Table of Contents
Table of Contents
- State Information Security Regulations: Complete Guide
- 50-State Information Security Regulations Reference Table
- Common Requirements in State Information Security Regulations
- State Information Security Regulations: Compliance Guides
- How to Simplify State Information Security Regulations Compliance
-
State InfoSec Requirement FAQs
- Which states have the most comprehensive state information security regulations?
- Do federal cybersecurity requirements override state information security regulations?
- How do I determine which state information security regulations apply?
- Can compliance with NIST CSF satisfy state information security regulations?
- How often do state cybersecurity regulations change?
- What is the relationship between state privacy laws and information security regulations?
State Information Security Regulations: Complete Guide
Across the U.S., all fifty state governments have issued their own state information security regulations. As a result, many organizations must navigate a patchwork of unique compliance requirements, often without practical guidance.
This guide provides a clear overview of state information security regulations to help GRC (governance, risk, and compliance) professionals understand the regulatory landscape, specific requirements, and how to comply. It includes a 50-state reference table of information security statutes and policies, common requirements for regulations across states, and state-specific compliance guidance.
50-State Information Security Regulations Reference Table
The following table provides a comprehensive reference of state information security regulations, statutes, policies, and frameworks across all 50 U.S. states. Use this as a starting point for identifying which regulations may apply to your organization.
| State | Statute/Policy | Description | Guide |
|---|---|---|---|
| Alabama | Code of Alabama § 41-28 (Office of Information Technology) | Establishes the Office of Information Technology and grants the Secretary of Information Technology authority to adopt binding rules, policies, procedures, and standards for the management and operation of information technology by state agencies. | — |
| Alaska | Administrative Order No. 284 (2017) | Establishes the Office of Information Technology (OIT) within the Department of Administration as the centralized authority for IT and cybersecurity governance in the executive branch. | — |
| Arizona | Statewide Policy 8120 Information Security Program | Establishes state information security program and responsibilities for state agencies. | Arizona P8000 Guide → |
| Arkansas | Cybersecurity Policy (Shared Administrative Services/Office of State Technology) | Defines the operational framework, procedures, and standards for securing Arkansas state systems, aligned with NIST CSF, applying to all users of state IT systems including contractors and vendors. | — |
| California | SIMM 5300-A/B Information Security Standards | Statewide Information Management Manual establishing security standards for state agencies. | California SIMM 5300 Guide → |
| Colorado | 8 CCR 1501-5 (Rules in Support of the Colorado Information Security Act) | Implements the Colorado Information Security Act by requiring each public agency to develop, maintain, and annually submit a Cyber Security Plan to the State CISO. | — |
| Connecticut | Sec. 4d-8a (Information and telecommunications systems for state agencies) | Establishes the Office of Policy and Management as the statewide authority responsible for developing and implementing information security and telecommunications policies for executive branch agencies. | — |
| Delaware | State of Delaware Information Security Policy (Title 29 Chapter 90C §9004C) | Establishes mandatory information security standards for all state agencies and external users, requiring annual compliance certification to the DTI CSO. | — |
| Florida | Florida Cybersecurity Act (§ 282.318, F.S.) | Mandates statewide cybersecurity standards for state agencies, including risk assessments, incident reporting, NIST-aligned safeguards, and enterprise governance under the Florida Digital Service. | Florida Cybersecurity Act Guide → |
| Georgia | Enterprise Information Security Policy (PS-08-005) | Establishes a security governance structure requiring all executive branch agencies to develop and maintain an internal information security program compliant with GTA’s minimum standards. | — |
| Hawaii | Hawaii Revised Statutes § 27-43.5 | Authorizes the Office of Enterprise Technology Services to set and enforce mandatory security standards, conduct audits, and direct remedial actions for all Executive Branch departments. | — |
| Idaho | ITS Information Security Policy Manual v4.0 | Establishes a comprehensive, NIST-based Information Security Management System (ISMS) to protect the confidentiality, integrity, and availability of Idaho data and information systems. | — |
| Illinois | DoIT Overarching Enterprise Information Security Policy | Establishes the minimum security controls for all State of Illinois Information Systems, applying to all agencies, employees, contractors, and third parties utilizing state IT resources. | — |
