 Table of Contents
Table of Contents
- GLBA Cybersecurity: Complete Guide to the Safeguards Rule Requirements
- What Does GLBA Have to Do With Cybersecurity?
- Who Must Comply With GLBA Cybersecurity Requirements
- Where GLBA Defines Cybersecurity Requirements
- Encryption
- Multi-Factor Authentication (MFA)
- Access Controls
- Audit Logging and Monitoring
- Secure Development
- Penetration Testing and Vulnerability Assessments
- Incident Response
- GLBA Control Alignment with NIST CSF and CIS Controls
- How to Simplify GLBA Cybersecurity Requirements
- Key Takeaways
- GLBA Cybersecurity FAQs
GLBA Cybersecurity: Complete Guide to the Safeguards Rule Requirements
The Safeguards Rule requires financial institutions to protect the security, confidentiality, and integrity of customer information. It defines the cybersecurity controls institutions must implement to prevent unauthorized access, data breaches, and misuse of nonpublic personal information (NPI). These controls include encryption, multi-factor authentication, penetration testing, vulnerability assessments, access controls, audit logging, secure development practices, and incident response planning.
The Safeguards Rule is one of three rules under the Gramm-Leach-Bliley Act (GLBA). GLBA compliance requires financial institutions to follow the Safeguards Rule alongside the Privacy Rule, which governs privacy notices and information-sharing disclosures, and the Pretexting Provisions, which prohibit obtaining customer information through false pretenses.
In 2023, the Federal Trade Commission (FTC) strengthened the Safeguards Rule, transforming flexible guidance into mandatory cybersecurity requirements, defining explicit technical safeguards, and requiring institutions to regularly test and monitor those controls.
This guide explains each cybersecurity requirement with specific technical standards institutions must implement, how those requirements operate in practice, and how GLBA requirements align with established cybersecurity frameworks such as NIST CSF and CIS Controls.
What Does GLBA Have to Do With Cybersecurity?
GLBA is fundamentally a cybersecurity regulation. It establishes mandatory cybersecurity protections for financial customer data. Through the Safeguards Rule, every financial institution must create and maintain a written information security program (ISP) that protects customer information from unauthorized access, disclosure, or misuse.
GLBA cybersecurity requirements are the technical safeguards that financial institutions must implement under the FTC’s Safeguards Rule (16 CFR Part 314) to protect nonpublic personal information. Updated in 2023, these requirements now explicitly mandate encryption, multi-factor authentication, penetration testing, access controls, and incident response capabilities.
The Safeguards Rule protects three core pillars of customer information: security, confidentiality, and integrity. Security prevents unauthorized access, confidentiality prevents unauthorized disclosure, and integrity prevents unauthorized alteration. Cybersecurity controls are the primary mechanism for achieving all three.
Prescriptive Cybersecurity Requirements
When the original Safeguards Rule first took effect in 2003, it required organizations to maintain an information security program but allowed flexibility in how organizations implemented security controls.
The FTC’s 2021 amendments, finalized in 2021 and effective June 9, 2023, introduced explicit cybersecurity safeguards and testing requirements.
Key requirements now include:
- Mandatory encryption requirements. Customer information must be encrypted at rest and in transit.
- Required multi-factor authentication (MFA). MFA must protect access to systems containing customer information.
- Security testing obligations. Institutions must conduct annual penetration testing and periodic vulnerability assessments.
- Formal incident response planning. Organizations must maintain documented procedures for responding to security incidents affecting customer data.
- Expanded governance expectations. A qualified individual must oversee the security program and report regularly to senior leadership.
These changes bring GLBA closer to modern cybersecurity regulatory expectations.
Who Must Comply With GLBA Cybersecurity Requirements
GLBA cybersecurity requirements apply to any organization classified as a “financial institution” under the law. GLBA defines financial institutions based on activity, not charter type. Any organization that is “significantly engaged” in financial activities and collects or processes customer financial data typically falls within scope.
Covered entities include:
- Traditional financial institutions. Banks, credit unions, savings associations, insurance companies, and broker-dealers.
- Non-bank financial institutions. Mortgage brokers, payday lenders, auto dealers arranging financing, tax preparers, real estate settlement services, debt collectors, and similar businesses engaged in consumer financial transactions.
- Higher education institutions. Colleges and universities that administer Title IV federal student financial aid programs also qualify as financial institutions under GLBA. For a deeper explanation, see our guide on GLBA compliance in higher education.
