 Table of Contents
Table of Contents
- NIST 800-53 Data Classification: How It Determines Your Controls
- What Are Data Categorization Controls in NIST 800-53?
- FIPS 199 Impact Levels (Low, Moderate, High)
- How Classification Determines Control Baselines
- Practical Data Classification Approach
- How to Simplify NIST 800-53 Data Classification
- Key Takeaways
- NIST 800-53 Data Classification FAQs
NIST 800-53 Data Classification: How It Determines Your Controls
Before selecting the right NIST 800-53 controls, organizations must classify their data to determine which of the framework’s 1,196 controls apply to their systems.
NIST Special Publication 800-53 Rev 5 is the federal government’s primary security and privacy control catalog. It organizes its controls into three baselines: Low (149 controls), Moderate (287 controls), and High (370 controls). The baseline that applies depends on the potential impact to the organization if a system or its data were compromised. Data classification through the Federal Information Processing Standard (FIPS) 199 determines which baseline applies.
Required under the Federal Information Security Modernization Act (FISMA), NIST 800-53 uses a tiered approach where data classification sets the appropriate tier.
Part of our NIST 800-53 complete resource center, this guide explains how FIPS 199 categorization works, what the three impact levels mean, and how classification maps directly to control selection.
What Are Data Categorization Controls in NIST 800-53?
NIST 800-53 includes specific controls that require organizations to categorize their information and systems, most notably within the Risk Assessment (RA) and Program Management (PM) families which govern how organizations identify, document, and manage security requirements at both the system and enterprise level. These controls mandate that the classification process happens and is documented.
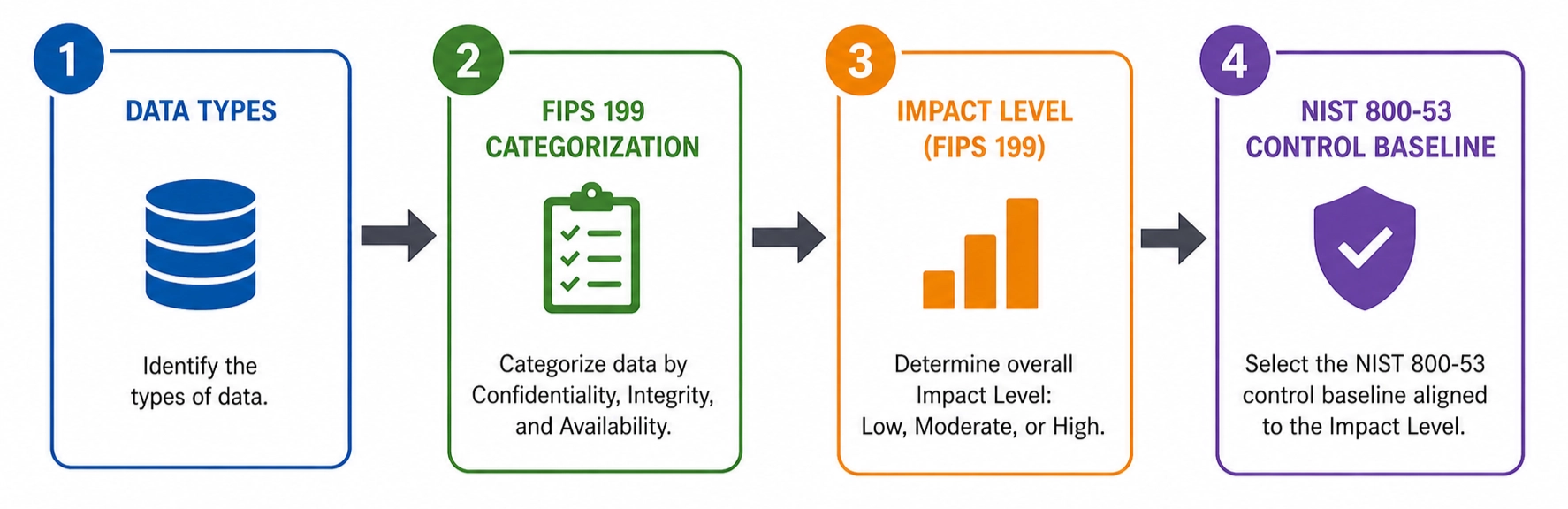
NIST 800-53 data classification is the process of categorizing information and information systems by potential impact level (Low, Moderate, or High) using the Federal Information Processing Standard (FIPS) 199 framework. This categorization determines which of the three NIST 800-53 control baselines (149, 287, or 370 controls) an organization must implement.
RA-2 (Security Categorization)
RA-2 is the primary control governing data classification in NIST 800-53. It requires organizations to categorize their information systems in accordance with FIPS 199 and document the results in the System Security Plan (SSP). RA-2 also requires the authorizing official to review and approve the categorization decision before control selection begins.