| Indiana | Senate Enrolled Act 472 (SEA 472) | Establishes statewide requirements for public entities to adopt cybersecurity and technology resource policies by 12/31/2027, directing the Indiana Office of Technology to develop implementing standards. | — |
| Iowa | Information Security Standard (OCIO) | Establishes minimum computer security requirements for state systems and central units of state government. | — |
| Kansas | ITEC 7000-P IT Enterprise Security Policy | Statewide policy requiring all Executive Branch Entities to implement and maintain IT security policies at least as stringent as this policy, authorized by K.S.A. 75-7238 and 75-7203. | — |
| Kentucky | CIO-091: Enterprise Information Security Program Policy | Establishes the Commonwealth’s Enterprise Information Security Program, mandating security controls aligned with NIST SP 800-53 Rev 5 moderate baseline for executive branch agencies. | — |
| Louisiana | Louisiana Information Security Policy (DoA) | Sets forth information security policies for accessing, protecting, managing, storing, transmitting, and distributing data to ensure availability, integrity, authenticity, and confidentiality. | — |
| Maine | Maine OIT Information Security Policy | Establishes minimum benchmarks to protect the security of State Information Assets under the purview of the Chief Information Officer. | — |
| Maryland | Maryland Department of IT Security Manual (v 1.2) | Establishes mandatory information security requirements for executive departments and independent state agencies to protect Maryland Information Systems and state-owned data. | — |
| Massachusetts | Information Security Governance Policy (ISP.001) | Establishes mandatory minimum information security requirements for executive branch agencies under the authority of EOTSS pursuant to M.G.L. c. 7D. | — |
| Michigan | Policy 1340.00 Information Technology Information Security | Establishes mandatory, NIST-aligned information security requirements for Michigan Executive Branch departments, agencies, boards, and commissions. | — |
| Minnesota | Information Security Program Standard | Establishes a mandatory, enterprise-wide information security program for Minnesota executive branch entities, authorizing the State CISO to set policies and oversee incident response. | — |
| Mississippi | Enterprise Security Policy (Title 36 Part 1) | Establishes minimum, enterprise-wide cybersecurity requirements for Mississippi state agencies under the authority of the Mississippi Department of Information Technology Services. | — |
| Missouri | Office of Cyber Security (OCS) Information Security Policy | Provides statewide, enterprise-approved guidance defining the structure and minimum expectations for agency-level information security policies aligned with NIST standards. | — |
| Montana | Montana Operations Manual Information Security Policy | Statewide information security policy requiring Montana state agencies to implement NIST-aligned controls to protect state information and information systems. | — |
| Nebraska | Nebraska Information Technology Commission – Information Security Policy (Chapter 8) | Establishes mandatory, statewide information security requirements for Nebraska state agencies, aligned with NIST standards and enforced through the Office of the CIO and SISO. | — |
| Nevada | State Information Security Program Policy | Defines the State of Nevada’s enterprise information security program and mandatory baseline controls for Executive Branch agencies, enforced through EITS pursuant to NRS 242.101. | — |
| New Hampshire | Information Security and Privacy Program Policy | Establishes New Hampshire’s statewide information security and privacy program for Executive Branch agencies, requiring a risk-based, NIST-aligned approach. | — |
| New Jersey | Statewide Information Security Manual (SISM) | Statewide information security and privacy manual mandating NIST-aligned controls for Executive Branch agencies and authorized third parties. | — |
| New Mexico | Cybersecurity Act (NMSA 1978 §§ 9-27A-1 to 9-27A-5) | Establishes the Office of Cybersecurity as the statewide authority responsible for developing standards, coordinating cybersecurity efforts, and improving posture across state government. | — |
| New York | NYS ITS Information Security Policy (NYS-P03-002) | Defines mandatory minimum information security requirements for all state entities, employees, and third parties using or accessing IT resources for which the state has administrative responsibility. | — |
| North Carolina | Statewide Information Security Manual (SISM) | Foundation for IT security establishing statewide standards based on NIST SP 800-53, with optional adoption by local entities. | North Carolina SISM Guide → |
| North Dakota | N.D. Cent. Code § 54-59-09 (Information technology standards) | Requires the North Dakota Information Technology Department and Office of Management and Budget to establish statewide IT policies, standards, and guidelines. | — |
| Ohio | ITS-SEC-02 Enterprise Security Controls Framework | Sets statewide minimum information-security requirements for executive-branch agencies using NIST SP 800-53 Rev. 4 as the foundational control framework. | Ohio ORC 9.64 Guide → |
