 Table of Contents
Table of Contents
-
NIST 800-53 Assessment: Types, Procedures & Tools
- Types of 800-53 Assessments
- NIST 800-53 Self-Assessment Questionnaires (SAQs)
- NIST 800-53 Maturity Model & Levels
- NIST SP 800-53A Assessment Procedures
- NIST 800-53 Assessment Tools & Approaches
- How to Simplify NIST 800-53 Assessments
- Key Takeaways
-
NIST 800-53 Assessment FAQs
- What is a NIST 800-53 assessment?
- How many controls are in NIST 800-53?
- What is NIST SP 800-53A?
- Is a NIST 800-53 assessment required?
- How often should you conduct a NIST 800-53 assessment?
- What is the difference between a NIST 800-53 assessment and an audit?
- What is a NIST 800-53 maturity assessment?
- Can you self-assess against NIST 800-53?
NIST 800-53 Assessment: Types, Procedures & Tools
A NIST 800-53 assessment validates whether an organization’s security and privacy controls are implemented correctly and operate as intended under NIST Special Publication 800-53.
Because NIST 800-53 Rev 5 contains 1,196 controls across 20 control families, evaluating each relevant control requires a structured approach. Whether your organization is a federal agency subject to the Federal Information Security Modernization Act (FISMA), a cloud provider pursuing FedRAMP authorization, or a university managing federal research data, assessment is the process that translates compliance into measurable outcomes.
For organizations still developing their program, our NIST 800-53 compliance guide provides a broader starting point.
This guide covers three types of 800-53 assessments: self-assessment, third-party, and automated assessments. It also explains the role of the companion document SP 800-53A, how organizations structure self-assessment questionnaires, and practical GRC tools for managing assessments at scale.
Types of 800-53 Assessments
NIST 800-53 assessments fall into three primary categories: self-assessments conducted by internal teams, third-party assessments performed by independent assessors, and automated assessments driven by continuous monitoring tools. Each approach serves a different purpose depending on regulatory requirements, risk tolerance, and budget.
A NIST 800-53 assessment is a systematic evaluation of an organization’s security and privacy controls against the 1,196 controls defined in NIST SP 800-53 Rev 5. Assessments determine whether controls are implemented correctly, operating as intended, and producing the desired outcome.
A self-assessment is an internal review of how an organization has implemented its NIST 800-53 controls. Here, internal security teams or system owners conduct the evaluation using questionnaires, documentation reviews, and evidence collection. The low cost allows organizations to run them quarterly or semi-annually to track progress between formal evaluations.
Self-assessments are common in higher education institutions, healthcare organizations, research labs, and private-sector companies that use NIST frameworks as a security best practice but do not require a formal Authority to Operate (ATO). The trade-off is potential bias — internal teams may unintentionally overlook weaknesses or interpret requirements in ways that favor existing practices.
Third-Party Assessment
Third-party assessments provide an objective, independent evaluation of control effectiveness. Federal agencies operating under FISMA and cloud service providers pursuing FedRAMP authorization, rely on independent assessors, including Third Party Assessment Organizations (3PAOs), to perform formal evaluations.
Third-party assessments typically occur annually or during an ATO authorization cycle. Although they involve higher costs, they provide the independence and credibility required for regulatory compliance. Under the FedRAMP 20xmodernization initiative, the 3PAO role is evolving from manual documentation review toward automated evidence validation, though third-party assessment remains required for both the traditional and 20x authorization paths.
Automated and Continuous Assessment
Automated assessments use monitoring tools to continuously evaluate control effectiveness through vulnerability scanning, configuration checks, and log analysis. NIST encourages ongoing assessment through the Monitor steps in the Risk Management Framework (RMF).
Organizations with mature programs increasingly rely on automated monitoring to supplement manual assessments. Automated approaches primarily evaluate technical controls and therefore work best as part of a hybrid strategy.
