 Table of Contents
Table of Contents
NIST CSF vs NIST 800-53: Why They’re Complementary, Not Competitors
NIST CSF and NIST 800-53 are two different publications designed to work together in a cybersecurity program. Both are published by the National Institute of Standards and Technology (NIST), but each resource serves a different purpose. Treating them as interchangeable is one of the most common misconceptions in information security risk management (ISRM) today.
The NIST Cybersecurity Framework (CSF) helps organizations structure how they manage cybersecurity risk. NIST SP 800-53 Rev 5 provides the security and privacy controls that put those plans into practice. Many organizations start with CSF to organize their security program, then adopt 800-53 controls as their program matures.
Part of our NIST 800-53 framework comparisons series, this guide explains how the two publications relate, how CSF 2.0 maps to 800-53 controls, and when to use each.
NIST 800-53 vs CSF
The primary difference between NIST CSF and NIST 800-53 is purpose — one is a framework for managing cybersecurity risk, the other is a control catalog.
NIST CSF 2.0 is a voluntary cybersecurity risk management framework that helps organizations understand, assess, and improve their cybersecurity posture through outcome-based guidance.
NIST SP 800-53 Revision 5 is a catalog of security and privacy controls that helps organizations protect information systems and manage security risks.
The NIST Cybersecurity Framework (CSF) 2.0, released in February 2024, is a high-level risk management framework. It organizes cybersecurity activities into six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. These functions break down into 22 categories and 106 subcategories that describe the outcomes organizations should achieve. Organizations assess their practices using four implementation tiers, from Tier 1 (Partial) to Tier 4 (Adaptive). CSF is voluntary, risk-based, and industry-agnostic. For a closer look at the Cybersecurity Framework, check out our NIST CSF complete guide.
NIST Special Publication 800-53 Revision 5, published in September 2020, is a control catalog. Today, it contains 1,196 security and privacy controls organized across 20 families, including access control, incident response, and system integrity. Federal agencies must implement 800-53 controls under the Federal Information Security Modernization Act (FISMA). The catalog also provides the control baselines used for FedRAMP authorization. For a complete breakdown of the catalog’s structure, see our NIST 800-53 complete guide.
CSF explains what strong cybersecurity looks like, and NIST 800-53 provides the controls organizations use to achieve it. But neither replaces the other.
NIST CSF and NIST 800-53: Side-by-Side Comparison
CSF and 800-53 differ across purpose, structure, audience, and implementation approach. The following table offers a side-by-side comparison of 800-53 vs CSF at the highest level.
| NIST CSF 2.0 | NIST 800-53 Rev 5 | |
| Type | Cybersecurity risk management framework | Security and privacy control catalog |
| Purpose | Organize and communicate cybersecurity risk management and program maturity | Specify security and privacy controls organizations implement to protect systems and data |
| Structure | 6 functions, 22 categories, 106 subcategories | 20 control families, 1,196 security and privacy controls |
| Approach | Voluntary, risk-based, outcome-oriented | Control-based with defined baselines (Low, Moderate, High) |
| Audience | All organizations (any sector, any size) | Primarily federal agencies and organizations supporting federal systems |
| Mandatory for | No one (voluntary guidance) | Federal agencies under FISMA; FedRAMP CSPs |
| Granularity | High-level outcomes | Detailed control requirements |
| Relationship | Maps TO NIST 800-53 controls | Provides controls FOR NIST CSF subcategories |
| Best for | Strategic planning, board reporting, risk communication, maturity assessment | Technical implementation, audit preparation, compliance assessment |
How to Use CSF and 800-53 Together
CSF provides strategic structure for managing cybersecurity risk but does not specify controls. NIST 800-53 provides detailed control requirements but does not organize those controls within a broader risk management framework.
Together, they form two halves of a complete cybersecurity approach. Most organizations integrate the two publications using a structured sequence:
- Use CSF to evaluate operational maturity across the six functions. Identify where the organization currently stands and where improvements are needed.
- Identify gaps using CSF profiles and implementation tiers. CSF 2.0 introduces Organizational and Community Profiles that define current state and target state.
- Select 800-53 controls that address each CSF subcategory. NIST provides CSF 2.0 Informative References that map CSF subcategories to relevant 800-53 controls.
- Implement, assess, and monitor controls. Use 800-53’s detailed guidance to build policies, configure systems, and conduct ongoing security assessments.
For more detailed guidance on CSF adoption, see our guide on how to implement NIST CSF 2.0.
How CSF 2.0 Maps to NIST 800-53 Controls
The publication of NIST CSF 2.0 in 2024 only strengthened its relationship with NIST 800-53. The update introduced the Govern function, expanded profile guidance, and added reference tools that link CSF subcategories directly to 800-53 controls.
