 Table of Contents
Table of Contents
- NIST CSF Core Functions and Implementation Tiers Explained
- What Are NIST CSF Functions and Tiers?
- NIST CSF Functions
- NIST CSF Implementation Tiers
- How to Measure CSF Performance
- Policy Templates for NIST CSF
- How to Simplify NIST CSF Compliance
- Key Takeaways
-
NIST CSF Functions and Tiers FAQs
- What are the 6 core functions of NIST CSF?
- How many tiers are in NIST CSF?
- What is the difference between functions and tiers?
- What is the Govern function?
- What does Tier 1 (Partial) mean?
- Do organizations need to reach Tier 4?
- How does NIST CSF handle incident response?
- How to use NIST CSF functions and tiers for an assessment
NIST CSF Core Functions and Implementation Tiers Explained
The NIST Cybersecurity Framework organizes cybersecurity risk management into six core functions and four implementation tiers that measure organizational maturity.
- Functions define key activities organizations must perform to manage cybersecurity risk.
- Tiers describe how consistently and effectively those activities are implemented across the organization.
Today, NIST CSF is the most widely adopted cybersecurity framework in the United States. Over half of organizationsreport using it, and Executive Order 13800 mandates its use across all federal agencies.
This guide covers each NIST CSF function in detail, breaks down all four tiers, explains how to measure CSF performance, and provides policy templates for organizations at any stage of framework adoption.
What Are NIST CSF Functions and Tiers?
The NIST CSF organizes cybersecurity risk management around two complementary structures: functions that define what activities to perform, and tiers that measure how consistently and effectively those activities are carried out.
NIST CSF Functions tell organizations what cybersecurity activities to focus on and where to direct their efforts. They include Govern, Identify, Protect, Detect, Respond, and Recover.
NIST CSF Tiers show how well those activities are being carried out across the organization, ranging from Partial (Tier 1) to Adaptive (Tier 4).
Each NIST CSF function contains multiple categories and subcategories that define specific cybersecurity outcomes. In CSF 2.0, the framework includes 22 categories and 106 subcategories distributed across the six functions.
NIST CSF Functions
The six functions of the NIST CSF represent a full lifecycle of cybersecurity risk management across governance and risk understanding through prevention, detection, response, and recovery as they operate concurrently.
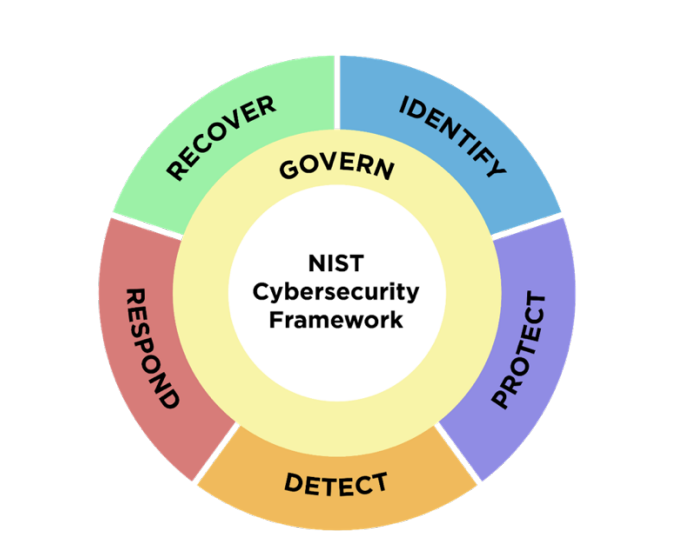
NIST CSF Functions, The NIST Cybersecurity Framework (CSF) 2.0
NIST diagrams put Govern at the center because it provides the strategic foundation that all five operational functions depend on: clear ownership, defined policies, and risk direction. The following table includes all six CSF functions and the number of categories and subcategories for each.
| Function | Code | Categories | Subcategories | Key Purpose |
| Govern (NEW) | GV | 6 | 31 | Strategy, policy, oversight, supply chain risk |
| Identify | ID | 3 | 21 | Asset management, risk assessment, improvement |
| Protect | PR | 5 | 22 | Access control, training, data security, platform security |
| Detect | DE | 2 | 11 | Continuous monitoring, adverse event analysis |
| Respond | RS | 4 | 13 | Incident management, analysis, reporting, mitigation |
| Recover | RC | 2 | 8 | Recovery execution, recovery communication |
| Total | 22 | 106 |
Organizations can explore the full structure using the NIST CSF 2.0 Reference Tool, which allows navigation through every category and subcategory. CISA’s Cross-Sector Cybersecurity Performance Goals (CPG) 2.0, released December 2025, aligns directly with all six CSF 2.0 functions and provides measurable baseline actions for critical infrastructure organizations.