NIST 800-53 Assessment Types Comparison
| Type | Who | When | Cost | Use |
| Self-Assessment | Internal security or compliance teams | As needed; often quarterly or semi-annually | Variable (Internal resource effort) | Baseline readiness checks, gap analysis, internal monitoring |
| Third-Party Assessment | Independent assessor (3PAO) | Annually or per ATO cycle | High | Regulatory compliance such as FedRAMP or FISMA |
| Automated/Continuous | Security teams using monitoring tools | Continuous | Medium | Mature programs, ongoing monitoring of technical controls |
Most organizations combine these approaches. Self-assessments maintain readiness between formal reviews, third-party assessments satisfy regulatory mandates, and automated monitoring catches control drift in real time.
A self-assessment questionnaire (SAQ) translates NIST 800-53 control requirements into structured questions that unit owners and system administrators can answer to document their control implementation status. SAQs are the operational backbone of any self-assessment program, particularly for large, decentralized organizations like universities and multi-site agencies.
Building an effective SAQ starts with mapping each control family to specific, answerable questions. For example, the Access Control (AC) family might include questions such as:
- Do you enforce multi-factor authentication for privileged accounts?
- Are access permissions reviewed at least quarterly?
The goal is to convert technical control language into questions that operational staff, who are not security specialists, can easily understand and answer accurately.
For more on questionnaire design, check out our complete guide on SAQs.
Scoping the Assessment to the Correct Baseline
Scoping is critical. NIST 800-53 Rev 5 defines three baselines that determine which controls apply to a system:
- Low: 149 controls
- Moderate: 287 controls
- High: 370 controls
Rather than attempting to assess the entire control catalog, organizations should align their SAQ with the baseline associated with the system’s FIPS 199 impact level, as defined in NIST SP 800-53B.
Scoping should also reflect the actual assessment environment. Controls that do not apply to the target system should be excluded from the assessment scope. For example, physical security controls may not apply in a fully cloud-based environment. A well-scoped assessment focuses only on controls that are implemented, inherited, or required for the system being evaluated. Ultimately, this approach improves response accuracy and reduces unnecessary assessment effort.
Distributing SAQs Across the Organization
In organizations with many departments or units, the distribution model matters as much as the questions themselves. Typically, a central GRC team designs and distributes the SAQ, while decentralized unit owners complete it for their systems or business functions.
But managing responses across dozens or hundreds of units quickly becomes difficult with email and spreadsheets. Teams must track response rates, follow up on overdue submissions, and collect evidence. Platforms that support self-assessment questionnaires simplify this workflow considerably.
Even with the right distribution model, however, several issues can reduce the quality of SAQ responses. These include questionnaire fatigue from asking too many questions too often, inconsistent interpretation of questions across units, and lack of strong evidence. Clear instructions, examples for ambiguous controls, and required evidence uploads for critical controls help improve assessment accuracy.
NIST 800-53 Maturity Model & Levels
NIST 800-53 controls are assessed at the individual control level, where each control is implemented, not implemented, or partially implemented based on the percentage of control parts fulfilled. This granular approach is effective for compliance verification but does not directly measure how well an organization’s overall security program operates.
For program-level maturity, the NIST Cybersecurity Framework (CSF) 2.0 Implementation Tiers provide the appropriate evaluation framework. CSF 2.0 evaluates strategic processes and outcomes rather than individual control status, making it better suited for measuring organizational maturity across security functions.
Some organizations apply a conceptual maturity overlay to track how their assessment processes evolve over time:
| Level | Name | Description | Characteristics |
| 1 | Ad Hoc | Controls exist inconsistently | Reactive, undocumented, person-dependent |
| 2 | Defined | Controls documented with procedures | Repeatable, policy-driven, evidence available |
| 3 | Managed | Controls measured and tracked | Metrics-driven, regular reporting, gap tracking |
| 4 | Optimized | Controls continuously improved | Proactive, threat-informed, automated monitoring |
These levels describe how an organization’s assessment program operates, not the status of individual controls. A control assessed as “implemented” under 800-53 tells you the control is in place. CSF 2.0 Implementation Tiers (Partial, Risk-Informed, Repeatable, Adaptive) tell you how consistently and strategically the organization manages controls as a program.
The distinction matters in practice: NIST 800-53 controls are too granular for a maturity ranking to add value at the individual control level. Complex controls with multiple parts may be “partially implemented,” but that reflects the percentage of the control fulfilled rather than a maturity stage. Program-level maturity is better assessed through CSF 2.0, which examines strategic processes and outcomes of control operations.