| Oklahoma | State of Oklahoma Information Security Policy, Procedures and Guidelines (PPG) | Compiles and enforces minimum mandatory standards for the protection of all state information assets across state agencies, as required by 62 O.S. sections §34.11.1 through 34.33. | — |
| Oregon | Cyber and Information Security Statewide Policy (107-004-052) | Establishes a unified statewide cyber and information security program requiring Oregon Executive Branch agencies to implement baseline security controls under the State CIO’s authority. | — |
| Pennsylvania | Executive Order 2016-06 – Enterprise Information Technology Governance | Establishes centralized statewide IT and cybersecurity governance by designating OA/OIT as the Commonwealth’s authority for security policy and enterprise standards. | Pennsylvania EO 2016-06 Guide → |
| Rhode Island | Security and Risk Program Management Policy (ETSS_PM-1) | Establishes a statewide information security program and standards framework for executive branch agencies, directing the CISO to implement consistent practices for IT assets and data protection. | — |
| South Carolina | Information Security Program Master Policy (v1.2) | Creates a statewide information security governance framework mandating agency security plans, risk management, and NIST-aligned controls under DIS oversight. | — |
| South Dakota | IT Security Policy (Bureau of Information and Technology) | Provides a comprehensive set of cyber security policies detailing acceptable practices for use of State of South Dakota IT resources, also applying to local governments and educational institutions. | — |
| Tennessee | Enterprise Information Security Policy — Strategic Technology Solutions (STS) | Establishes statewide minimum information-security requirements for all Tennessee executive-branch agencies and third parties handling state data, based on ISO 27000 standards. | — |
| Texas | TAC Title 1 Part 10 Chapter 202 | Texas Administrative Code establishing information security standards for state agencies. | Texas TAC 202 Guide → |
| Utah | Utah Code § 63A-16-205 – CIO Rulemaking and Security Policies | Authorizes the Chief Information Officer to establish mandatory statewide standards and policies for executive-branch state agencies. | — |
| Vermont | Vermont Information Security Foundations Policy | Defines baseline information-security requirements for executive-branch agencies, establishing a NIST-aligned framework and minimum safeguards for state systems. | — |
| Virginia | Commonwealth Information Security Standard (SEC530.01.1) | Commonwealth-wide information security standard defining minimum baseline controls for executive-branch agencies under the statewide program established by SEC519. | Virginia SEC530 Guide → |
| Washington | Washington State Cybersecurity Program Policy (SEC-01) | Outlines requirements for state agencies to manage cybersecurity risks and ensure compliance with WaTech policies, including agencies headed by separately elected officials. | — |
| West Virginia | WVOT-PO1001 Information Security Policy | Establishes objectives and responsibilities for state agencies regarding information security, issued by the West Virginia Office of Technology. | — |
| Wisconsin | IT Security Policy Handbook | Defines statewide information-security policies and mandates NIST SP 800-53 Rev. 5 aligned controls for all executive-branch state agencies. | Wisconsin IT Security Guide → |
| Wyoming | Wyoming Data Policies (W.S. 9-21-101) | Requires executive-branch agencies to adopt data-security policies addressing collection, access, safeguards, and incident response in accordance with CIO standards. | — |
Common Requirements in State Information Security Regulations
Earlier state information security regulations focused on technical controls like encryption, access controls, and network security. However, more recent frameworks put greater weight on governance, risk management, and organizational accountability.
Specific requirements vary by state. That said, most comprehensive state information security regulations address the following areas:
| Requirement Area | Common Elements |
|---|---|
| Governance | Designated security officer, written policies, executive oversight |
| Risk Assessment | Periodic risk assessments, documented methodology, risk registers |
| Access Controls | Authentication requirements, least privilege, access reviews |
| Data Protection | Encryption standards, data classification, retention policies |
| Incident Response | Response plans, notification procedures, post-incident review |
| Vendor Management | Due diligence requirements, contractual provisions, ongoing monitoring |
| Training | Security awareness programs, role-based training, regular updates |
| Audit & Monitoring | Logging requirements, monitoring capabilities, periodic audits |
State Information Security Regulations: Compliance Guides
Most state information security regulations tell you what to do, but not how to do it. The following guides break down specific state frameworks with practical compliance guidance for GRC teams.
