 Table of Contents
Table of Contents
- How to Conduct a NIST 800-53 Risk Assessment: Complete Guide
- What Is a NIST 800-53 Risk Assessment?
- How NIST 800-37, 800-53, and 800-30 Work Together
- NIST SP 800-53: The Control Catalog
- NIST SP 800-30: The Methodology
- NIST 800-37 (RMF): The Lifecycle
- How to Prepare for a NIST 800-53 Risk Assessment
-
How to Conduct a NIST 800-53 Risk Assessment
- Step 1: Prepare for the Assessment
- Step 2: Characterize the Environment
- Step 3: Map Controls to Assessment Targets
- Step 4: Distribute Control-Based Questionnaires
- Step 5: Identify Implementation Gaps
- Step 6: Assess Likelihood and Impact
- Step 7: Determine Overall Risk
- Step 8: Recommended Risk Responses
- Step 9: Repeat Regularly
- How to Simplify NIST 800-53 Risk Assessments
-
NIST 800-53 Risk Assessment FAQs
- What is a NIST 800-53 risk assessment?
- What is the RA family in NIST 800-53?
- What is the difference between NIST 800-53 and NIST 800-30?
- What is the difference between NIST 800-53 and NIST 800-37?
- How often should a NIST 800-53 risk assessment be updated?
- What documentation does a NIST 800-53 risk assessment require?
- How does NIST 800-53 risk assessment relate to FedRAMP?
- Is a risk assessment template available for NIST 800-53?
- Conclusion
How to Conduct a NIST 800-53 Risk Assessment: Complete Guide
A NIST SP 800-53 risk assessment is the structured process for identifying threats, evaluating vulnerabilities, assessing control effectiveness, and determining residual risk across an organization’s information systems. It uses ve risk assessments use NIST 800-53 security and privacy controls as the benchmark, NIST 800-30 as the methodology to execute the assessment, and the NIST SP 800-37 Risk Management Framework (RMF) to integrate assessment results into the system authorization lifecycle.
This guide covers the full process—the 800-53 controls that govern risk assessment, the step-by-step methodology in 800-30, and how everything fits into the 800-37 RMF lifecycle. For a broader overview of the entire NIST 800-53 control catalog, see our complete guide to all 20 families.
What Is a NIST 800-53 Risk Assessment?
A NIST 800-53 risk assessment is the process an organization uses to evaluate cybersecurity risk across its information systems—from initial system categorization through control gap analysis, risk determination, and ongoing monitoring. The goal of an 800-53 risk assessment is to produce a defensible picture of existing risks, whether current controls adequately address them, and what residual risk remains for leadership to accept or act on.
Multiple NIST publications guide an 800-53 risk assessment, each playing a specific role:
- NIST SP 800-53 Rev 5 — The control catalog: Defines the security and privacy controls an organization must implement across 20 families. The Risk Assessment (RA) family governs the assessment program, but the assessment itself evaluates controls across all families.
- NIST SP 800-30 Rev 1 — The methodology: Outlines the analytical process for identifying threats, determining likelihood and impact, and calculating risk. This is how organizations execute the assessment.
- NIST SP 800-37 Rev 2 (RMF) — The lifecycle: Defines when risk assessment activities occur across the seven-step Risk Management Framework, from system categorization through authorization and continuous monitoring.
Supporting publications round out the picture:
- FIPS 199: The standard for categorizing systems by impact level (Low, Moderate, High)
- FIPS 200 / NIST SP 800-53B: Minimum security requirements and recommended control baselines for each impact level
- NIST SP 800-53A: Assessment procedures for evaluating whether implemented controls are working effectively
For the end-to-end compliance process, see our NIST 800-53 compliance guide.