Organizations seeking both compliance verification and maturity measurement should use 800-53 assessments for control-level status and CSF 2.0 for program-level evaluation. The NIST Cybersecurity and Privacy Reference Tool (CPRT) provides official mappings between SP 800-53 controls and CSF 2.0 subcategories to support this dual approach.
NIST SP 800-53A Assessment Procedures
NIST Special Publication 800-53A defines the official procedures for assessing security and privacy controls in NIST 800-53. It is the companion document that tells assessors exactly what to examine, interview, and test. The current version, SP 800-53A Rev. 5, aligns directly with SP 800-53 Rev. 5 and is intended to be used alongside it. In August 2025, NIST issued Release 5.2.0 of both publications, adding assessment procedures for three new controls (SA-24, SA-15(13), SI-02(07)) while leaving all baseline allocations unchanged. While SP 800-53 specifies what organizations must implement, SP 800-53A explains how to verify that implementation works.
SP 800-53A Rev 5 specifies three assessment methods that assessors use individually or in combination:
- Examine: Review documentation, policies, procedures, system configurations, and other artifacts to verify controls are defined and documented.
- Interview: Speak with staff responsible for control implementation to confirm they understand the procedures and their role in maintaining them.
- Test: Actively exercise controls to confirm they work as intended. This may include running vulnerability scans, attempting unauthorized access, or verifying that automated alerts trigger correctly.
SP 800-53A also supports the Assess step (Step 5) of the RMF defined in NIST SP 800-37 Rev. 2. Here, organizations use 800-53A procedures to determine whether implemented controls meet their intended objectives. For a detailed walkthrough of how assessment fits within the RMF lifecycle, see RMF and NIST 800-53.
Organizations conducting NIST 800-53 security assessments should treat SP 800-53A as their primary procedural reference. It removes ambiguity from the assessment process and ensures that results are defensible, repeatable, and aligned with NIST’s expectations.
NIST 800-53 Assessment Tools & Approaches
Organizations use several tools to manage NIST 800-53 assessments. Most programs combine GRC platforms, spreadsheets, and automated scanning tools. The right choice depends on your organization’s scale, the number of systems in scope, assessment frequency, and regulatory requirements.
GRC Platforms for NIST 800-53
Centralized GRC tools map controls to assessments, distribute questionnaires to unit owners, track evidence collection, and generate compliance reports. These systems are especially valuable for organizations with multiple departments or decentralized operations such as universities. An assessment management tool can reduce the operational burden of large-scale assessment campaigns.
Spreadsheet-Based Approaches
NIST publishes the 800-53 control catalog in spreadsheet formats and through OSCAL(Open Security Controls Assessment Language). Spreadsheets are often used for early gap assessments or smaller environments, but they become difficult to maintain and scale as control counts grow and assessment cycles repeat.
Automated Scanning and SCAP
Security Content Automation Protocol (SCAP) tools automate assessment of certain technical controls including configuration management, vulnerability scanning, and patch verification. Automated scanning is efficient but covers only a subset of controls, primarily technical ones. Operational and management controls still require manual assessment methods.
Hybrid Approaches
Most mature organizations combine automated scanning for technical controls with questionnaire-based assessment for operational and management controls. This hybrid model balances efficiency with coverage. For a deeper look at risk-focused assessment, see our NIST 800-53 risk assessment guide, or IT risk assessment fundamentals.
When selecting tools, consider the number of systems in scope, whether you need FedRAMP or FISMA documentation, your assessment frequency, and your budget. Organizations managing hundreds of controls across multiple units will benefit most from dedicated GRC platforms.