Where GLBA Defines Cybersecurity Requirements
GLBA cybersecurity safeguards are defined in 16 CFR 314.4, which outlines the required elements of a financial institution’s information security program.
Most technical cybersecurity requirements appear in three parts of the rule:
- Element 3 (Safeguard design and implementation): Defines security controls institutions must deploy to protect customer data.
- Element 4 (Testing and monitoring): Requires regular testing of safeguards through penetration testing and vulnerability assessments.
- Element 8 (Incident response): Requires institutions to maintain a documented plan for detecting and responding to security events.
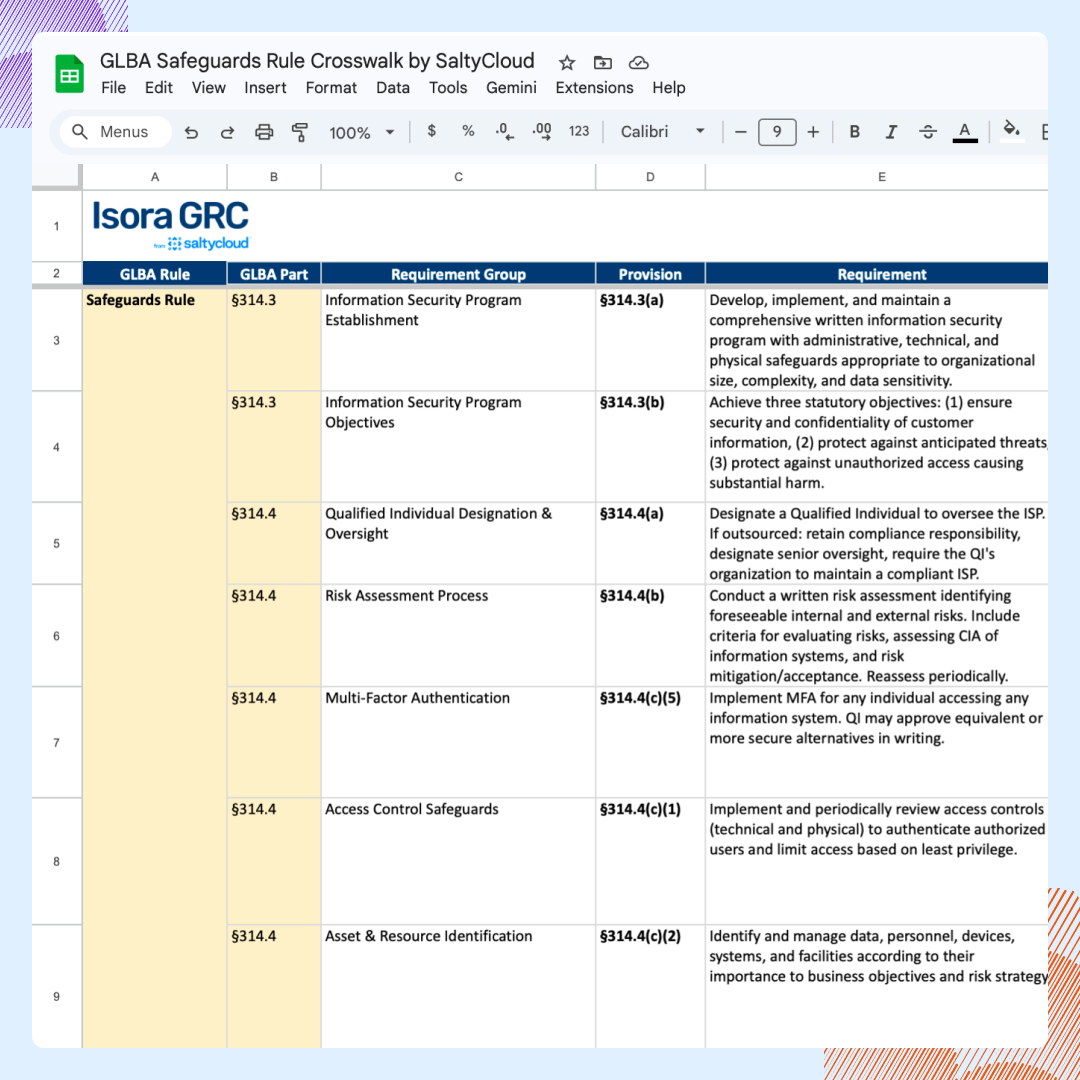
The table below summarizes the core GLBA cybersecurity safeguards.