How NIST 800-37, 800-53, and 800-30 Work Together
Each NIST publication plays a distinct role at each stage of the risk assessment process: NIST 800-53 defines what controls to satisfy, NIST 800-30 defines how to execute the analytical work, and NIST 800-37 defines when to act.
| NIST 800-30 (Phase) | NIST 800-53 (Controls) | NIST 800-37 (Step) |
| Prepare → | PM-09, PM-28 | ← Prepare |
| (Inputs to Conduct) → | RA-02 | ← Categorize |
| (Informed by risk) → | 800-53B Baselines | ← Select |
| (Informed by risk) → | All 20 Control Families | ← Implement |
| Conduct → | CA-02, RA-03, RA-05 | ← Assess |
| Communicate → | CA-06, RA-07 | ← Authorize |
| Maintain → | CA-07, RA-03(f), RA-05 | ← Monitor |
NIST SP 800-53: The Control Catalog
In NIST 800-53 Rev 5, the Risk Assessment (RA) family contains nine active controls to govern a risk assessment program—the policy, procedures, and recurring activities that keep risk assessment functioning. But the RA control family doesn’t define the full scope of the assessment itself. Instead, that spans every control family in the catalog.
The Risk Assessment Control Family
Five RA controls apply at every baseline level (Low, Moderate, and High):
- RA-01 — Risk Assessment Policy and Procedures: Requires a documented risk assessment policy covering purpose, scope, roles, and compliance requirements.
- RA-02 — Security Categorization: Requires classifying each information system as Low, Moderate, or High impact per FIPS 199. An authorizing official must approve the categorization. This step scopes the entire assessment—impact level determines the control baseline and the depth of analysis required.
- RA-03 — Risk Assessment: The core control. Requires conducting risk assessments that identify threats and vulnerabilities, determine likelihood and impact, integrate system-level findings with organization-wide and mission-level risk decisions, and document the results. NIST SP 800-30 provides the methodology for executing this control.
- RA-05 — Vulnerability Monitoring and Scanning: Requires regular automated and manual vulnerability scans, documented findings, and remediation tied to risk response processes. RA-5 provides the continuous technical data that feeds each RA-3 assessment cycle.
- RA-07 — Risk Response: Requires acting on assessment findings — risks can be mitigated, accepted with documented rationale, transferred, or avoided. Where immediate mitigation isn’t possible, a Plan of Action and Milestones (POA&M) is created.
The RA family also includes controls for:
- Technical Surveillance Surveys (RA-06)
- Privacy Impact Assessments (RA-08)
- Criticality Analysis (RA-09)
- Threat Hunting (RA-10)
Which of these controls apply depends on a system’s impact level and organizational context.
Other NIST 800-53 Control Families that Inform Risk Assessment
Two Program Management (PM) controls establish the governance context that scopes every assessment:
- PM-28 — Risk Framing: Requires organizations to document the assumptions, constraints, priorities, trade-offs, and risk tolerance that affect risk assessments, risk responses, and risk monitoring. This is where leadership defines the guardrails before any assessment begins.
- PM-09 — Risk Management Strategy: Requires a comprehensive, organization-wide strategy that includes acceptable risk assessment methodologies, risk tolerance expression, and mitigation strategies. PM-09 gives RA-03 its operating parameters.
Two Assessment, Authorization, and Monitoring (CA) controls also govern how the assessment process works:
- CA-02 — Control Assessments: Requires organizations to assess the controls in the security and privacy plans at a defined frequency to determine whether they are implemented correctly, operating as intended, and producing the desired outcome. The methodology comes from SP 800-53A.
- CA-06 — Authorization: Requires an authorizing official to review the risk assessment results and determine whether residual risk is acceptable before authorizing system operation. This is the decision point where your assessment work either clears the system for operation or triggers additional remediation.
NIST SP 800-30: The Methodology
NIST SP 800-30 is a risk management framework that organizes risk assessments into four phases—Prepare, Conduct, Communicate, and Maintain. NIST 800-30 also defines three tiers where assessment can operate:
- Tier 1 (Organization): Risk tolerance, strategic priorities, and resource allocation
- Tier 2 (Mission/Business Process): Risk to specific mission functions and business lines
- Tier 3 (Information System): System-level threats, vulnerabilities, and control effectiveness
Most teams start at Tier 3 and work up. However, because RA-03 requires that system-level findings integrate with organization-level and mission-level risk decisions, all three tiers matter.
