 Table of Contents
Table of Contents
- NIST 800-53 Certification: What Actually Exists (and What Doesn’t)
- Certification vs Accreditation: Getting the Terminology Right
- How Organizations Demonstrate NIST 800-53 Compliance
- Comparing Authorization Pathways Based on NIST 800-53
- How Isora GRC Supports NIST 800-53 Authorization
- Key Takeaways
-
NIST 800-53 Certification FAQs
- Is there a NIST 800-53 certification?
- What is an Authority to Operate (ATO) in NIST 800-53?
- How do you demonstrate NIST 800-53 compliance?
- What is the difference between certification and accreditation in NIST 800-53?
- Can you get NIST 800-53 certified like ISO 27001?
- What is the difference between FedRAMP and NIST 800-53?
NIST 800-53 Certification: What Actually Exists (and What Doesn’t)
NIST 800-53 is not a certifiable standard. NIST Special Publication 800-53 Revision 5 is a catalog of 1,196 security and privacy controls across 20 families, but the National Institute of Standards and Technology (NIST) does not operate a certification program for it. You cannot get “NIST 800-53 certified” the way you get ISO 27001 certified.
That said, the search for “NIST 800-53 certification” is not misguided. Several formal authorization pathways, including Risk Management Framework (RMF) authorization to operate, Federal Risk and Authorization Management Program (FedRAMP) Authority to Operate (ATO), and Federal Information Security Modernization Act (FISMA) compliance, are built directly on NIST 800-53 controls. Even without a formal certification, there are clear pathways to demonstrate NIST 800-53 compliance.
This page is part of our NIST 800-53 compliance guide, which covers the full compliance lifecycle from baseline selection through continuous monitoring. Below, you will learn why no certification exists, what terminology to use instead, and which pathways your organization should pursue.
Certification vs Accreditation: Getting the Terminology Right
The terms “certification,” “accreditation,” and “authorization” are often used interchangeably in cybersecurity, but they mean different things, and the distinction matters when discussing NIST 800-53.
Is there a NIST 800-53 certification? There is no direct NIST 800-53 certification. NIST 800-53 Rev 5 is a control catalog with 1,196 security and privacy controls across 20 families. Organizations demonstrate compliance through formal authorization pathways that include the RMF authorization to operate, FedRAMP ATO, or FISMA compliance, not through a certification issued by NIST.
Certification
In the security context, certification means a formal attestation by an accredited third party that an organization meets a defined standard. ISO 27001 is the clearest example. An accredited certification body audits your information security management system (ISMS) and issues a certificate if you meet the requirements. That certificate is valid for three years, with annual surveillance audits in between. NIST does not offer anything equivalent for NIST 800-53. NIST publishes standards and guidelines, it does not audit organizations, and it does not issue certificates.
For a detailed comparison of how ISO 27001 and NIST 800-53 relate, see our ISO 27001 vs NIST 800-53 guide.
Accreditation
Historically, the federal government used a process called Certification and Accreditation (C&A) to evaluate and approve information systems. Under C&A, “certification” referred to the technical evaluation of security controls, while “accreditation” referred to the management decision to authorize system operation.
In 2010, NIST replaced C&A terminology entirely with the Risk Management Framework (RMF) in SP 800-37 Rev 1. “Accreditation” became “authorization,” and the term “certification” was dropped from official NIST usage.
Legacy terminology persists in practice though, which is why searches for “NIST 800-53 certification” and “NIST 800-53 accreditation” remain common today.
Authorization
Authorization is the correct NIST term today. Under the NIST SP 800-37 RMF, an Authorizing Official (AO) reviews the security assessment of NIST 800-53 controls and grants an authorization to operate. This is a formal, documented decision that permits a system to operate based on an accepted level of risk. It is the closest equivalent to “certification” in the NIST ecosystem, where a named official puts their signature on a decision based on assessed evidence. Authorization to operate under NIST SP 800-37 RMF is the formal path for federal agencies and contractors handling federal information systems.
For cloud service providers, the equivalent term is Authority to Operate (ATO), which is granted by a federal agency as part of the FedRAMP authorization process.
For a comprehensive overview of how NIST 800-53 fits into the broader framework landscape, see our NIST 800-53 complete guide.
How Organizations Demonstrate NIST 800-53 Compliance
While there is no NIST 800-53 certification, organizations demonstrate compliance through five recognized pathways, each involving formal assessment of 800-53 controls by qualified assessors.