Arizona P8000
Arizona’s P8000 Information Security Policy Series covers security, privacy, and supply-chain risk. It addresses the expanding threat landscape, protects sensitive state data, and manages risks from modern digital services. Within this series, the P8120 Information Security Policy defines the statewide program that every agency must implement.
Explore the Arizona P8000 guide →
California SIMM 5300
California’s Statewide Information Management Manual (SIMM) 5300 series establishes information security requirements for state agencies. In addition, CCPA/CPRA create significant privacy and security obligations for businesses.
View the California SIMM 5300 guide →
Florida Cybersecurity Act
Florida’s Cybersecurity Act, under Florida Statutes (§ 282.318, F.S.), sets mandatory cybersecurity standards for state agencies. It covers governance, operational requirements, and oversight structures aligned with the NIST Cybersecurity Framework. The Local Government Cybersecurity Act (§ 282.3185, F.S.) extends similar obligations to counties and municipalities. Together with the Florida Cybersecurity Standards (Chapter 60GG-2, F.A.C.), these laws define how public sector organizations manage cybersecurity risk.
See the Florida Cybersecurity Act guide →
North Carolina SISM
North Carolina’s Statewide Information Security Manual (SISM) provides a framework for governance, accountability, and continuous improvement. It defines the minimum cybersecurity requirements that every agency, department, and institution must follow as part of the state’s digital government platform.
Learn about the North Carolina SISM guide →
Ohio ORC 9.64
Ohio’s ORC § 9.64 is the state’s first law requiring local governments to establish formal cybersecurity programs. It applies to counties, municipalities, townships, and special districts. Its purpose is to safeguard public data and IT systems across the state.
Review the Ohio compliance guide →
Pennsylvania EO 2016-06
Pennsylvania’s information security governance operates under Executive Order 2016-06 through three core entities. Each entity plays a distinct role in defining, executing, and enforcing enterprise IT strategy. Because a Governor-issued Executive Order maintains this structure, the state can respond to evolving threats without delay.
Explore the Pennsylvania guide →
Texas TAC 202
Texas Administrative Code Title 1, Part 10, Chapter 202 establishes information security standards for state agencies and higher education institutions. It sets minimum standards to protect sensitive data and effectively manage risks.
View the Texas TAC 202 guide →
Virginia SEC530
Virginia’s SEC530 defines minimum baseline requirements for information security and risk management across state agencies. Specifically, it outlines security controls, governance structures, and procedures for protecting data and systems.
See the Virginia SEC530 guide →
Wisconsin IT Security Standards
Wisconsin’s IT Security Policy Handbook and the IT Security Standards Handbook define cybersecurity accountability. They cover which policies agencies must implement and how to translate policies into security controls, assess vendors, and respond to incidents.
How to Simplify State Information Security Regulations Compliance
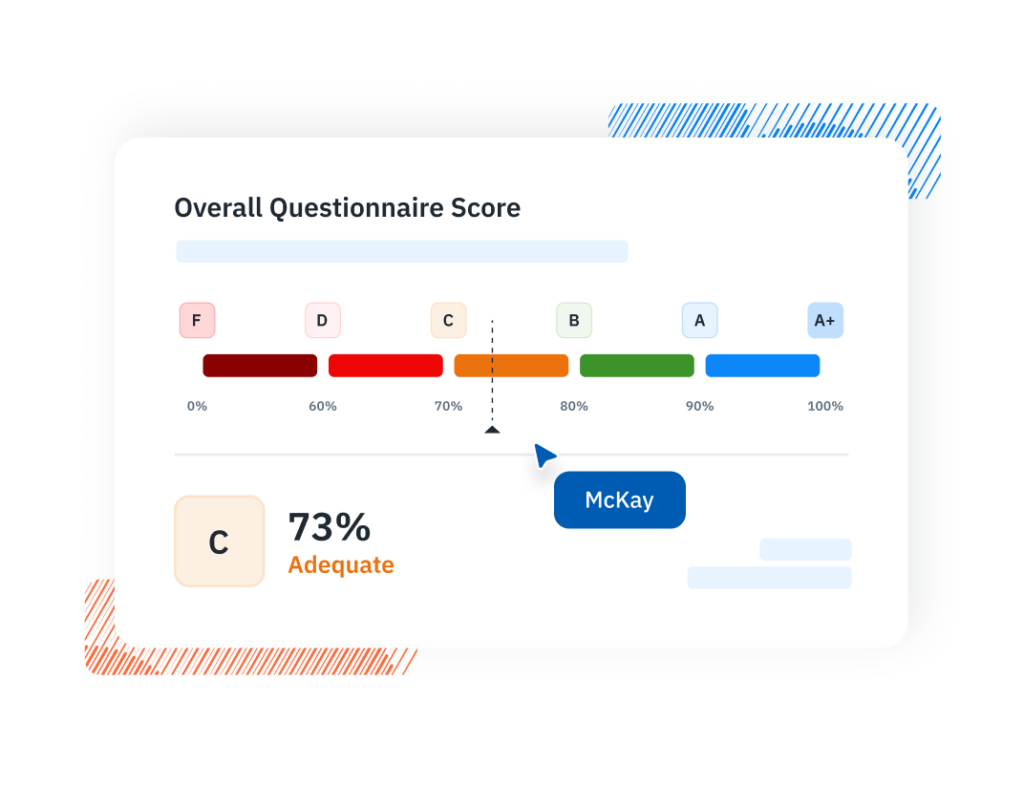
Managing compliance across multiple state information security regulations demands systematic processes. These include risk assessment, control implementation, policy management, and continuous monitoring. With platforms like Isora GRC, organizations subject to state cybersecurity regulations can:
- Map controls across frameworks: Align state-specific requirements with federal frameworks (NIST SP 800-53, NIST CSF, HIPAA, GLBA) to identify overlaps and gaps
- Automate risk assessments: Conduct and track periodic risk assessments required by state regulations
- Manage vendor risk: Document third-party due diligence and monitor ongoing vendor compliance
- Track policy compliance: Distribute, track acknowledgment, and manage updates to security policies
- Generate compliance evidence: Produce documentation and reports for audits and regulatory examinations
- Maintain a risk register: Track identified risks, remediation status, and exception tracking
Simplify state cybersecurity compliance with Isora GRC
- Map controls across frameworks: Align state-specific requirements with federal frameworks (NIST SP 800-53, NIST CSF, HIPAA, GLBA) to identify overlaps and gaps
- Automate risk assessments: Conduct and track periodic risk assessments required by state regulations
- Manage vendor risk: Document third-party due diligence and monitor ongoing vendor compliance
- Track policy compliance: Distribute, track acknowledgment, and manage updates to security policies
- Generate compliance evidence: Produce documentation and reports for audits and regulatory examinations
- Maintain a risk register: Track identified risks, remediation status, and exception tracking
Simplify state cybersecurity compliance with Isora GRC →
State InfoSec Requirement FAQs
Which states have the most comprehensive state information security regulations?
California SIMM 5300 and Florida’s Cybersecurity Act are particularly detailed. However, what counts as “most comprehensive” depends on the sector. For example, financial services, healthcare, and government entities all face different regulatory landscapes.
Do federal cybersecurity requirements override state information security regulations?
Generally, no. Organizations must comply with both federal and state requirements. In some cases, federal law may preempt specific state provisions. However, this is the exception rather than the rule. As a result, most organizations need to meet the most stringent requirement across all jurisdictions.
How do I determine which state information security regulations apply?
Applicability typically depends on several factors:
- Where your organization is physically located
- Where you have employees or operations
- Where your customers or clients reside
- What sectors you operate in (financial services, healthcare, government)
- What types of data you process
Can compliance with NIST CSF satisfy state information security regulations?
Many states reference or require alignment with NIST CSF. As a result, it serves as a strong foundation. However, some states have requirements beyond NIST CSF. In fact, many state information security regulations also borrow heavily from NIST 800-53. Therefore, organizations should verify specific state requirements before assuming CSF alone is sufficient.
How often do state cybersecurity regulations change?
State information security regulations change regularly. For example, major legislative sessions (typically annual or biennial) may introduce new requirements. Meanwhile, administrative agencies may update rules more frequently. As a result, organizations should monitor changes at least quarterly.
What is the relationship between state privacy laws and information security regulations?
State privacy laws (like CCPA, CPRA, and state consumer privacy acts) typically include security requirements as part of data protection obligations. Consequently, organizations must address both the privacy and security provisions of applicable laws.
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.