NIST 800-37 (RMF): The Lifecycle
The Risk Management Framework (RMF) is the seven-step lifecycle in NIST SP 800-37 Rev 2 that governs how organizations manage security risk from system inception through decommissioning. Risk assessment feeds results into multiple 800-37 stages.
Here are the steps where risk assessment activity is most concentrated:
- Prepare — PM-28 and PM-09 establish the risk tolerance, assumptions, and methodology that scope every subsequent assessment.
- Categorize — RA-02 classifies the system per FIPS 199 and determines the control baseline.
- Assess — CA-02 and RA-03 evaluate control effectiveness and update risk determinations. This is where the 800-30 Conduct phase does most of its work.
- Authorize — The authorizing official uses RA-03 findings and the SAR to decide whether residual risk is acceptable.
- Monitor — RA-03(f), RA-05, and CA-07 keep the risk picture current as systems and threats evolve.
Risk assessment also informs the Select and Implement steps (risk conditions shape which controls are chosen and how they’re deployed), but the analytical work is concentrated in the five steps above. Organizations outside the federal mandate can apply the NIST CSF 2.0 risk assessment process as a less prescriptive alternative.
How to Prepare for a NIST 800-53 Risk Assessment
Proper preparation is essential for a successful NIST 800-53 risk assessment. That means accurately categorizing systems first, then clearly selecting and tailoring controls.
System Categorization
Before choosing any controls, categorize systems using FIPS 199. Here’s how:
- Clearly define the system boundary. Document precisely which hardware, software, data, users, and processes the system includes. Be explicit since ambiguity at this stage can create confusion later.
- List and classify information types. Identify all data the system handles (e.g., PII, financial records, CUI, healthcare data). Use NIST SP 800-60 Volumes I & II, Guide for Mapping Types of Information and Information Systems to Security Categories, to determine the security impact of each data type.
- Evaluate the security impact (CIA). For each identified information type, carefully evaluate:
-
- C: How harmful would unauthorized disclosure of this information be?
- I: How severe would unauthorized modification of the data be?
- A: How damaging would disruption or loss of access be?
Then, rate each criterion individually as Low, Moderate, or High:
-
- Low: Limited negative impact (inconvenient but minor disruption or risk).
- Moderate: Serious negative impact (significant harm or disruption to operations or reputation).
- High: Catastrophic negative impact (severe or critical harm to operations, reputation, or public safety).
- Determine the overall system categorization. Take the highest impact level from each category across all information types. The overall categorization directly determines the baseline controls to apply.
- Document categorization decisions: Provide written justification for why each rating was chosen, referencing specific data types, scenarios, and regulatory requirements. This documentation is crucial evidence for auditors and regulators.
Control Selection and Tailoring
After categorizing the system, carefully select and customize controls from NIST 800-53 Rev 5. Follow these specific steps to do it precisely and defensibly:
- Identify the baseline control set using NIST SP 800-53B: Based on system categorization, select the corresponding baseline controls from SP 800-53B as the starting point.
- Conduct an initial gap analysis. Review each control in the chosen baseline and document clearly:
-
- Fully implemented controls
- Partially implemented controls needing refinement
- Unimplemented controls requiring action
- Tailor the baseline for the system’s context. Adjust selected controls explicitly using these methods:
-
- Scoping: Remove controls that don’t apply and document reasons for doing so
- Parameterization: Set specific values and parameters within controls and document them with rationales
- Adding supplemental controls: Identify and add controls to address unique risks or regulatory requirements
- Defining inheritance: Document inherited controls for shared responsibilities with cloud providers and third parties
- Engage stakeholders and document decisions. Involve system owners, security officers, IT operations, compliance teams, and business leaders in decisions about control validation. Document exactly who participated, why each decision was made, and how each tailored control aligns with business goals and risk tolerance.