1. RMF Authorization to Operate
The most direct pathway. Under the RMF, defined in NIST SP 800-37 Rev 2, an Authorizing Official (AO) reviews the security assessment of NIST 800-53 controls and formally authorizes the system to operate. Authorization is required for all federal information systems and must be reauthorized periodically, typically every three years or upon significant change to the system or its operating environment. The authorization package includes the System Security Plan (SSP), Security Assessment Report (SAR), and Plan of Action and Milestones (POA&M).
2. FedRAMP Authority to Operate (ATO)
Cloud service providers (CSPs) that sell to federal agencies must undergo assessment against FedRAMP baselines, which are derived from NIST 800-53 but include additional controls and enhancements specific to cloud computing. FedRAMP Low requires ~156 controls, Moderate requires ~323, and High requires ~410.
An accredited Third-Party Assessment Organization (3PAO) independently assesses the CSP’s security controls. A federal agency’s Authorizing Official then reviews the assessment and signs the authorization, indicating that the agency assessed the CSP’s security posture in accordance with FedRAMP guidelines and found it acceptable. Single agency authorizations enable the agency to safely use a cloud product or service in a manner consistent with its use and risk tolerances. FedRAMP lists authorized CSPs on the FedRAMP Marketplace, and all federal agencies recognize the authorization.
Over 300 cloud products hold FedRAMP authorization, making it one of the most rigorous NIST 800-53-based assessment programs in operation.
Note: As of 2024, FedRAMP moved to a single FedRAMP Authorized designation, replacing the previous JAB and Agency authorization paths.
3. FISMA Compliance
Federal agencies demonstrate compliance with FISMA through annual assessments against NIST 800-53 controls. Agencies report compliance metrics to the Office of Management and Budget (OMB). The agency’s Inspector General (IG) conducts independent audits to verify implementation. FISMA compliance requires continuous monitoring and annual reporting and should not be viewed as a one-time event.
4. 3PAO Assessments
Third-Party Assessment Organizations (3PAOs) accredited by the American Association for Laboratory Accreditation (A2LA) perform independent security assessments against NIST 800-53. While 3PAO assessments are most commonly associated with FedRAMP, any organization can engage a 3PAO for independent validation of their 800-53 control implementation. This pathway is growing among private-sector organizations seeking rigorous, third-party proof of compliance.
5. ISO 27001 Certification (Related)
ISO 27001 is the only pathway in this list that results in formal third-party certification. While it is not built on NIST 800-53 directly, NIST provides an official mapping document that crosswalks 800-53 controls to ISO 27001 requirements, and the two share significant overlap in intent and coverage. Organizations that need a certifiable, internationally recognized standard often pursue ISO 27001 alongside their NIST 800-53 compliance program. For a detailed comparison, see our ISO 27001 vs NIST 800-53 guide.
For a detailed look at the assessment process, including assessment methods, self-assessment, and maturity models, see our guide to NIST 800-53 assessment. For risk assessment procedures that feed into control selection and prioritization, see the NIST 800-53 risk assessment guide.
Comparing Authorization Pathways Based on NIST 800-53
Each pathway for demonstrating NIST 800-53 compliance serves a different audience, requires a different assessment approach. The table below compares the five pathways across key dimensions.
| Pathway | Based On | Certifiable? | Who Needs It | Assessment Type |
| RMF Authorization to Operate | NIST 800-53 controls via RMF (SP 800-37) | No. Authorization, not certification. Granted by Authorizing Official. | Federal agencies, DoD, contractors operating federal systems | Internal or independent assessor; AO decision |
| FedRAMP Authority to Operate (ATO) | NIST 800-53 controls, with FedRAMP-specific enhancements: Low (~156), Moderate (~323), and High (~410). | No. ATO granted by federal agency. Not a certification. | Cloud service providers selling to federal agencies | 3PAO assessment (accredited by A2LA) |
| FISMA Compliance | NIST 800-53 controls + FIPS standards | No. Compliance determination. Annual reporting to OMB. | All federal agencies | Agency self-assessment + Inspector General audit |
| 3PAO Assessment | NIST 800-53 | No. Independent validation. Not a certification. | Any organization seeking third-party proof of compliance | Accredited 3PAO assessment |
| ISO 27001 | ISO/IEC 27001 Annex A controls (maps partially to 800-53) | YES. Formal certification by accredited certification body | Any organization (international standard) | Accredited certification body audit |
Several observations stand out from this comparison.
- Only ISO 27001 offers formal certification among these pathways. If you are searching for a “NIST 800-53 certification,” what you may actually need is ISO 27001. It is the internationally recognized certifiable standard that maps closely to 800-53 controls and produces a certificate you can show to customers, partners, and regulators. For a detailed comparison, see ISO 27001 vs NIST 800-53.