OMB Circular A-130 reinforces these obligations at the policy level, requiring federal agencies to use FIPS 199 for system categorization and to maintain SSPs as part of their information security programs.
This is a mandatory step in the Risk Management Framework (RMF) process. NIST SP 800-37 Rev. 2 Section 3.2 defines the three Categorize step tasks (system description, security categorization, and categorization review and approval) that must be completed before control selection begins.
PM-7 (Enterprise Architecture)
PM-7 requires organizations to develop and maintain an enterprise architecture that integrates information security and privacy considerations across all organizational systems. Classification decisions cannot be made in isolation at the individual system level. They must align with the organization’s broader security architecture and risk management strategy. PM-7 ensures FIPS 199 categorization results flow through the entire enterprise, not just individual systems.
The categorization process itself is defined by FIPS 199. Organizations handling Controlled Unclassified Information (CUI) should note that data classification also intersects with NIST 800-171 requirements.
Higher education institutions and third-party servicers handling federal student aid data carry parallel obligations under the Department of Education FSA’s electronic announcement on protecting student information. EDUCAUSE’s NIST SP 800-171 overview maps the practical implications for colleges and universities. See our guide on CUI/FCI data scoping for more on that relationship.
FIPS 199 Impact Levels (Low, Moderate, High)
FIPS 199 defines three impact levels, Low, Moderate, and High, based on the potential impact to an organization if its information or systems were compromised across three security objectives: confidentiality, integrity, and availability.
Published by National Institute of Standards and Technology (NIST) in 2004 as a companion standard to FIPS 200 (Minimum Security Requirements for Federal Information and Information Systems), FIPS 199 provides the categorization foundation that feeds directly into NIST 800-53 control selection.
| Impact Level | Definition | Example |
|---|---|---|
| Low | Loss could have a limited adverse effect on organizational operations, assets, or individuals | A university’s public website or course catalog |
| Moderate | Loss could have a serious adverse effect on organizational operations, assets, or individuals | Student financial records, employee HR data, grant management systems |
| High | Loss could have a severe or catastrophic adverse effect on organizational operations, assets, or individuals | Research systems handling classified or export-controlled data |
The CIA Triad
FIPS 199 assesses each system against three security objectives, commonly referred to as the CIA triad:
- Confidentiality: Preserving authorized restrictions on information access and disclosure
- Integrity: Guarding against improper information modification or destruction
- Availability: Ensuring timely and reliable access to information and systems
The High-Water Mark
Each system is assessed against all three security objectives independently. The overall system categorization takes the highest impact level across them, called the high-water mark. If a system is Low for confidentiality but Moderate for integrity, the system is categorized as Moderate overall.
NIST SP 800-60 provides a catalog of common information types pre-mapped to provisional impact levels, simplifying the categorization process. The NIST RMF Quick Start Guide for the Categorize step walks through how provisional values from SP 800-60 are adjusted and finalized in practice.
Once impact level is determined, the next step is mapping it to a control baseline.
How Classification Determines Control Baselines
Once a system is categorized using FIPS 199, the impact level maps directly to one of three NIST 800-53 control baselines defined in NIST SP 800-53B, each specifying a different set of mandatory controls. They represent the minimum security requirements organizations must meet based on their categorization.
| Baseline | Controls | Common Use Cases |
|---|---|---|
| Low | ~149 | Public websites, non-sensitive internal tools |
| Moderate | ~287 | Student information systems, financial systems, email (most commonly applied baseline in federal agencies) |
| High | ~370 | National security systems, classified research environments |
Each higher baseline builds on the one below it. A Moderate system implements all Low-baseline controls (149) plus additional requirements. A High system adds further controls on top of Moderate. This cumulative structure means moving up a baseline level extends what is already in place.
Different communities apply categorization differently. National Security Systems follow CNSS Instruction No. 1253, which adopts FIPS 199’s three-component CIA categorization and replaces the high-water mark with a trigraph (e.g., M-M-H) that drives more granular control selection. Cloud service providers serving federal agencies follow the FedRAMP PMO guidance on baselines and impact levels, which maps FIPS 199 categorizations directly to FedRAMP Low, Moderate, and High control sets.
Tailoring Your Baseline
The baseline is a starting point that organizations refine for their environment. NIST SP 800-53B provides tailoring guidance that allows organizations to adjust their baseline in two directions:
- Add controls where a risk assessment identifies threats not addressed by the baseline.
- Remove controls that are not applicable to their environment or mission.
All tailoring decisions must be documented and justified. Critical infrastructure owners and federal contractors also map NIST 800-53 baselines against CISA’s Cross-Sector Cybersecurity Performance Goals 2.0, which align with NIST CSF 2.0 and SP 800-53 to define a prioritized federal baseline for entities outside FISMA’s direct scope.