How to Simplify NIST 800-53 Assessments
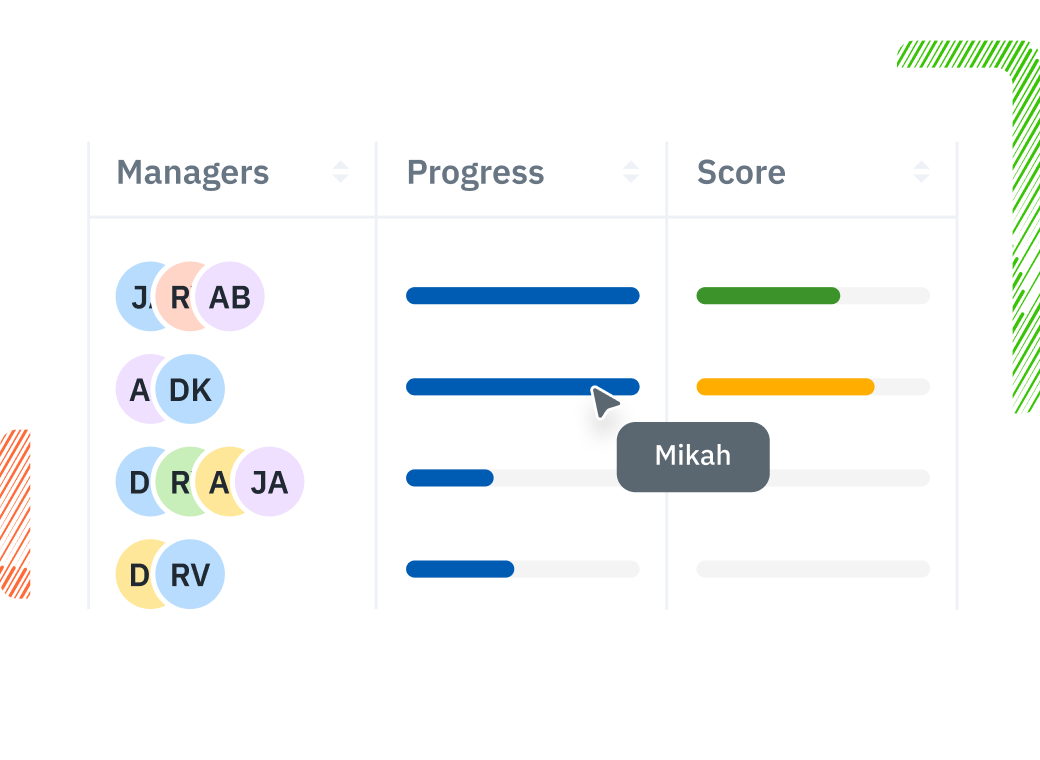
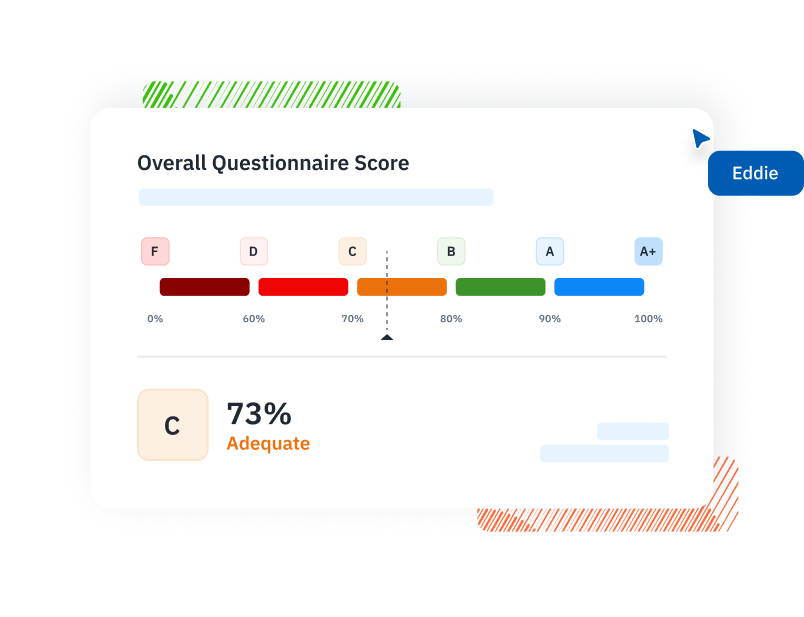
Organizations managing NIST 800-53 assessments across multiple departments, units, or campuses, need a single shared workspace where every assessment response, evidence attachment, and completion status is visible without chasing spreadsheets or email threads. Isora GRC by SaltyCloud streamlines assessments by distributing control-level questionnaires to unit owners and tracking completion in real time.