| Cybersecurity Requirement | Description | What It Protects | Safeguard Rule Section | Safeguard Rule Element | Frequency |
| Encryption | Encrypt nonpublic personal information (NPI) at rest and in transit. | Customer financial data stored or transmitted across systems | 16 CFR 314.4(c)(3) | Element 3: Safeguard design and implementation | Continuous |
| Multi-Factor Authentication (MFA) | Require MFA for individuals accessing systems containing customer information. | System access to environments containing NPI | 16 CFR 314.4(c)(5) | Element 3: Safeguard design and implementation | Continuous |
| Access Controls | Restrict system access based on role and business need (the principle of least privilege). | Unauthorized access to customer information | 16 CFR 314.4(c)(1) | Element 3: Safeguard design and implementation | Continuous |
| Audit Logging and Monitoring | Maintain logs that record authentication events, system access, and security activity. | Detection of unauthorized access or misuse of systems | 16 CFR 314.4(c)(8) | Element 3: Safeguard design and implementation | Continuous |
| Secure Development Practices | Implement secure coding practices and security testing for internally developed systems. | Applications storing or processing NPI | 16 CFR 314.4(c)(4) | Element 3: Safeguard design and implementation | Continuous |
| Penetration Testing | Conduct penetration testing to identify exploitable weaknesses. | System vulnerabilities that could expose customer data | 16 CFR 314.4(d)(2) | Element 4: Testing and monitoring | At least annually |
| Vulnerability Assessments | Perform vulnerability scans across infrastructure and applications. | Known security vulnerabilities across systems | 16 CFR 314.4(d)(2) | Element 4: Testing and monitoring | At least every 6 months |
| Incident Response Plan | Maintain a written incident response plan for security events affecting customer information. | Detection and response to security incidents | 16 CFR 314.4(h) | Element 8: Incident response | Maintained continuously and tested periodically |
Encryption
The Safeguards Rule requires encryption of all customer information both at rest (stored data) and in transit (transmitted data) under 16 CFR 314.4(c)(3).
The rule does not name a single encryption standard, but FTC enforcement actions and industry guidance point to AES-256 for stored data and TLS 1.2+ for data transmitted across networks.
Where Encryption Applies
Encryption applies wherever systems store or transmit NPI, including databases, backups, portable devices, and transmission channels that contain or transmit nonpublic personal information (NPI).
Common Implementation Practices
Financial institutions typically implement encryption through:
- Full-disk encryption on endpoints and servers containing NPI
- Database-level or field-level encryption for sensitive data stores
- TLS 1.2 or higher for websites, API integrations, and email systems handling NPI
- Secure transmission methods for sharing NPI with consumers and third parties
- Encryption for offsite and cloud backups
Common Compliance Gaps
Encryption gaps often appear in legacy or overlooked systems. Common places are:
- Unencrypted backup media
- Internal applications still using HTTP
- Unencrypted portable devices (laptops, USB drives)
- Legacy systems that do not support current encryption standards.
Multi-Factor Authentication (MFA)
The 2023 update explicitly requires multi-factor authentication (MFA) for any individual accessing information systems containing customer information under 16 CFR 314.4(c)(5).
Where MFA Applies
MFA applies broadly. It is not limited to remote administrators or privileged users. All user access to systems containing NPI, including remote access, administrative access, email systems with NPI, database access, cloud services storing customer data, and VPN connections to internal networks.
Both employees and third-party service providers must use MFA when accessing systems containing customer information.
Acceptable MFA Factors
Authentication must combine at least two factors from different categories:
- Something you know (password or PIN)
- Something you have (hardware token, authenticator app, SMS code)
- Something you are (biometric factor)
Hardware tokens and authenticator apps are generally stronger than SMS-based codes because SMS remains vulnerable to SIM-swapping attacks.
Access Controls
Financial institutions must restrict access to customer information under 16 CFR 314.4(c)(1). Access should follow the principle of least privilege, allowing users to access only the data necessary for their role. Their permissions must also be reviewed periodically to ensure that outdated privileges do not expose customer data.
