickly.
Step 4: Conduct a gap analysis. Compare your current control implementation against the applicable baseline. Identify controls that are missing, partially implemented, or lacking evidence. A partially implemented control is not a passing control. Auditors assess each control part individually, so gaps within a control matter as much as missing controls entirely.
Prioritize remediation based on risk. High-impact gaps that affect confidentiality, integrity, or availability should be addressed first. For risk prioritization methodology, see the NIST 800-53 risk assessment guide and our NIST 800-53 risk assessment.
Step 5: Remediate gaps. Address identified gaps using a Plan of Action and Milestones (POA&M). Each POA&M entry should include the control identifier, the nature of the gap, the planned remediation action, the responsible party, and the target completion date. Where full implementation is not feasible, document compensating controls and the residual risk.
Auditors expect to see a POA&M. Its absence signals poor risk management more than the gaps themselves.
Step 6: Perform a dry run. Conduct an internal self-assessment using NIST SP 800-53A assessment procedures before the formal audit. Walk through each applicable control as an auditor would: examine the documentation, check that evidence exists and is defensible, and test whether controls operate as described. Any issues surfaced here can be addressed before the formal assessment window opens, reducing the risk of findings that delay authorization.
Audit Preparation Timeline
| Step | Timeline | Activity | What to Produce |
|---|---|---|---|
| Step 1 | 6–12 months before | Identify the system’s FIPS 199 categorization and confirm the applicable NIST 800-53 baseline with the system owner and authorizing official | Documented system categorization and confirmed baseline (Low, Moderate, or High) |
| Step 2 | 6–12 months before | Document how each applicable control is implemented in the environment | System Security Plan (SSP) with control implementation descriptions, responsible parties, and implementation status |
| Step 3 | 4–6 months before | Collect evidence demonstrating that controls are operating as intended | Policies, procedures, configuration screenshots, log samples, training records, access control lists, change management records |
| Step 4 | 3–4 months before | Conduct a gap analysis comparing implementation and evidence against the applicable baseline and assessment procedures | Gap analysis report identifying missing, partially implemented, or undocumented controls, prioritized by risk |
| Step 5 | 1–3 months before | Remediate identified gaps and document remediation actions | Updated SSP, compensating control documentation, Plan of Action and Milestones (POA&M) entries |
| Step 6 | 1–2 months before | Perform an internal dry run using SP 800-53A assessment methods (examine, interview, test) | Internal assessment results, resolved issues, and an audit-ready evidence package |
| Audit window | External assessors review documentation, interview personnel, and test controls according to SP 800-53A procedures | Security Assessment Report (SAR), documented findings, and any required POA&M updates |
Starting early is critical. For organizations with many systems in scope, documentation and evidence collection alone can take several months. Beginning 6 to 12 months out gives teams enough runway to remediate gaps before the assessment window opens, rather than carrying open findings into a formal audit.
With a structured preparation plan in place, the right tools can accelerate every step.
Audit Tools and Automation
NIST 800-53 audits generate a significant operational burden. Evidence needs to be collected from multiple system owners, mapped to specific controls, organized by control family, and kept current as systems change. At scale, across multiple departments, campuses, or systems in scope, spreadsheets and shared drives create version conflicts, missed submissions, and last-minute scrambles that put authorization timelines at risk.
Audit tools and GRC platforms reduce that burden at every stage. They automate evidence collection, control status tracking, and reporting to reduce preparation time and improve accuracy.
The categories of tools that support NIST 800-53 audits include:
- GRC platforms for centralized control management, questionnaire distribution, and evidence collection mapped directly to controls and baselines
- SIEM (Security Information and Event Management) and log management solutions for AU family compliance, providing the centralized, queryable log records that auditors require as evidence for AU-2, AU-3, AU-6, and AU-12
- Vulnerability scanners for technical control validation, producing timestamped scan reports that serve as direct evidence for CM and SI family controls
- Configuration management tools for CM family evidence, capturing and retaining records of system configuration changes over time
- Document management systems for policy and procedure storage, ensuring version-controlled documentation is accessible and audit-ready
When evaluating an audit tool, look for built-in baseline mapping (Low, Moderate, and High), the ability to attach evidence to individual controls, assessment workflow automation, real-time control status dashboards, exportable audit reports, and role-based access that allows assessors to review evidence without full administrative access.