- Prepare a formal System Security Plan (SSP). Document the final tailored controls in an SSP that explicitly describes how each is implemented, who’s responsible, and the timeline for planned improvements or corrective actions.
How to Conduct a NIST 800-53 Risk Assessment
A NIST 800-53 risk assessment uses the methodology in NIST SP 800-30 Rev 1 to satisfy RA-03 requirements, combined with the control assessment procedures from SP 800-53A to evaluate whether controls across the full catalog are working effectively. It builds directly on the previous work of categorizing systems with FIPS 199 and selecting and tailoring security controls. Here, teams will assess each threat’s likelihood, measure the potential impact, prioritize the most critical risks, and document intended responses in great detail.
Following the NIST 800-30 methodology can show auditors, regulators, and leadership that an organization manages risk strategically, proactively, and with intention. But more importantly, it can help transform the risk assessment process into a more valuable tool for informed, strategic decision-making.
A NIST 800-53 risk assessment using NIST 800-30 involves structured questionnaires rather than technical testing or theoretical threat modeling. Organizations distribute questionnaires mapped directly to NIST 800-53 controls (like access management, data encryption, or incident response) to gather evidence and pinpoint gaps in implementation. This structured, questionnaire-based approach makes the assessment easier to manage and provides clear, actionable data on security controls.
Step 1: Prepare for the Assessment
Good preparation is the key to a useful, defensible risk assessment. Start by clearly defining what will be assessed, who will do it, how they’ll do it, and any limitations they might face.
To prepare for a NIST 800-53 assessment using the NIST 800-30 approach, organizations should:
- Define the scope. Identify the departments, systems, vendors, and business units to be assessed. Then, specify which NIST 800-53 control families are in scope for each.
- Assign responsibilities. Identify who will complete the questionnaires, who will provide supporting evidence, and who will review and approve findings.
- Choose assessment methods. Most organizations use structured questionnaires mapped to NIST 800-53 controls. Decide how these will be distributed, how responses will be collected, and what evidence is required to support answers.
- Set expectations. Document timelines, access limitations, known constraints, and any assumptions about existing controls or system conditions to help keep the process realistic and manageable.
This preparation phase sets the foundation for a focused, well-scoped assessment that actually produces valuable results.
Step 2: Characterize the Environment
Describing the system helps everyone understand exactly what they’re protecting. This step is about getting a clear picture of what’s being assessed. Rather than focusing only on technical systems, this phase captures context across departments, teams, vendors, and infrastructure, so control assignments and risk ratings are grounded in real operations.
To characterize the environment, organizations should:
- List what’s in scope. Document which departments, systems, applications, and vendors are being assessed. Be specific about names, functions, and ownership.
- Capture key context. For each item in scope, record relevant details like data sensitivity, system connectivity, regulatory requirements, and the types of users involved.
- Identify responsible stakeholders. Name the people or teams responsible for completing the assessment, providing evidence, and making decisions.
Having this context up front helps tailor control mappings, choose the right questionnaires, and interpret responses more accurately later in the process.
Step 3: Map Controls to Assessment Targets
Mapping controls to assessment targets means determining which NIST 800-53 controls apply to the teams, systems, or vendors in scope. The goal is to build a clear, targeted assessment that reflects how real responsibilities and risks are distributed across the organization.
To map controls effectively, organizations should:
- Match controls to the correct targets. Identify which NIST 800-53 controls are relevant to each team, department, system, or vendor.
- Tailor assessment templates. Create customized questionnaires based on the selected controls. Align questions with actual responsibilities and level of access to keep them focused and practical.
- Avoid one-size-fits-all assessments. Different parts of the organization manage various risks. Customizing control mappings and questionnaires improves the quality of responses and avoids unnecessary confusion.
This step builds the foundation for a more accurate, targeted risk assessment by asking the right questions to the right people.