Implementation Requirements
- Role-based access control (RBAC) with clearly defined roles and permissions
- Regular access reviews to confirm permissions remain appropriate (quarterly is recommended best practice)
- Immediate removal of access for terminated employees or contractors
- Privileged access management (PAM) for administrative accounts
- Logging of all access to systems containing NPI
Audit Logging and Monitoring
Financial institutions must maintain logs that detect unauthorized access, misuse of systems, or attempts to tamper with customer information under 16 CFR 314.4(c)(8).
Logging Requirements
- Logging controls should capture key security events such as user authentication attempts, successful and failed login events, access to systems containing nonpublic personal information (NPI), privilege escalation or role changes, and any modification or deletion of data.
- The logs must be retained long enough to support investigations, regulatory reviews, and forensic analysis. Many organizations retain logs for at least one year.
- Security teams must also actively monitor and analyze logs to detect suspicious activity.
Secure Development
Financial institutions must evaluate and implement secure coding practices for in-house applications that store, process, or transmit customer information, including code reviews, static and dynamic application security testing, and secure software development lifecycle (SDLC) practices as required under 16 CFR 314.4(c)(4).
Typical safeguards include:
- Secure software development lifecycle (SSDLC) processes
- Code reviews for security vulnerabilities
- Static application security testing (SAST)
- Dynamic application security testing (DAST)
- Dependency and library vulnerability scanning
Penetration Testing and Vulnerability Assessments
Institutions must conduct annual penetration testing and vulnerability assessments at least every six months to identify weaknesses that could expose customer information. Vulnerabilities identified during testing should be remediated according to the organization’s risk management process.
Penetration Testing
Penetration testing simulates real-world attacks against systems to identify exploitable weaknesses. Typical simulations involve:
- External network penetration testing against internet-facing systems
- Internal network penetration testing to evaluate lateral movement risks
- Web application testing for customer-facing applications that process NPI
- Social engineering testing (recommended best practice, not explicitly required)
Vulnerability Assessments
Vulnerability assessments identify known security weaknesses across the technology environment. A typical assessment scope includes:
- Network vulnerability scanning across all systems, servers, and endpoints.
- Configuration review for servers, databases, and network devices
- Patch management verification
- Cloud infrastructure scanning
Test results must be documented and findings must be remediated. Use the GLBA compliance checklist to track testing schedules and remediation status.
Incident Response
Financial institutions must maintain a written incident response plan under 16 CFR 314.4(h). The plan must define procedures for detecting, responding to, and recovering from security incidents affecting customer information.
Incident Response Plan Requirements
The incident response plan must include:
- Goals and scope of the incident response program
- Internal processes for detecting and responding to security events
- Clear roles and responsibilities for the incident response team
- Communication and notification procedures for internal teams and external stakeholders
- Remediation steps for containing and recovering from a breach
- Documentation and reporting requirements
- Post-incident analysis to prevent recurrence
Institutions must maintain the plan continuously and test it periodically through tabletop exercises or simulations.
FTC Breach Notification Requirement
The FTC’s October 2023 amendment introduced breach notification requirements under the Safeguards Rule. Financial institutions must notify the FTC within 30 days of discovering a breach affecting 500 or more consumers.
For complete notification requirements, see our GLBA data breach notification guide.
GLBA Control Alignment with NIST CSF and CIS Controls
Organizations already implementing the NIST Cybersecurity Framework (CSF) or CIS Controls will find significant overlap with GLBA cybersecurity requirements.
For a deeper explanation of how the framework works, see our NIST CSF complete guide.
| GLBA Requirement | Safeguards Rule Section | NIST CSF Function | CIS Control |
| Risk Assessment | 16 CFR 314.4(b) | Identify (ID.RA) | CIS 16: Application Software Security |
| Access Controls | 16 CFR 314.4(c)(1) | Protect (PR.AA) | CIS 6: Access Control Management |
| Encryption | 16 CFR 314.4(c)(3) | Protect (PR.DS) | CIS 3: Data Protection |
| MFA | 16 CFR 314.4(c)(5) | Protect (PR.AA) | CIS 6: Access Control Management |
| Audit Logging | 16 CFR 314.4(c)(8) | Protect (PR.PS) | CIS 8: Audit Log Management |
| Penetration Testing | 16 CFR 314.4(d)(2) | Identify (ID.IM) | CIS 18: Penetration Testing |
| Vulnerability Assessments | 16 CFR 314.4(d)(2) | Identify (ID.RA) | CIS 7: Continuous Vulnerability Management |
| Incident Response | 16 CFR 314.4(h) | Respond (RS.MA) | CIS 17: Incident Response Management |
GLBA is a federal law enforced by regulators including the FTC. Violations carry fines and enforcement actions. NIST CSF and CIS Controls are voluntary frameworks — organizations adopt them as guidance unless a regulation or contract requires them. Mapping existing framework controls to GLBA requirements reduces duplicated effort but does not replace Safeguards Rule compliance.
