 Table of Contents
Table of Contents
ISO 27001 vs NIST 800-53: Which Standard Is Best?
ISO 27001 and NIST 800-53 are two of the most widely adopted security frameworks in the world, but they differ fundamentally in origin, structure, and certification.
- ISO 27001 lets organizations earn a globally recognized security certificate that demonstrates their security program meets an international standard.
- NIST 800-53 provides a comprehensive, prescriptive security and privacy framework covering areas from access control to supply chain risk management. For federal agencies and contractors, it is the mandatory baseline for operating and securing federal systems.
The right choice depends on where an organization operates and who it serves. Organizations needing a globally portable security credential pursue ISO 27001 — a risk-driven program verified by independent auditors. US federal agencies, DoD contractors, and cloud providers seeking FedRAMP authorization must comply with NIST 800-53, which requires implementing pre-defined controls on federal information systems.
For organizations evaluating both: ISO 27001 focuses on security program maturity, NIST 800-53 on system-level control coverage.
This article is part of our NIST 800-53 framework comparisons series. It covers the key differences in scope, certification, and control structure, how ISO 27001 and NIST 800-53 controls map to each other, and how organizations can use both frameworks to meet compliance obligations without duplicating effort.
International Standard vs US Federal Security Framework
The fundamental difference is jurisdictional scope — one is built for the world, the other for the US federal government.
ISO/IEC 27001:2022 is an international standard published jointly by the International Organization for Standardization(ISO) and the International Electrotechnical Commission (IEC). NIST Special Publication 800-53 Revision 5 is a U.S. federal framework published by the National Institute of Standards and Technology (NIST) primarily for federal information systems.
ISO 27001 is an international information security management system (ISMS) standard published by ISO/IEC with 93 controls in Annex A across 4 themes, certifiable by accredited third-party auditors. NIST 800-53 is a US federal security and privacy control catalog containing 1,196 controls across 20 families, mandated for federal systems under FISMA, with no formal certification pathway.
Control Selection
ISO 27001 lets organizations choose their own controls based on a risk assessment. NIST 800-53 assigns a pre-defined set of controls based on system impact level.
ISO 27001:2022, recognized in over 160 countries and released in October 2022 (with all ISO 27001:2013 certifications expired as of October 31, 2025), takes that risk-based approach.
Organizations conduct a risk assessment and use the results to determine which controls apply to them from Annex A, ISO 27001’s security control catalog covering areas from access control to supplier relationships. All 93 controls are considered, and organizations document their selections and exclusions in a Statement of Applicability (SoA). There is no mandatory baseline. Most organizations implement between 60 and 90 controls depending on their risk profile and scope.
NIST 800-53 is primarily used by US federal agencies under the Federal Information Security Modernization Act(FISMA), and by organizations pursuing FedRAMP authorization or supporting federal systems. The current version, NIST SP 800-53 Rev 5 published September 2020 (with Release 5.2.0 issued August 2025 adding controls for software update security), tells organizations exactly which controls to implement based on whether their system’s impact level is Low, Moderate, or High.
The impact levels are determined through a formal system categorization process under FIPS 199. The higher the sensitivity of the data and the potential impact of a breach, the higher the baseline. A Low baseline requires implementing around 125 controls, a Moderate baseline around 325, and a High baseline around 421.
For a deeper look at the catalog’s structure, see our NIST 800-53 complete guide. For a breakdown of changes in the current revision, see our NIST 800-53 Rev 5 guide.
NIST 800-53 provides less flexibility but more specific guidance. That structural difference drives the biggest practical distinction between the two: certification.
Certification vs Compliance
Certification is the primary difference between the two frameworks — while ISO 27001 offers a formal third-party certification pathway, NIST 800-53 does not.
ISO 27001 certification is conducted by accredited bodies such as British Standards Institution (BSI), Bureau Veritas, or Schellman. The certificate is valid for three years, with annual surveillance audits required to maintain it. Holding an ISO 27001 certificate provides market-recognized proof of security maturity that organizations can present to customers, partners, and regulators worldwide.
Preparation typically takes 6 to 12 months depending on organizational maturity, with certification audits and implementation costs ranging from tens of thousands to over $100,000 depending on scope and remediation required.