Step 4: Distribute Control-Based Questionnaires
Distributing questionnaires is what shifts the assessment from planning to data collection. Here, organizations send structured questionnaires to the teams, departments, or vendors responsible for each assigned control. The goal is to gather clear, consistent information on whether controls are in place, and if not, why not.
To distribute control-based questionnaires effectively, organizations should:
- Send tailored questionnaires. Use the templates built in Step 3 to send only relevant questions to each group. Keep each assessment focused on that team’s specific responsibilities and access.
- Ask about control implementation status. For each control, ask whether it is fully implemented, partially implemented, or not in place. Require evidence or comments to explain each answer.
- Set clear expectations for response quality. Make it easy for respondents to know what’s expected—what counts as complete, what kind of documentation is helpful, and when responses are due.
- Track participation and progress. Monitor who has completed their questionnaires and follow up with teams that need support, clarification, or reminders.
This step gives organizations the data they need to identify gaps, track control coverage, and prepare for the next phase: analyzing the results.
Step 5: Identify Implementation Gaps
Identifying implementation gaps means reviewing the results to determine where controls aren’t entirely in place. Gaps in control implementation–whether due to missing documentation, partial coverage, or unclear ownership–represent real security risks and must be documented clearly.
To identify implementation gaps, organizations should:
- Review questionnaire responses. Look for answers marked as “partially implemented” or “not implemented,” especially those lacking supporting evidence or clear explanations.
- Validate missing or weak controls. Confirm whether incomplete answers reflect actual gaps or just incomplete documentation. Follow up with teams when clarification is needed.
- Log each gap. For every control that isn’t fully implemented or lacks verifiable evidence, record the issue in a risk register along with any available context.
- Separate minor issues from major ones. Not all gaps carry the same weight. Start organizing them now based on what’s missing, how critical the control is, and where it is applied.
This step lays the foundation for risk scoring and prioritization by turning raw questionnaire data into a structured list of real, actionable issues.
Step 6: Assess Likelihood and Impact
Assessing the likelihood and impact means estimating how serious each control gap is. This step involves estimating how likely a gap is to cause a security incident and how much damage would result if it occurred. Together, these two ratings form the foundation for prioritizing remediation.
To assess likelihood and impact, organizations should:
- Review the context around each gap. Examine the system or vendor involved, the type of control that’s missing, and any known threats or weaknesses that might make the vulnerability riskier.
- Estimate the likelihood. Based on system exposure, criticality, past incidents, and current protections, rate how likely the missing control could lead to a real-world issue. Use simple categories like High, Moderate, or Low.
- Evaluate the potential impact. Consider what could happen if each gap were exploited–lost data, downtime, compliance violations, financial loss, reputational damage–and rate the severity.
- Document both ratings. Record the reasoning behind the likelihood and impact ratings for each gap to make it easier to explain decisions later and help teams focus on what matters most.
This step helps teams turn a list of control gaps into a clear risk picture. It shines a direct spotlight on where the most significant problems are and which issues need attention first.
Step 7: Determine Overall Risk
Determining risk involves combining likelihood and impact ratings into clear, easy-to-understand risk rankings. This step helps teams clearly identify exactly which threats and vulnerabilities require immediate attention and which risks are lower priorities.
To determine overall risk, organizations should:
- Assign a risk level to each gap. Use a simple matrix to combine the likelihood and impact scores into a final rating (High, Moderate, or Low). For example, a gap that’s highly likely and high impact should be rated High.
- Prioritize based on real consequences. Sort control gaps by risk level so teams can see at a glance which ones require immediate attention and which can be addressed over time.
- Document each risk decision. Include a short explanation of why the risk level was chosen. This will help with future reviews, keep stakeholders aligned, and make audits smoother.
This step turns that risk picture into a clear, ranked set of priorities that gives security and compliance teams a concrete action plan.