Key capabilities that support NIST 800-53 assessment workflows include:
- Assessment questionnaire distribution: Build NIST 800-53-aligned questionnaires and distribute them to decentralized unit owners. Each unit responds independently, and the platform aggregates results into a unified compliance view.
- Real-time completion tracking: See which units have completed assessments, which are overdue, and where gaps exist, across your entire organization, in one dashboard.
- Evidence collection: Attach documentation and evidence directly to control assessments, building a ready-made audit trail that supports both internal reviews and third-party evaluations.
In Isora, assessments, risks, assets, and vendors are all connected, creating a single source of truth where collaboration is natural and nothing slips through the cracks. Organize assessments by compliance goal to streamline complex campaigns across your institution.
See how NIST 800-53 compliance software automates assessment workflows for organizations managing controls across multiple departments, or request a demo to see Isora in action.
Key Takeaways
NIST 800-53 assessment is the verification engine that determines whether your security and privacy controls are actually working. By combining self-assessments for ongoing readiness, third-party evaluations for regulatory compliance, and automated monitoring for real-time visibility, organizations can build an assessment program that goes beyond checkbox compliance.
SP 800-53A provides the official procedures for evaluating control implementation, automated tools help monitor technical safeguards, and centralized platforms simplify coordination across large assessment programs. The key is matching your assessment approach to your organization’s size, regulatory requirements, and risk tolerance.
Explore more NIST 800-53 compliance topics in our NIST 800-53 compliance guide, or see how Isora GRC simplifies NIST 800-53 assessments for complex organizations.
NIST 800-53 Assessment FAQs
What is a NIST 800-53 assessment?
A NIST 800-53 assessment evaluates whether an organization has implemented its security and privacy controls correctly and whether those controls operate as intended. Assessors review documentation, interview responsible staff, and test system safeguards using procedures defined in SP 800-53A. Organizations may conduct assessments internally, use independent assessors, or rely on automated monitoring tools.
How many controls are in NIST 800-53?
NIST 800-53 Rev 5 contains 1,196 security and privacy controls organized into 20 control families. The number of controls an organization must assess depends on its baseline: Low (149 controls), Moderate (287), or High (370).
What is NIST SP 800-53A?
NIST SP 800-53A is the companion document that explains how to assess each NIST 800-53 control. It specifies three assessment methods:
- Examine: review policies, documentation, and system configurations
- Interview: speak with personnel responsible for implementing controls
- Test: verify that controls operate as intended
Assessors use these procedures to perform consistent and defensible security assessments.
Is a NIST 800-53 assessment required?
NIST 800-53 assessments are mandatory for U.S. federal agencies under FISMA and for cloud service providers seeking FedRAMP authorization. Outside the federal government, many organizations adopt the framework voluntarily as a security best practice. It is widely used in higher education, healthcare, research environments, and regulated industries.
How often should you conduct a NIST 800-53 assessment?
Most organizations conduct formal assessments once a year or during an Authority to Operate (ATO) cycle. NIST recommends continuous monitoring as part of the Risk Management Framework (RMF). Self-assessments can be conducted quarterly to maintain readiness between formal evaluations.
What is the difference between a NIST 800-53 assessment and an audit?
A NIST 800-53 assessment evaluates whether controls are implemented and operating effectively, typically using SP 800-53A procedures. An audit is a formal, independent examination that produces a compliance determination and may have regulatory or legal implications. Assessments feed into audits.
What is a NIST 800-53 maturity assessment?
NIST 800-53 controls are assessed as implemented, not implemented, or partially implemented at the individual control level. For program-level maturity, organizations should use the NIST Cybersecurity Framework (CSF) 2.0 Implementation Tiers, which evaluate how consistently and strategically an organization manages its security program rather than the status of individual controls.
Can you self-assess against NIST 800-53?
Yes. Organizations frequently conduct internal self-assessments using questionnaires aligned to 800-53 controls and baselines. These assessments help identify gaps, collect evidence, and prepare systems for formal evaluations, though they do not replace independent evaluation for FedRAMP or FISMA.
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.


