For a detailed crosswalk between the Safeguards Rule and established frameworks, see the GLBA Safeguards Rule Requirements Crosswalk.
How to Simplify GLBA Cybersecurity Requirements
GLBA cybersecurity safeguards touch many parts of the organization. Encryption lives in infrastructure, MFA sits in identity systems, penetration testing happens in security programs, and incident response spans the entire organization. Keeping visibility across all of that requires more than scattered spreadsheets and email threads. Isora GRC brings these moving pieces into one place.
- Assessment Management. Send cybersecurity control assessments directly to IT teams and unit owners. Infrastructure teams confirm encryption controls, identity teams verify MFA, and security teams document testing practices. Responses and evidence come back into one workspace instead of disappearing across inboxes.
- Risk Management. Capture assessment gaps immediately in a centralized risk register. Missing MFA, outdated encryption, or incomplete logging becomes a tracked risk with an owner and remediation plan. Monitor progress until the safeguard is implemented.
- Reports and Scorecards. Turn assessment results into clear compliance views. See which GLBA safeguards are implemented, where controls are incomplete, and what remediation is underway. Security leaders and auditors get a straightforward picture of the organization’s cybersecurity posture.
See how Isora GRC simplifies GLBA compliance →
Key Takeaways
Under the GLBA Safeguards Rule, all financial institutions must encrypt NPI at rest and in transit, enforce MFA for all system access, implement role-based access controls, and maintain audit logging across all systems containing customer information.
That includes mandatory annual penetration testing and biannual vulnerability assessments, with findings that are documented and remediated. It also includes a written incident response plan that must be maintained continuously and tested periodically. Additionally, breaches affecting 500+ consumers require FTC notification within 30 days.
Organizations already using NIST CSF or CIS Controls can map existing controls to GLBA requirements, but Safeguards Rule compliance requires independent verification. Ultimately, compliance is not a one-time exercise — continuous monitoring, regular testing, and ongoing safeguard updates are required.
For the full Safeguards Rule framework, see the GLBA Safeguards Rule guide. For a step-by-step compliance process, see the GLBA compliance checklist.
See how Isora GRC simplifies GLBA compliance →
GLBA Cybersecurity FAQs
What cybersecurity requirements does GLBA mandate?
The Safeguards Rule requires financial institutions to protect nonpublic personal information (NPI) using specific safeguards defined in 16 CFR 314.4. These safeguards include encryption, multi-factor authentication, access controls, audit logging, secure development practices, regular security testing (penetration testing and vulnerability assessments), and a written incident response plan to prevent unauthorized access to customer information systems and data.
Does GLBA require encryption?
Yes. The Safeguards Rule (effective June 2023) requires financial institutions to encrypt customer information both at rest and in transit. If encryption is not feasible, the institution must document why and implement approved compensating controls. Most organizations use AES-256 for stored data and TLS 1.2 or higher for data in transit.
Does GLBA require penetration testing?
Yes. Under 16 CFR 314.4(d)(2), the Safeguards Rule requires institutions to test the effectiveness of their safeguards. Institutions must either conduct annual penetration testing with vulnerability assessments at least every six months, or implement continuous monitoring that includes regular vulnerability assessments.
Is MFA required under GLBA?
Yes. The 2023 Safeguards Rule update explicitly requires MFA (multi-factor authentication) for any individual accessing information systems containing customer information.
How does GLBA relate to NIST Cybersecurity requirements?
GLBA cybersecurity requirements overlap significantly with the NIST Cybersecurity Framework (CSF). Organizations already implementing NIST CSF can map existing controls to GLBA requirements to reduce duplicated effort. The key difference: GLBA compliance is legally mandatory.
What happens when financial institutions fail to meet GLBA cybersecurity requirements?
Financial institutions that fail to implement the GLBA cybersecurity requirements can face penalties up to $100,000 per violation, and officers and directors can face individual fines up to $10,000 per violation and up to 5 years imprisonment for willful violations. See our GLBA penalties and enforcement guide for details.
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.


