NIST 800-53 compliance follows the Risk Management Framework (RMF) process, which results in an Authority to Operate (ATO) rather than a certificate. Cloud service providers can achieve FedRAMP authorization, which verifies NIST 800-53 compliance, through a third-party assessment organization (3PAO). No standardized NIST 800-53 certificate exists. Organizations maintain compliance through continuous monitoring under the RMF cycle — ongoing control assessments, security reporting, and plan of action tracking.
To understand how NIST 800-53 and the RMF work together in practice, see our NIST 800-53 and RMF integration guide. For a full walkthrough of the compliance process, see our NIST 800-53 compliance guide.
The consequences of non-compliance are well-documented. A June 2024 GAO report (GAO-24-107231) found that 567 of 1,610 cybersecurity recommendations made since 2010 remained unimplemented across federal agencies, with only 8 of 23 civilian CFO Act agencies rated “effective” for their information security programs. The Department of Energy OIG issued 79 new NIST 800-53 recommendations during FY 2024, with 44 prior-year recommendations still open. The Department of Health and Human Services received a “Not Effective” FISMA rating for the sixth consecutive year in FY 2025, failing to achieve “Managed and Measurable” maturity in any cybersecurity function area.
When Does Certification Matter?
ISO 27001 certification matters when selling to enterprise or international markets, where it functions as externally validated proof of a structured security program.
NIST 800-53 becomes a hard requirement for organizations operating within the US federal ecosystem. Federal agencies must comply under FISMA, and cloud providers must meet NIST 800-53 requirements to achieve FedRAMPauthorization. Contractors and vendors supporting federal systems are also subject to the framework.
Organizations that need a certificate to win customers pursue ISO 27001. Organizations that need to operate within the US federal ecosystem must comply with NIST 800-53 regardless of certification.
A notable 2026 development: FedRAMP RFC-0022 formally recognizes ISO 27001 as a qualifying external framework for a fast-track FedRAMP 20x Level 1 authorization pathway, allowing cloud service providers with current ISO 27001 certification to reduce redundant assessment work when pursuing FedRAMP Validated status. This is the first formal federal mechanism acknowledging that ISO 27001 provides overlapping assurance value with FedRAMP baselines.
Control Mapping
Most ISO 27001 Annex A controls have corresponding NIST 800-53 controls, though the mapping is not one-to-one due to NIST’s greater granularity.
ISO 27001:2022 contains 93 controls in Annex A organized across four themes: Organizational, People, Physical, and Technological. NIST 800-53 Rev. 5 contains 1,196 controls across 20 control families, including access control, incident response, system integrity, and risk assessment.
The size difference comes down to granularity. NIST 800-53 breaks controls into much more specific requirements than ISO 27001, so a single ISO 27001 control often maps to several NIST 800-53 controls.
NIST publishes formal mapping guidance that shows exactly how ISO 27001 Annex A controls correspond to NIST 800-53 control families. Organizations pursuing both can use this mapping to identify where existing controls already satisfy requirements under the second framework and where gaps remain. The crosswalk notes that these tables provide a general indication of coverage and cautions against assuming control equivalency without independent analysis.
The highest overlap sits in areas like access control, cryptography, incident management, risk assessment, and audit logging. The table below shows specific mapping examples.
| Domain | Security Objective | ISO 27001:2022 Annex A Control | NIST 800-53 Rev 5 Control | What the Mapping Shows |
| Governance | Security governance and policy framework | A.5.1 Policies for information security | Policy and Procedures controls across NIST control families (e.g., AC-1, IR-1, CM-1, RA-1) | ISO defines a single overarching policy requirement, while NIST requires domain-specific policy documentation for each control family. |
| Access Control | Privileged access management | A.8.2 Privileged access rights | AC-6 Least Privilege, AC-6(1), AC-6(5) | ISO defines the governance requirement for privileged access. NIST expands it into detailed technical controls enforcing least privilege. |
| Incident Response | Incident response planning | A.5.24 Incident management planning | IR-1 Incident Response Policy, IR-8 Incident Response Plan | Both frameworks require incident response capability, but NIST separates policy, planning, and operational controls. |
| Configuration Management | Secure system configuration | A.8.9 Configuration management | CM-2 Baseline Configuration, CM-6 Configuration Settings | NIST defines detailed baseline and configuration enforcement requirements beyond ISO’s broader governance requirement. |
| Cryptography | Cryptographic protection | A.8.24 Use of cryptography | SC-12 Cryptographic Key Management, SC-13 Cryptographic Protection | ISO defines when cryptography should be used. NIST specifies how encryption and key management must be implemented. |
NIST SP 800-53 Rev 5 includes ISO 27001 mappings directly within its control descriptions, which makes it straightforward to see where the two frameworks align. Organizations can use these mappings to run a gap analysis, identifying which controls already satisfy both standards and where additional work is needed. For guidance on the risk assessment process that underpins NIST 800-53 control selection, see our NIST 800-53 risk assessment guide.