Step 8: Recommended Risk Responses
Recommending specific risk responses means deciding what to do about them. Each control gap needs a clear, documented response so everyone understands what’s being addressed, what’s being accepted, and what happens next.
To recommend risk responses, organizations should:
- Summarize each control gap and its risk level. For each gap, restate the affected control, its status (e.g., not implemented, no evidence), and the associated likelihood and impact ratings.
- Select a response strategy. For each risk, choose one of the following:
- Implement: Plan to close the gap by fully implementing the missing control.
- Accept: Decide to leave the gap unaddressed, often due to low risk or resource limits.
- Transfer: Shift responsibility for the risk to a third party, such as a vendor or insurer.
- Mitigate: Reduce the risk through partial fixes or compensating controls.
- Document the rationale. Clearly explain why each response was chosen. This will help stakeholders understand tradeoffs and give auditors a clear view of your risk decisions.
- Share decisions with stakeholders. Communicate the proposed responses to everyone involved—system owners, business leaders, and compliance teams—so they can review, approve, and move forward.
This second-to-last step turns your risk register into a strategic advantage, connecting assessment results to clear, trackable decisions.
Step 9: Repeat Regularly
Update the risk assessment at a defined frequency and whenever significant changes occur—new systems, configuration changes, newly disclosed vulnerabilities, threat intelligence updates, or findings from audits and penetration tests.
To keep the process current and reliable, organizations should:
- Set a cadence. Most teams reassess annually, but higher-risk systems may need quarterly reviews, and significant changes should always trigger reassessments.
- Refresh questionnaires. Update assessment templates to reflect new risks, updated control requirements, or lessons learned from previous cycles.
- Compare across cycles. Use historical data to track which control gaps are getting fixed, which ones are recurring, and where progress is stalling..
- Close the loop. Share findings and next steps with the teams participating in the assessment to keep people engaged.
Repeating the process regularly helps build momentum toward a risk assessment process that actually reflects what’s happening across systems and teams. For the full SP 800-30 methodology—including threat source tables and risk matrices—see our NIST 800-30 guide.
NIST SP 800-137 covers continuous monitoring program design in detail and is the primary reference for building a monitoring strategy aligned with 800-53 requirements.
How to Simplify NIST 800-53 Risk Assessments
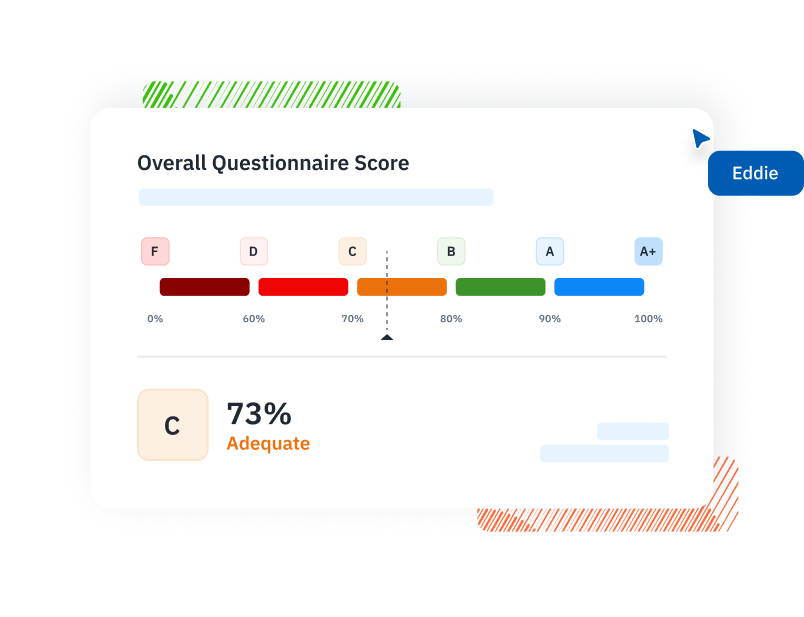
Isora GRC by SaltyCloud connects risk assessment findings directly to control implementation — replacing disconnected spreadsheets with a shared workspace where assessments, risks, assets, and vendors are all connected. With Isora, organizations can simplify NIST 800-53 risk assessments with:
- A risk register: Document and track risks identified during assessments using a built-in risk management tool, with risks published directly from assessment findings and remediation monitored over time.