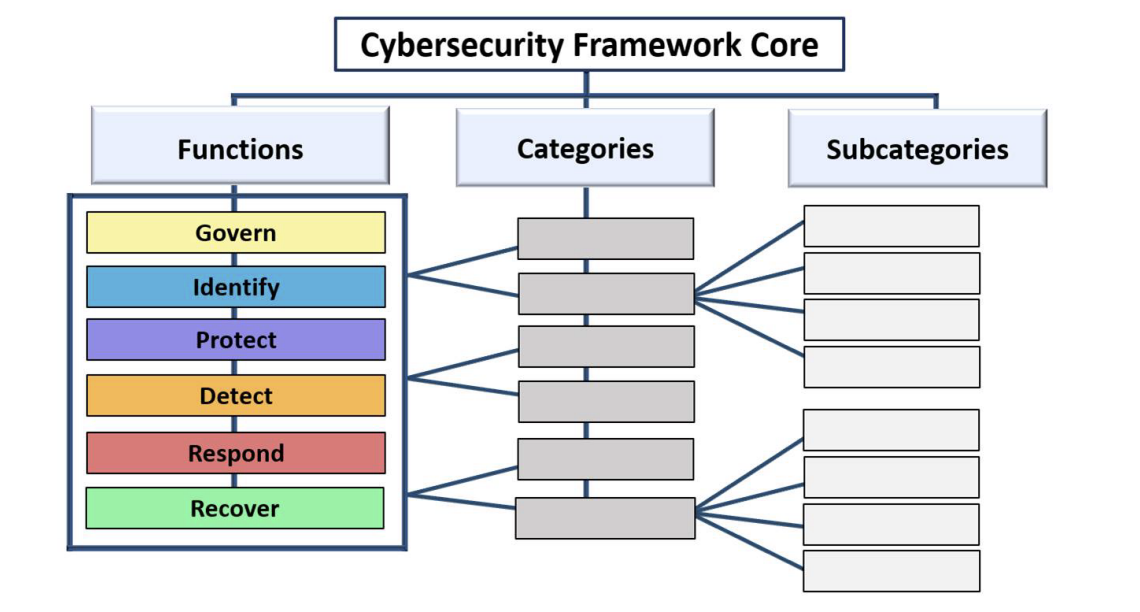
CSF Core Structure, NIST CSF 2.0
Govern (GV)
Govern establishes the organizational foundation for cybersecurity. It defines strategy, policy, leadership oversight, and accountability structures that guide how cybersecurity risk is managed across the organization.
Added in CSF 2.0, NIST elevated governance into a dedicated function to emphasize that cybersecurity is a leadership and risk management responsibility, not only a technical one. As ISACA’s analysis notes, it creates a formal hierarchy elevating cybersecurity to board-level governance. NIST’s IR 8286 series, updated in December 2025 to align with CSF 2.0, provides detailed guidance on integrating cybersecurity risk management into enterprise risk management — a direct extension of the Govern function’s emphasis on strategic alignment.
Govern contains six categories and 31 subcategories covering how organizations establish policies, assign roles, manage supply chain risk, and maintain oversight of their cybersecurity program.
| Code | Category | Subcategories | Purpose |
| GV.OC | Organizational Context | 4 | Business objectives, mission context, risk tolerance |
| GV.RM | Risk Management Strategy | 5 | Cybersecurity risk management approach and priorities |
| GV.RR | Roles, Responsibilities, and Authorities | 4 | Assignment of cybersecurity ownership and accountability |
| GV.PO | Policy | 5 | Organizational cybersecurity policies and standards |
| GV.OV | Oversight | 5 | Leadership oversight and governance mechanisms |
| GV.SC | Supply Chain Risk Management | 8 | Management of third-party and vendor cybersecurity risks |
| Total | 31 |
Identify (ID)
Identify helps organizations develop a clear understanding of their assets, risks and vulnerabilities. It provides the foundation for all protective and defensive activities. An organization cannot effectively manage cybersecurity risk without first knowing what it is responsible for protecting.