FIPS 200 establishes the minimum security requirements that formally connect FIPS 199 categorization to 800-53 control selection, ensuring the tiered approach holds from classification through implementation. The connection is direct: classify your data, determine your impact level, and the baseline tells you which controls to implement.
Practical Data Classification Approach
Classifying data in practice starts with knowing what data exists and where it lives. A comprehensive inventory is the prerequisite for effective FIPS 199 categorization.
Step 1: Inventory Your Information Types and Systems
Organizations cannot classify what has not been identified. Before applying FIPS 199, they need a complete picture of the information they process, store, and transmit across all systems. See our guide to IT asset inventory management for how to approach this step.
Step 2: Map Information Types to Security Categories
NIST SP 800-60 provides a catalog of common information types pre-mapped to provisional impact levels across confidentiality, integrity, and availability. Use it as a starting point to assign impact levels to each information type a system handles.
Step 3: Apply the FIPS 199 high-water mark
For each system, take the highest impact level across all information types it processes. A system handling both Low and Moderate information types is categorized as Moderate overall.
Step 4: Document in the system security plan.
RA-2 requires the categorization results and supporting rationale to be documented in the SSP and approved by the authorizing official. Categorization must also be maintained and revisited as systems and data evolve. After categorization and control selection, NIST SP 800-53A Rev. 5 provides the formal assessment methodology that carries the program through control assessment and authorization.
Common Pitfalls
Over-classifying, meaning labeling everything High, increases cost and implementation burden without a corresponding reduction in risk. Under-classifying creates gaps that leave systems inadequately protected. In higher education, student records, financial aid data, research data, and public course information each warrant different categorization levels. The GAO’s June 2024 report on persistent federal cybersecurity challenges documents how inconsistent categorization and incomplete baseline implementation continue to drive compliance gaps across federal agencies.
How to Simplify NIST 800-53 Data Classification
NIST 800-53 data classification breaks down when inventory data lives in disconnected spreadsheets, FIPS 199 categorizations get documented once and never revisited, and the link between information types and applicable controls is rebuilt manually for every audit.
Isora GRC is the collaborative GRC Assessment Platform™ that gives security teams one shared workspace to run assessments, manage vendors and assets, track live risks, and publish audit-ready reports.
A unified inventory of systems, applications, and vendors carries data classification, ownership, and assessment context as metadata on every record. FIPS 199 categorizations live alongside the systems they apply to, not in a separate document, so impact levels stay current as inventory updates flow through the assessment workflow.
Assessments scope to systems based on their categorization, and findings flow back to the inventory with full lineage from questionnaire item to mapped control to system of record. This connects RA-2 categorization decisions to the controls organizations actually implement, eliminating the manual mapping step that makes audit trails fragile.
Explore NIST 800-53 compliance software, or for state and local agencies, IT risk management software for the public sector.
Streamline security GRC workflows with Isora GRC →
Key Takeaways
Data classification is the entry point to NIST 800-53. FIPS 199 categorization sets a system’s impact level (Low, Moderate, or High), and that level determines which of the three SP 800-53B control baselines applies: ~149, ~287, or ~370 controls. Get the categorization right and the rest of the program has a defensible foundation. Get it wrong, however, and every downstream control decision inherits the error.
For a comprehensive overview of all 20 control families and 1,196 controls, see the NIST 800-53 complete guide.
NIST 800-53 Data Classification FAQs
What is data classification in NIST 800-53?
Data classification in NIST 800-53 refers to the process of categorizing information and systems by impact level (Low, Moderate, or High) using FIPS 199. This categorization determines which control baseline an organization must implement: Low (~149 controls), Moderate (~287), or High (~370).
What is FIPS 199 and how does it relate to NIST 800-53?
FIPS 199 is the standard that defines how to categorize federal information systems by potential impact across confidentiality, integrity, and availability. It feeds directly into NIST 800-53 by determining which control baseline applies to a given system.
How many controls are in each NIST 800-53 baseline?
The Low baseline contains ~149 controls, Moderate contains ~287, and High contains ~370. Each higher baseline includes all lower-baseline controls plus additional requirements. NIST 800-53 Rev 5 contains 1,196 total controls across all 20 families.
What is the high-water mark in FIPS 199?
The high-water mark means a system’s overall categorization is determined by the highest impact level across all three security objectives. If a system is Low for confidentiality but Moderate for integrity, the system is categorized as Moderate overall.
Can a NIST 800-53 baseline be tailored?
Yes. NIST SP 800-53B provides tailoring guidance that allows organizations to add controls not in their baseline or remove controls that are not applicable, based on risk assessment results and mission requirements. All tailoring decisions should be documented.
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.
Dive into our research-backed resources–from product one pagers and whitepapers, to webinars and more–and unlock the transformative potential of powerfully simple GRC.
Learn More


















 Other Relevant Content
Other Relevant Content