Control Mapping Limitations
ISO 27001 has no direct equivalents for some NIST control families, such as Program Management (PM). NIST 800-53 does not address the management system requirements in ISO 27001 clauses 4 through 10 — organizational context, leadership commitment, and continual improvement — the requirements that make ISO 27001 a management system standard.
Which Standard Should You Use?
The right standard depends on three factors: where the organization operates, who its customers are, and what regulatory obligations it faces.
Pursue ISO 27001 if the organization:
- Operates internationally. ISO 27001 is the globally recognized security credential and the default certification for commercial transactions in Europe and the Asia-Pacific region.
- Is a SaaS provider, technology vendor, or services company serving enterprise or commercial markets. ISO 27001 certification is frequently required by enterprise customers as a condition of doing business.
- Faces customer or partner requirements for third-party certification. Without it, deals can stall or fall through entirely at the security review stage.
- Is building an ISMS from the ground up. The standard provides a structured, risk-driven framework for establishing and maturing a security program.
Pursue NIST 800-53 if the organization:
- Is a US federal agency subject to FISMA. NIST 800-53 is mandatory for all federal information systems.
- Is pursuing FedRAMP authorization. Cloud service providers must demonstrate NIST 800-53 compliance through a 3PAO assessment.
- Supports federal information systems. Contractors and vendors connected to federal systems are subject to NIST 800-53 or related standards.
Higher education institutions often need both. Universities serving international students and partners benefit from ISO 27001 certification, while those receiving federal research funding must comply with NIST 800-53 or NIST 800-171depending on the systems involved.
For a deeper look at scoping federal compliance requirements, see our CUI and FCI scoping guide.
Geography matters. ISO 27001 dominates in Europe and the Asia-Pacific region, where it is frequently the default security certification for commercial transactions. NIST 800-53 is primarily US-centric, tied to federal acquisition and regulatory requirements.
Customer requirements often drive the decision. Enterprise SaaS companies typically face requests for ISO 27001 certification from prospective customers. Organizations bidding on US government contracts must comply with NIST 800-53 or related standards such as NIST 800-53 vs 800-171 for contractor environments. For additional NIST comparisons, see our analysis of NIST CSF vs 800-53.
Implementing Both Frameworks Together
An organization compliant with one standard has already completed a substantial portion of the work for the other.
NIST’s official bilateral mapping shows that the majority of ISO 27001:2022 Annex A controls have corresponding NIST 800-53 Rev 5 controls. NIST’s catalog also contains controls — particularly in the privacy (PT), program management (PM), and systems security families — with no direct ISO equivalent, but the core security domains overlap significantly.
A practical approach to pursuing both:
- Start with whichever standard is most urgent. Let contract requirements or audit deadlines drive the first priority.
- Run a gap analysis using NIST’s published control mappings. Identify which controls from the second standard the existing program already satisfies.
- Implement the remaining gap controls. The majority of core security domains overlap, so the gap is typically manageable.