Identify contains three categories and 21 subcategories covering how organizations inventory assets, assess cybersecurity risks, and continuously improve their understanding of the risk environment.
| Code | Category | Subcategories | Purpose |
| ID.AM | Asset Management | 8 | Inventory and classification of systems, devices, software, and data |
| ID.RA | Risk Assessment | 10 | Identification and analysis of cybersecurity threats and vulnerabilities |
| ID.IM | Improvement | 3 | Continuous improvement of cybersecurity risk management |
| Total | 21 |
Supply Chain Risk Management, which sat under Identify in CSF 1.1, moved to Govern in CSF 2.0. Improvement is also new to 2.0, formalizing the process of incorporating lessons from assessments, incidents, and audits back into the program.
To see everything that changed in CSF 2.0, including the new Govern function and structural updates, read our NIST CSF 2.0 guide.
Protect (PR)
Protect covers the safeguards organizations put in place to reduce the likelihood and impact of cybersecurity events. This is where most organizations direct the bulk of their security investment. A strong foundation here reduces the frequency and severity of events that escalate to the Detect and Respond functions.
Protect contains five categories and 22 subcategories covering the safeguards organizations implement to protect systems, identities, data, and infrastructure from cybersecurity threats.
| Code | Category | Subcategories | Purpose |
| PR.AA | Identity Management, Authentication, and Access Control | 6 | Identity governance, authentication, and access enforcement |
| PR.AT | Awareness and Training | 3 | Security awareness and role-based training |
| PR.DS | Data Security | 6 | Protection of data confidentiality, integrity, and availability |
| PR.PS | Platform Security | 4 | Secure configuration and management of systems and devices |
| PR.IR | Technology Infrastructure Resilience | 3 | Infrastructure resilience and availability protections |
| Total | 22 |
Detect (DE)
Detect enables timely identification of cybersecurity events to reduce the amount of time attackers have unrestricted access to an organization’s systems, data, and operations.
The average time to identify a breach is 181 days, according to IBM’s Cost of a Data Breach Report. As outlined in NIST incident response guidance (SP 800-61r3), effective detection capabilities compress that window.
The Detect function consists of two categories with 11 subcategories.
| Code | Category | Subcategories | Purpose |
| DE.CM | Continuous Monitoring | 8 | Monitoring networks, systems, and environments for anomalies |
| DE.AE | Adverse Event Analysis | 3 | Investigation and analysis of detected events |
| Total | 11 |
Continuous monitoring requires establishing a clear baseline of normal activity across the environment so that anomalies can be identified and escalated appropriately.
Respond (RS)
Respond covers the activities after detecting a cybersecurity incident, such as containing the incident, reducing damage, and ensuring appropriate communication with stakeholders.
Effective response is an organizational process. Often, simply having a plan in place before an incident occurs is what separates a contained event from a crisis.
The Respond function includes four categories with 13 subcategories.
| Code | Category | Subcategories | Purpose |
| RS.MA | Incident Management | 3 | Response planning and incident management coordination |
| RS.AN | Incident Analysis | 4 | Investigation and analysis of incidents |
| RS.CO | Incident Reporting and Communication | 3 | Internal and external incident communication |
| RS.MI | Incident Mitigation | 3 | Containment and remediation of incidents |
| Total | 13 |
Recover (RC)
Recover focuses on restoring systems and operations after an incident to ensure the organization can resume normal operations safely and efficiently. It involves restoring systems from backups, rebuilding infrastructure, validating system integrity, and communicating with internal and external stakeholders.
Organizations that plan recovery effectively can significantly reduce the operational and financial impact of cyber incidents.
The Recover function includes two categories with 8 subcategories.
| Code | Category | Subcategories | Purpose |
| RC.RP | Incident Recovery Plan Execution | 5 | Restoration of systems and services after incidents |
| RC.CO | Incident Recovery and Communication | 3 | Communication during and after recovery activities |
| Total | 8 |
NIST CSF Implementation Tiers
Implementation Tiers describe how mature and consistent an organization’s approach to cybersecurity risk management is, specifically, how well it performs the activities within each of the six CSF functions. Each of the four tiers represents a progressively more integrated and proactive approach.