- FedRAMP ATO is the closest analog to certification within the NIST ecosystem. It is a formal, documented authorization issued by a federal agency’s Authorizing Official. It carries legal weight within the federal government and must be renewed periodically.
- FedRAMP is the most rigorous NIST 800-53-based assessment pathway. Cloud service providers typically invest $1 million to $3 million or more and 12 to 18 months in the FedRAMP authorization process. The assessment covers FedRAMP Low (156 controls), Moderate (323 controls), or High (410 controls) baselines.
- These pathways are not mutually exclusive. An organization can hold a FedRAMP authorization and pursue ISO 27001 certification simultaneously. A federal contractor can obtain RMF authorization for its systems while also maintaining a ISO 27001 certification for its international customers.
- No certification does not mean no compliance. The pathways above provide structured, recognized approaches to demonstrating NIST 800-53 compliance, each with its own assessment rigor and formal output. The right pathway depends on your organization type, regulatory obligations, and whether you need a certifiable standard or a formal authorization.
How Isora GRC Supports NIST 800-53 Authorization
Pursuing RMF authorization to operate, a FedRAMP ATO, or FISMA compliance requires a clear, documented picture of your control implementation across your organization. Without a structured platform, managing that process across departments, systems, and assessment cycles becomes a significant operational burden.
Isora GRC provides a single workspace for managing NIST 800-53 compliance from assessment through authorization.
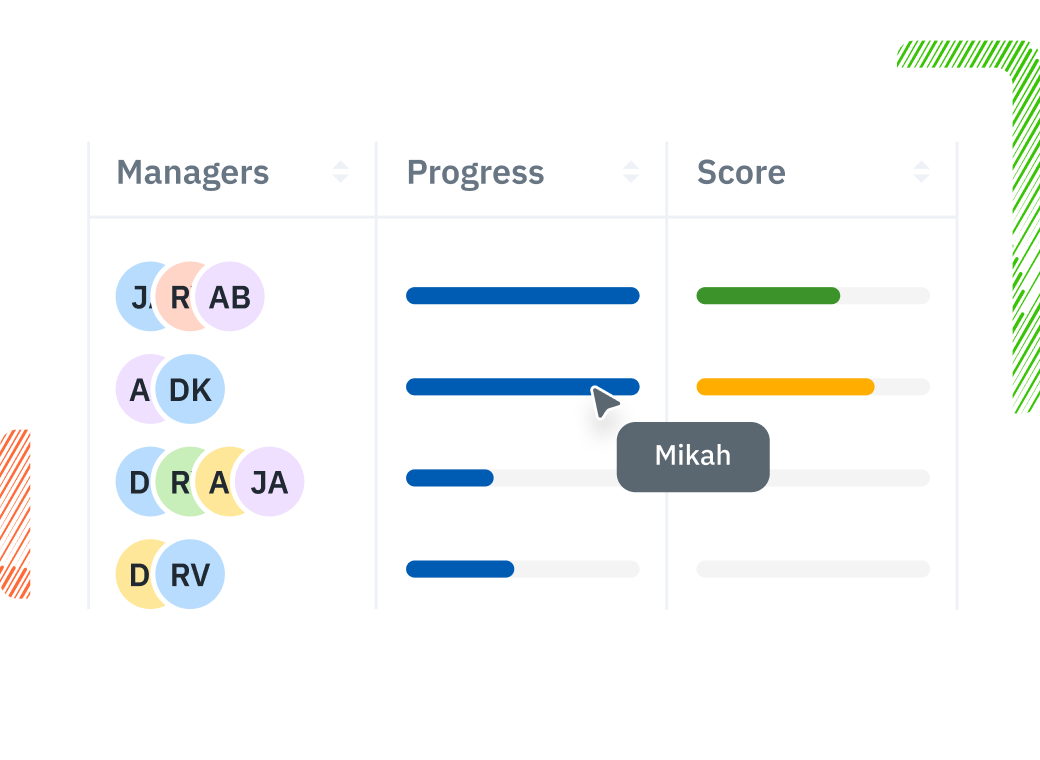
- Assessment Management: Organize assessments by system, department, or compliance goal and track progress in real time. Whether you are preparing an authorization package for RMF or building toward a FedRAMP ATO, Isora keeps your entire program visible from one dashboard.
- Prebuilt Questionnaires: Use prebuilt NIST 800-53 questionnaires to distribute control assessments to system owners across your organization and collect evidence directly within their responses, reducing the manual coordination that slows most authorization efforts.