- Maintain both through integrated compliance management. Use a single internal control framework and map outward to both standards, reducing duplicate assessment and documentation work.
| Dimension | ISO 27001 | NIST 800-53 |
| Full Name | ISO/IEC 27001:2022 | NIST SP 800-53 Rev 5 |
| Publisher | ISO/IEC (International) | NIST (U.S. Department of Commerce) |
| Scope | Any organization, any industry, globally | US federal information systems |
| Number of Controls | 93 controls (Annex A) | 1,196 controls |
| Control Structure | 4 themes (Organizational, People, Physical, Technological) | 20 control families |
| Approach | Risk-based (select controls via risk assessment) | Prescriptive baselines (Low, Moderate, High) |
| Certification | Yes, third-party certification by accredited bodies | No direct certification (ATO via RMF) |
| Certification Validity | 3 years with annual surveillance audits | Ongoing (continuous monitoring under RMF) |
| Primary Audience | Global organizations, commercial sector | US federal agencies, FedRAMP CSPs |
| Regulatory Driver | Customer/market requirements, GDPR alignment | FISMA, FedRAMP, US government contracts |
| Cost of Entry | Certification audit fees + consultant costs | RMF process + 3PAO audit (FedRAMP) |
| Privacy Controls | Via ISO 27701 extension | Yes (dedicated PT family) |
| Free to Access? | No (must be purchased from ISO) | Yes (freely available at csrc.nist.gov) |
Tools that support both frameworks streamline this process significantly by maintaining a single source of truth for shared controls.
How To Simplify Multi-Framework Compliance
Organizations managing compliance across both ISO 27001 and NIST 800-53 need a single workspace where assessments, risks, and evidence are connected — not duplicated across spreadsheets and disconnected tools.
Isora GRC is the collaborative GRC Assessment Platform™ that gives security teams one shared workspace to run assessments, manage vendors and assets, track live risks, and publish audit-ready reports. Isora scales with the security program, supporting additional frameworks, vendors, and organizational units without losing consistency.
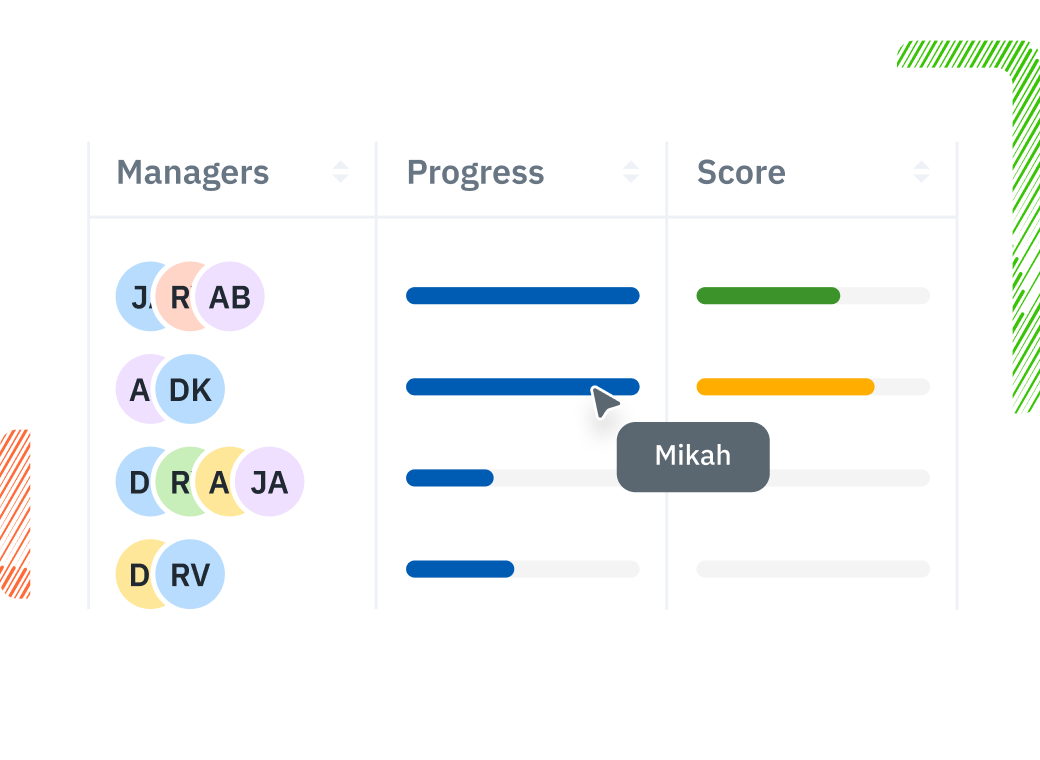
Organize assessments by compliance goal — whether that means an ISO 27001 internal audit cycle or a NIST 800-53 RMF assessment. Isora streamlines complex campaigns by tracking progress across the organization from a single dashboard, eliminating the need for separate assessment programs for each standard.