Importantly, tiers are assessed per function, not as a single overall score, which means an organization can operate at different tier levels across different areas of its program.
| Tier | Name | Risk Management Process | Integrated Program | External Participation |
| Tier 1 | Partial | Ad hoc, reactive | Limited awareness | Minimal participation |
| Tier 2 | Risk Informed | Risk-aware but not organization-wide | Awareness but limited practice | Some information sharing |
| Tier 3 | Repeatable | Formal policy, regularly updated | Organization-wide approach | Regular collaboration and information sharing |
| Tier 4 | Adaptable | Continuous improvement, predictive | Integrated into organizational culture | Strategic partnerships and active collaboration |
The CSF tier model builds on the organizational risk management hierarchy established in NIST SP 800-39, which defines three levels of risk management — organization, mission/business process, and information system — and emphasizes integrating security decisions across all three.
According to the NIST Quick-Start Guide for CSF Tiers, tiers are not always aspirational. The right tier depends on the organization’s risk environment, regulatory requirements, and available resources.
Tier 1: Partial
At Tier 1, an organization’s cybersecurity practices are ad hoc and reactive. Without formal policies in place, execution is inconsistent, and risk management decisions are made informally, often only in response to incidents.
Organizations at Tier 1 tend to rely heavily on individual expertise rather than defined procedures. This is especially common among organizations new to structured frameworks.
Tier 2: Risk Informed
At Tier 2, management has approved cybersecurity practices, but they are not consistently applied across the organization. Risk assessments happen, but results do not always feed into decision-making. Many mid-sized organizations land here, where the gap between policy and practice is a real vulnerability.
Tier 3: Repeatable
At Tier 3, cybersecurity risk management is formal, documented, and regularly reviewed. Policies apply consistently across the organization and cybersecurity considerations are integrated into business decisions.
Most organizations should aim to reach Tier 3 across the majority of their functions. It represents a mature, sustainable level of cybersecurity practice for most risk environments.
Tier 4: Adaptive
At Tier 4, cybersecurity is fully embedded in organizational culture. Risk management includes predictive analytics, automated response capabilities, and continuous improvement cycles informed by both internal experience and external threat intelligence.
In practice, achieving a true Tier 4 program across all functions and subcategories is rare. It is most realistic for large enterprises and critical infrastructure operators with mature, well-resourced security programs.
How to Measure CSF Performance
CSF performance is measured by evaluating how consistently and effectively each function is implemented across the organization, mapped against a defined target tier. This process tracks progress over time, surfaces gaps before they become incidents, and gives leadership an evidence-based view of program maturity.
The following are sample indicators for each function that can be tracked to measure progress and demonstrate success. Performance targets for each metric will vary depending on the organization’s current implementation tier. What success looks like at Tier 2 will differ from what is expected at Tier 3 or Tier 4. A complete set of indicators will depend on the organization’s context, risk environment, and target tier level.
| Function | What It Measures | Example |
| Govern (GV) | Policy governance maturity and progress toward formalized cybersecurity governance | Percentage of policies reviewed within 12 months; percentage of policies drafted for new organizations (Tier 1–2) |
| Identify (ID) | Visibility into organizational assets and risk surface | Percentage of assets inventoried and classified |
| Protect (PR) | Effectiveness of preventive safeguards | MFA adoption rate; security awareness training completion |
| Detect (DE) | Speed of identifying cybersecurity events | Mean time to detect (MTTD) incidents |
| Respond (RS) | Efficiency of incident response processes | Mean time to respond (MTTR) |
| Recover (RC) | Ability to restore systems and operations | Recovery time objective (RTO) achievement |
NIST SP 800-55 provides the authoritative methodology for developing and selecting information security performance measures aligned to any risk management framework, including the CSF.
For a structured approach to evaluating program maturity against the full framework, see the NIST CSF assessment guide. For a downloadable self-assessment tool, access the NIST CSF 2.0 Readiness Scorecard.
Policy Templates for NIST CSF
Every function in the NIST CSF maps to a set of policies and procedures that organizations should have documented.
Policy templates give organizations a starting point for translating framework requirements into formal, actionable documentation. They are particularly useful for organizations at Tier 1 or Tier 2 that are building out their cybersecurity program for the first time, as well as for more mature organizations looking to audit and close gaps in their existing documentation.
NIST provides official Quick Start Guides with templates and implementation resources for each function, and publishes CSF 2.0 Implementation Examples for every subcategory with concrete actions organizations can take within each function. For a step-by-step walkthrough of putting the framework into practice, see How to Implement NIST CSF.