- A risk matrix: Visualize risk posture across systems using a likelihood-impact matrix to prioritize where to focus.
- Assessment integration: Risk findings connect directly to assessment workflows, creating a continuous feedback loop between risk identification and control evaluation.
Learn how NIST 800-53 compliance software supports risk assessment at scale.
NIST 800-53 Risk Assessment FAQs
What is a NIST 800-53 risk assessment?
A NIST 800-53 risk assessment is the process of identifying threats, evaluating vulnerabilities, assessing control effectiveness, and determining residual risk across your organization’s information systems. It uses the 800-53 control catalog as the benchmark, the 800-30 methodology to execute the analysis, and the RMF lifecycle to integrate results into system authorization and continuous monitoring.
What is the RA family in NIST 800-53?
The RA (Risk Assessment) family contains nine active controls — RA-1 through RA-10, with RA-4 withdrawn in Rev 5 and absorbed into RA-3. These controls govern the risk assessment program — policy (RA-1), system categorization (RA-2), assessment execution (RA-3), vulnerability monitoring (RA-5), and risk response (RA-7). The actual risk assessment evaluates controls across all 20 families, not just RA.
What is the difference between NIST 800-53 and NIST 800-30?
NIST SP 800-53 defines the controls your organization must implement—the what. NIST SP 800-30 provides the four-phase methodology for assessing risk against those controls (Prepare, Conduct, Communicate, Maintain)—the how. Together, they define what to assess and how to assess it.
What is the difference between NIST 800-53 and NIST 800-37?
NIST SP 800-53 is the control catalog—the what. NIST SP 800-37 defines the Risk Management Framework lifecycle—the when. RMF’s seven steps determine where risk assessment activities occur within system authorization and ongoing operations. RA-03 assessments can be conducted at every RMF step, not just during initial authorization.
How often should a NIST 800-53 risk assessment be updated?
RA-03 requires updates at an organization-defined frequency and whenever significant changes affect your system, environment, or threat landscape. Most organizations run formal annual assessments and supplement them with continuous monitoring throughout the year.
What documentation does a NIST 800-53 risk assessment require?
Three primary deliverables: the System Security Plan (SSP) documenting system boundaries, controls, and implementation; the Security Assessment Report (SAR) summarizing findings and control effectiveness; and the Plan of Action and Milestones (POA&M) tracking identified gaps with remediation plans. Results should also feed into an ongoing risk register.
How does NIST 800-53 risk assessment relate to FedRAMP?
FedRAMP requires cloud service providers to conduct risk assessments that satisfy the NIST SP 800-53 RA controls — all five core RA controls are required at every FedRAMP impact level. Results feed into the FedRAMP authorization package and must be kept current through continuous monitoring.
Is a risk assessment template available for NIST 800-53?
NIST doesn’t publish an official risk assessment template, but SP 800-30 Appendices D–L define the required structural elements. Most organizations build spreadsheet-based templates that capture system categorization, threats, vulnerabilities, likelihood, impact, control effectiveness, risk response decisions, and ownership.
Conclusion
A NIST 800-53 risk assessment uses the RA controls to govern the program, NIST 800-30 as the methodology, NIST 800-37 to integrate results into the system lifecycle, and the actual assessment evaluates controls across all 20 families to determine whether an organization’s residual risk is acceptable. Applied consistently—from initial categorization through ongoing reassessment—the process produces the evidence that justifies control selection, drives remediation, and keeps risk pictures accurate as systems and threats change.
Discover how Isora GRC simplifies NIST 800-53 risk assessments at scale.
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.


