- Reports and Scorecards: Generate automated compliance scorecards and audit-ready reports for Authorizing Officials, Inspector Generals, or FedRAMP reviewers, with drill-down capability from summary scores to individual control responses.
Isora scales with your security program, supporting additional frameworks, vendors, and organizational units without losing consistency. Learn more about our NIST 800-53 compliance software or request a demo to see how Isora supports authorization readiness across your organization.
Key Takeaways
There is no NIST 800-53 certification. RMF authorization to operate, FedRAMP ATO, and FISMA compliance are the recognized NIST 800-53-based formal authorization pathways to demonstrate compliance. ISO 27001 remains the only certifiable standard that partially maps to 800-53 controls.
The key distinction is this: certification means a third party issues a certificate confirming you meet a standard. Authorization means a senior official formally approves a system to operate based on assessed risk. Accreditation is legacy terminology that NIST replaced with authorization in 2010. Knowing which applies to your situation determines which pathway you pursue.
Whether you need RMF authorization to operate for a federal system, a FedRAMP ATO for a cloud product, or simply want to adopt a rigorous control framework voluntarily, NIST 800-53 provides the foundation.
Tools like Isora GRC can help you track authorization readiness and manage your NIST 800-53 control implementation across your organization. Learn more about NIST 800-53 compliance software.
Explore the full NIST 800-53 compliance guide for more on assessment, risk management, and implementation.
NIST 800-53 Certification FAQs
Is there a NIST 800-53 certification?
No. NIST does not operate a certification program for SP 800-53. The framework is a control catalog, not a certifiable standard. However, organizations can demonstrate compliance through formal pathways: RMF authorization to operate for federal information systems, FedRAMP ATO for cloud service providers, and FISMA compliance for federal agencies. Each involves formal assessment of 800-53 controls.
What is an Authority to Operate (ATO) in NIST 800-53?
An Authority to Operate (ATO) is a formal authorization issued by a federal agency’s Authorizing Official (AO) confirming that a cloud service provider’s security posture meets federal requirements. In the context of FedRAMP, a CSP receives an ATO from a sponsoring federal agency after an accredited 3PAO independently assesses its security controls against FedRAMP baselines (Low: 156 controls, Moderate: 323 controls, High: 410 controls).
In the RMF context, the equivalent process is called authorization to operate, wherein an Authorizing Official (AO) reviews security assessment results against NIST 800-53 controls and issues a formal decision permitting a federal information system to operate based on an accepted level of risk. It is the closest equivalent to “certification” in the NIST ecosystem.
How do you demonstrate NIST 800-53 compliance?
Organizations demonstrate compliance through five primary pathways: (1) obtaining RMF authorization to operate, (2) achieving a FedRAMP ATO as a cloud service provider, (3) meeting FISMA requirements as a federal agency, (4) undergoing independent 3PAO assessment, or (5) pursuing ISO 27001 certification with controls mapped to 800-53. The right pathway depends on your organization type and regulatory requirements.
What is the difference between certification and accreditation in NIST 800-53?
NIST replaced the term “accreditation” with “authorization” in SP 800-37 Rev 1 in 2010. The old Certification and Accreditation (C&A) process is now called the Risk Management Framework (RMF), defined in NIST SP 800-37. Today, certification is not an official NIST term for 800-53. The correct term depends on context: in FedRAMP, cloud service providers receive an Authority to Operate (ATO) from a federal agency. In the RMF, NIST refers to the equivalent process simply as “authorization to operate.”
Can you get NIST 800-53 certified like ISO 27001?
No. ISO 27001 offers formal third-party certification through accredited certification bodies. NIST 800-53 does not have an equivalent certification model. If your organization needs a certifiable security standard, ISO 27001 is the closest international option. NIST provides an official mapping document that crosswalks 800-53 Rev. 5 controls to ISO/IEC 27001:2022, making it straightforward to pursue both. Many organizations use NIST 800-53 for federal compliance and ISO 27001 for international certification. For a detailed comparison, see our ISO 27001 vs NIST 800-53 guide.
What is the difference between FedRAMP and NIST 800-53?
FedRAMP is an authorization program. NIST 800-53 is a control catalog. FedRAMP requires cloud service providers to implement FedRAMP baselines, which are derived from NIST 800-53 but include additional controls and enhancements specific to cloud computing environments. FedRAMP Low requires 156 controls, Moderate requires 323, and High requires 410. An accredited 3PAO must assess the CSP’s security controls against these baselines.
Think of it this way: NIST 800-53 defines the controls; FedRAMP defines the assessment and authorization process for cloud products selling to federal agencies.
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.


