Distribute pre-built questionnaires aligned to NIST 800-53 and ISO 27001 to unit owners, with collaborative evidence collection built into every response. Multiple contributors can add responses, upload evidence, and comment — reducing time spent on assessment tasks across both frameworks.
Generate clear visibility into compliance posture across both frameworks through automated scoring and category comparisons, with drill-down capability from summary scores to individual control responses. Frees up time for more strategic risk management tasks.
See how Isora GRC supports multi-framework compliance — explore NIST 800-53 compliance software or request a demo.
Key Takeaways
ISO 27001 is an international, certifiable ISMS standard with 93 Annex A controls selected through risk assessment. NIST 800-53 is a US federal control catalog with 1,196 controls assigned by system impact level (Low, Moderate, High) under FISMA — no formal certification pathway exists. ISO 27001 certification is conducted by accredited bodies and valid for three years; NIST 800-53 compliance results in an Authority to Operate (ATO) through the Risk Management Framework.
NIST publishes an official bilateral mapping showing the majority of ISO 27001 Annex A controls have corresponding NIST 800-53 equivalents, though NIST’s privacy, program management, and advanced systems security controls have no ISO counterpart. Organizations pursuing both should start with whichever standard is most urgent, run a gap analysis using NIST’s published crosswalk, implement the remaining controls, and maintain both through a single unified control framework. FedRAMP RFC-0022 (2026) formally recognizes ISO 27001 as a qualifying external framework for a fast-track FedRAMP 20x Level 1 authorization pathway — the first federal mechanism linking the two.
For a deeper look at NIST 800-53’s structure, see the NIST 800-53 complete guide. For the full compliance process, see the NIST 800-53 compliance guide. For additional framework comparisons, see the NIST 800-53 framework comparisons hub.
ISO 27001 vs NIST 800-53 FAQs
What is the difference between ISO 27001 and NIST 800-53?
ISO 27001 is an international Information Security Management System (ISMS) standard with 93 Annex A controls and a formal third-party certification pathway. NIST 800-53 is a U.S. federal security and privacy control catalog containing 1,196 controls mandated for federal information systems under FISMA. ISO 27001 is risk-based and certifiable; NIST 800-53 is prescriptive and compliance-based.
Can you get certified in NIST 800-53?
No. There is no formal “NIST 800-53 certification” equivalent to ISO 27001. Federal agencies demonstrate compliance through the Risk Management Framework (RMF), resulting in an Authority to Operate (ATO). Cloud providers can achieve FedRAMP authorization, which verifies NIST 800-53 compliance through a third-party assessment organization, but this is not a portable certificate.
Do ISO 27001 controls map to NIST 800-53?
Yes. NIST provides formal mapping guidance in SP 800-53 Rev 5 showing significant overlap between ISO 27001 Annex A and NIST 800-53 controls. The mapping is not one-to-one — a single ISO control often corresponds to multiple NIST controls due to NIST’s greater granularity.
Should I get ISO 27001 or comply with NIST 800-53?
It depends on regulatory obligations and market. Organizations operating federal systems or supporting U.S. federal agencies must comply with NIST 800-53. Organizations serving international customers or needing a market-recognized security credential pursue ISO 27001. Many organizations pursue both.
Is ISO 27001 easier than NIST 800-53?
Neither is inherently “easier.” ISO 27001 has fewer controls (93 vs 1,196) but requires building a full ISMS with management system documentation. NIST 800-53 has more controls but provides prescriptive implementation guidance. The effort depends on organization size, existing maturity, and whether the work involves full implementation or gap remediation.
Can you comply with both ISO 27001 and NIST 800-53?
Yes. NIST’s official bilateral mapping shows the majority of ISO 27001 Annex A controls have corresponding NIST 800-53 controls. Organizations can implement a unified control framework and map outward to both standards, reducing duplicate assessment and documentation work.
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.


