The following example illustrates the types of documentation commonly created.
| Function | Documentation |
| Govern | Risk management policy; cybersecurity governance charter; supply chain risk management policy |
| Identify | Asset management policy; risk assessment methodology; asset classification standards |
| Protect | Access control policy; data classification policy; security awareness training program; encryption standards |
| Detect | Continuous monitoring procedures; log management standards; security event monitoring procedures |
| Respond | Incident response plan; incident escalation procedures; incident communication policy |
| Recover | Disaster recovery plan; business continuity policy; recovery communication procedures |
How to Simplify NIST CSF Compliance
Isora GRC is built to operationalize the NIST CSF, mapping directly to its functions and tiers so security teams can assess maturity, track gaps, and manage compliance from a single platform.
- Structured assessments: Distribute prebuilt CSF-aligned questionnaires to control owners across teams and track completion in real time.
- Asset and vendor inventories: Link systems, vendors, and applications directly to assessments and risk records, supporting the Identify and Govern functions with end-to-end visibility.
- Audit-ready reporting: Generate compliance scorecards aligned to CSF structure and terminology, ready for leadership and regulators.
Learn more about simplifying NIST CSF compliance with Isora GRC.
Key Takeaways
The six core NIST CSF functions — Govern, Identify, Protect, Detect, Respond, and Recover — cover the full lifecycle, from establishing governance and understanding risk through to recovering from incidents.
The four implementation tiers — Partial, Risk Informed, Repeatable, and Adaptive — give organizations a way to measure how consistently and effectively those functions are being executed. Tiers are are evaluated per function, which means an organization can be at different levels across different areas of their program.
Organizations should aim for Tier 3 across the majority of their functions as a sustainable, long-term target.
See how Isora GRC simplifies NIST CSF compliance →
NIST CSF Functions and Tiers FAQs
What are the 6 core functions of NIST CSF?
The six core functions of NIST CSF are Govern, Identify, Protect, Detect, Respond, and Recover. They cover the full lifecycle of cybersecurity risk management. Govern establishes strategy and oversight, Identify helps organizations understand their assets and risks, Protect implements safeguards, Detect identifies cybersecurity events, Respond manages incidents, and Recover restores operations after an incident.
Govern is the newest addition, introduced in CSF 2.0 in February 2024.
How many tiers are in NIST CSF?
There are four implementation tiers: Tier 1 (Partial), Tier 2 (Risk Informed), Tier 3 (Repeatable), and Tier 4 (Adaptive). These tiers describe how mature and integrated an organization’s cybersecurity risk management practices are. A higher tier generally means processes are more formalized, consistently applied, and continuously improved.
What is the difference between functions and tiers?
Functions define what cybersecurity activities an organization needs to perform. Tiers describe how consistently and effectively those activities are being carried out. Think of functions as the “what” and tiers as the “how well.” Both are needed for a clear picture of where a program stands.
What is the Govern function?
Govern is the function that establishes the organizational foundation for everything else, including strategy, policy, ownership, and oversight. It was added in CSF 2.0 to make clear that cybersecurity is a leadership responsibility, not just a technical one. Without Govern in place, the other five functions lack the strategic direction they need to be effective.
What does Tier 1 (Partial) mean?
Organizations with mostly informal or reactive cybersecurity practices are typically operating at Tier 1 (Partial). At this level, some security activities may exist, but they are not guided by formal policies, consistent procedures, or organization-wide coordination. Many organizations start at Tier 1 when they first begin implementing a cybersecurity framework.
Do organizations need to reach Tier 4?
Not at all. NIST is explicit that higher tiers are not always the right target. Most organizations should aim for Tier 3, which represents a formal, consistently applied program. Tier 4 is rare in practice and most realistic for large enterprises or critical infrastructure operators with significant resources.
How does NIST CSF handle incident response?
Incident response sits across two functions: Detect and Respond. Detect covers identifying that something has gone wrong through continuous monitoring and event analysis. Respond takes over from there, covering containment, analysis, communication, and mitigation once an incident has been confirmed.
How to use NIST CSF functions and tiers for an assessment
Start by mapping current practices against the six functions to build a current profile. Then define a target profile based on the organization’s risk environment and requirements. The gap between the two, assessed per function, becomes the implementation roadmap. NIST’s Quick-Start Guide for Organizational Profiles (SP 1301) provides a structured five-step process for building current and target profiles. For a full step-by-step walkthrough, see the NIST CSF assessment guide.
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.
Dive into our research-backed resources–from product one pagers and whitepapers, to webinars and more–and unlock the transformative potential of powerfully simple GRC.
Learn More


















 Other Relevant Content
Other Relevant Content