How Isora GRC Streamlines NIST 800-53 Audit Preparation
The hardest part of a NIST 800-53 audit is rarely the audit itself. It is the months of evidence collection, questionnaire distribution, and gap tracking that happen before an assessor walks in. For organizations managing controls across multiple departments, units, or campuses, that process can quickly become unmanageable without a shared workspace where every response, attachment, and completion status is visible in one place.
Isora GRC by SaltyCloud is built for exactly that.
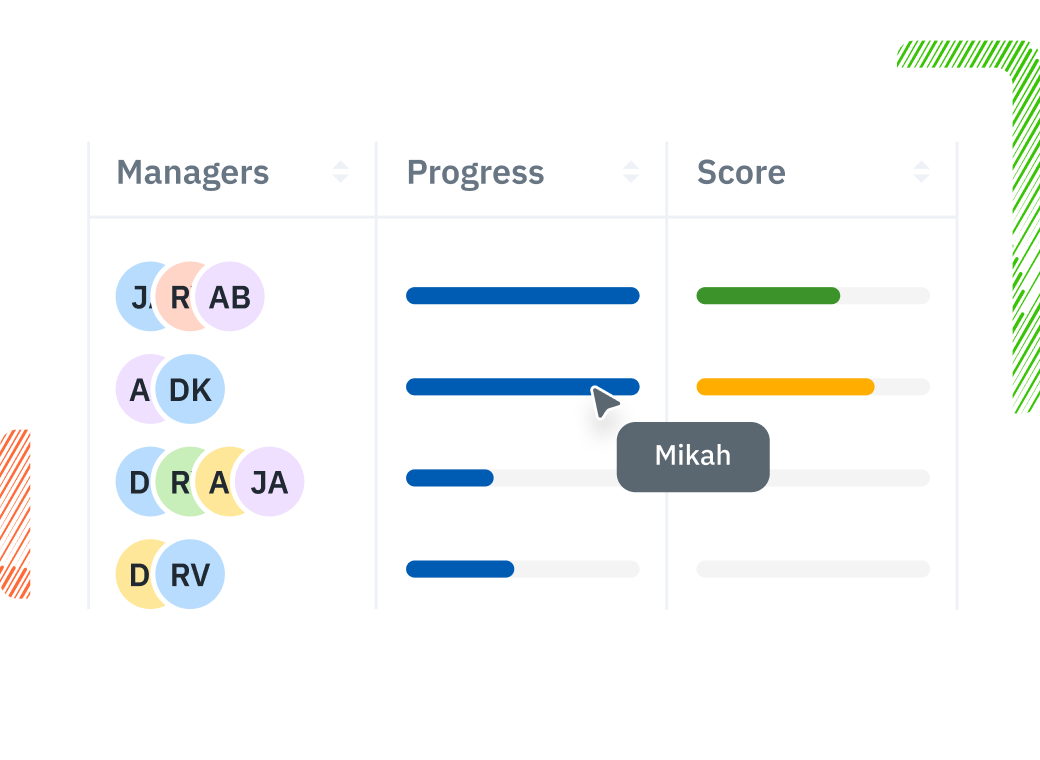
Assessment Questionnaire Distribution. Distribute control-specific questionnaires to unit owners, collect evidence directly within questionnaire responses, and track completion rates across the organization. Isora replaces the spreadsheet-and-email approach to evidence gathering with a shared assessment management workspace where every response and attachment is linked to its assessment.
Reports & Scorecards. Automated scoring and category comparisons show compliance posture across organizational units and control families. Filter by baseline (Low, Moderate, High) to focus on the areas that matter most for your upcoming audit. Generate exportable reports aligned to NIST 800-53 baselines with control-level detail that assessors need, reducing the back-and-forth that slows down formal evaluations. Explore Isora’s reports and scorecards.
Ready to simplify your next NIST 800-53 audit? Explore NIST 800-53 compliance software to see how Isora GRC can help.
Key Takeaways
A NIST 800-53 audit evaluates whether an organization’s controls, drawn from a baseline of 149, 287, or 370, are implemented correctly and producing the desired security outcomes. Internal audits keep you ready. Independent audits formalize compliance. The AU control family sits at the foundation of both, governing the audit trail that assessors depend on.
Preparation is manageable with the right approach. Start with your FIPS 199 categorization, document your controls in an SSP, collect defensible evidence, close gaps with a POA&M, and run a dry run before your assessment window opens. Begin the process 6 to 12 months before your audit window.
For organizations managing controls across multiple departments or systems, a GRC platform keeps evidence collection, completion tracking, and audit readiness in one place year-round, not just during active audit cycles.
Explore our full NIST 800-53 compliance guide for broader compliance guidance and work through the compliance checklist to start preparing today. Request a demo to see how Isora GRC simplifies NIST 800-53 audits for complex organizations.
NIST 800-53 Audit FAQs
What is a NIST 800-53 audit?
A NIST 800-53 audit is a systematic evaluation of an organization’s security and privacy controls against the NIST Special Publication 800-53 control catalog. Auditors assess whether each applicable control, from a catalog of 1,196 controls across 20 families, is implemented correctly, operating as intended, and producing the desired security outcomes. Audits may be internal (self-assessment) or independent (third-party).
How do you prepare for a NIST 800-53 audit?
NIST 800-53 audit preparation involves six steps: (1) identify your applicable baseline (Low, Moderate, or High), (2) document how each control is implemented, (3) collect evidence artifacts for each control, (4) conduct a gap analysis against the baseline, (5) remediate identified gaps with a Plan of Action and Milestones (POA&M), and (6) perform an internal dry run before the formal assessment.
What are the AU family controls in NIST 800-53?
The AU (Audit and Accountability) family contains controls governing how organizations generate, protect, review, and retain audit records. Key controls include AU-2 (Event Logging), AU-3 (Content of Audit Records), AU-6 (Audit Record Review, Analysis, and Reporting), and AU-12 (Audit Record Generation). All four appear in the Low, Moderate, and High baselines.
Is a NIST 800-53 audit mandatory?
NIST 800-53 audits are mandatory for federal agencies under the Federal Information Security Modernization Act (FISMA) and for cloud service providers seeking FedRAMP authorization. For private-sector organizations, NIST 800-53 adoption and auditing is voluntary but increasingly common as a best-practice control framework, especially for organizations handling federal data, including higher education institutions, healthcare organizations, and research environments.
How often are NIST 800-53 audits conducted?
Federal agencies under FISMA typically undergo a full independent assessment every three years, with continuous monitoring activities running between cycles. FedRAMP-authorized cloud service providers must complete an annual assessment by an accredited 3PAO. Most organizations supplement these formal cycles with quarterly or ongoing internal audits to maintain readiness and catch emerging gaps early.
What is the difference between a NIST 800-53 audit and a NIST 800-53 assessment?
An audit is a formal evaluation focused on determining whether controls meet compliance requirements, often tied to an authorization decision such as an ATO. An assessment is a broader term that encompasses initial evaluations, ongoing monitoring, and self-assessments used to measure control effectiveness. In practice, the terms overlap, but audits typically carry formal reporting obligations while assessments can be more flexible.
In the NIST context, internal audits follow RMF and SP 800-53A procedures, while self-assessments may or may not. For more on assessment types, see our NIST 800-53 assessment guide.
What is a Security Assessment Report (SAR)?
A Security Assessment Report (SAR) is the formal output of an independent NIST 800-53 audit. It documents the results of the security assessment, recording each control as satisfied, other than satisfied, or not applicable, and includes a recommendation on whether the system is ready for authorization.
For FedRAMP, the SAR is produced by the 3PAO and submitted as part of the Authorization to Operate (ATO) package. Findings classified as other than satisfied must be remediated and tracked in a POA&M before authorization can proceed.
What happens after a NIST 800-53 audit?
The outcome depends on the audit type. After an internal audit, the organization receives an internal findings report that identifies gaps and drives remediation through a POA&M. After an independent audit, the assessor produces a SAR. The Authorizing Official (AO) reviews the SAR and POA&M and makes a risk-based decision on whether to issue an ATO. If the ATO is granted, the organization enters a continuous monitoring phase, conducting ongoing internal audits and submitting periodic deliverables to maintain authorization. If findings are significant, the AO may require additional remediation before authorization is granted.
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.


