How CSF Functions Map to 800-53 Control Families
Each NIST CSF function aligns with related control families in NIST 800-53. While the functions describe outcomes, the control families provide the safeguards used to achieve those outcomes.
| NIST CSF 2.0 Function | NIST 800-53 Control Families | Shared Security Focus |
| Govern (GV) | PM (Program Management), PL (Planning), RA (Risk Assessment) | Cybersecurity governance, risk management strategy, and security policy oversight |
| Identify (ID) | RA (Risk Assessment), CM (Configuration Management), PM (Program Management) | Organizational assets, systems, and risks that support cybersecurity planning |
| Protect (PR) | AC (Access Control), SC (System & Communications Protection), AT (Awareness & Training) | Safeguards that control access to systems and protect sensitive data |
| Detect (DE) | AU (Audit & Accountability), SI (System & Information Integrity) | System and network monitoring to detect cybersecurity events and anomalies |
| Respond (RS) | IR (Incident Response), AU (Audit & Accountability) | Investigation, containment, and management of cybersecurity incidents |
| Recover (RC) | CP (Contingency Planning) | System and operations restoration following a cybersecurity incident |
Detailed mapping occurs at the CSF subcategory level, where each subcategory maps to one or more 800-53 controls. For example, subcategory ID.AM-01 (inventory of physical devices and systems) maps to CM-8 (System Component Inventory) and PM-5 (System Inventory). Subcategory PR.AA-01 (identity and credential management) maps to AC-2 (Account Management) and IA-2 (Identification and Authentication), among others.
NIST publishes these mappings through the Cybersecurity and Privacy Reference Tool (CPRT), which provides structured, machine-readable mappings between CSF 2.0 subcategories and 800-53 controls. Organizations can also download the complete CSF 2.0 Informative References in Excel format. For organizations still using CSF 1.1, NIST also provides a legacy crosswalk spreadsheet mapping CSF 1.1 and the NIST Privacy Framework to 800-53 Rev 5.
How CSF Profiles Align with 800-53 Control Baselines
Many organizations use CSF Organizational Profiles to define their current cybersecurity posture and their target state. These profiles frequently align with the Low, Moderate, or High control baselines defined in NIST SP 800-53B.
| Profile Goal | 800-53 Alignment | Baseline Controls |
| Basic cybersecurity program | Low baseline | 149 controls |
| Mature enterprise security program | Moderate baseline | 287 controls |
| High-impact federal systems | High baseline | 370 controls |
Those that defines a high-maturity CSF target profile will often find that the corresponding safeguards align closely with the Moderate or High baseline in 800-53. For step-by-step guidance on applying these mappings, see our guide on NIST CSF 2.0 risk assessment.
When to Use NIST CSF, NIST 800-53, or Both
The right combination of NIST 800-53 and NIST CSF often depends on regulatory requirements, program maturity, and who the organization reports to.
NIST CSF is the stronger starting point for organizations that need a high-level structure for cybersecurity risk management. It works well for security programs in early stages that need strategic direction before selecting specific controls, and for teams that report cybersecurity posture to leadership or a board in business-friendly terms.
NIST 800-53 is the primary publication for federal agencies mandated by FISMA, cloud service providers pursuing FedRAMP authorization, and any organization conducting formal security assessments or system authorizations. The catalog provides the control-level detail that CSF does not.
Most mature organizations use both. CSF manages the cybersecurity program at a strategic level while 800-53 supplies the specific controls. This is especially common in higher education and government contracting, where security teams use CSF for leadership and accreditor communication while implementing 800-53 controls for federally funded systems.
Which Framework Fits Your Organization
The right combination depends on the type of organization and its compliance obligations.
| Organization Type | NIST Publication | Reason |
| Federal agency | Both | FISMA mandates NIST 800-53; EO 13800 directs CSF for risk management. |
| Cloud service provider (FedRAMP) | NIST 800-53 | FedRAMP authorization requires NIST 800-53 baselines; NIST CSF structures the broader program. |
| Defense contractor (CMMC) | NIST 800-53 (via NIST 800-171) | CMMC Level 2 derives from the NIST 800-53 Moderate baseline. |
| Higher education | Both | NIST 800-171 (from NIST 800-53) protects CUI in federally funded research; NIST CSF governs the institutional program. |
| Private enterprise | NIST CSF | NIST CSF provides voluntary structure; adopt NIST 800-53 controls as the program matures. |
| Startup or small business | NIST CSF | NIST CSF scales to any size; layer in NIST 800-53 controls as needs grow. |
Organizations that already use one publication can add the other with moderate effort, since NIST provides published mappings between the two.
How to Simplify CSF and 800-53 Compliance
Security programs that adopt both CSF and 800-53 usually outgrow spreadsheets fast. Coordinating assessments across two frameworks, collecting overlapping evidence, and reconciling results for different audiences pulls teams away from closing actual gaps.
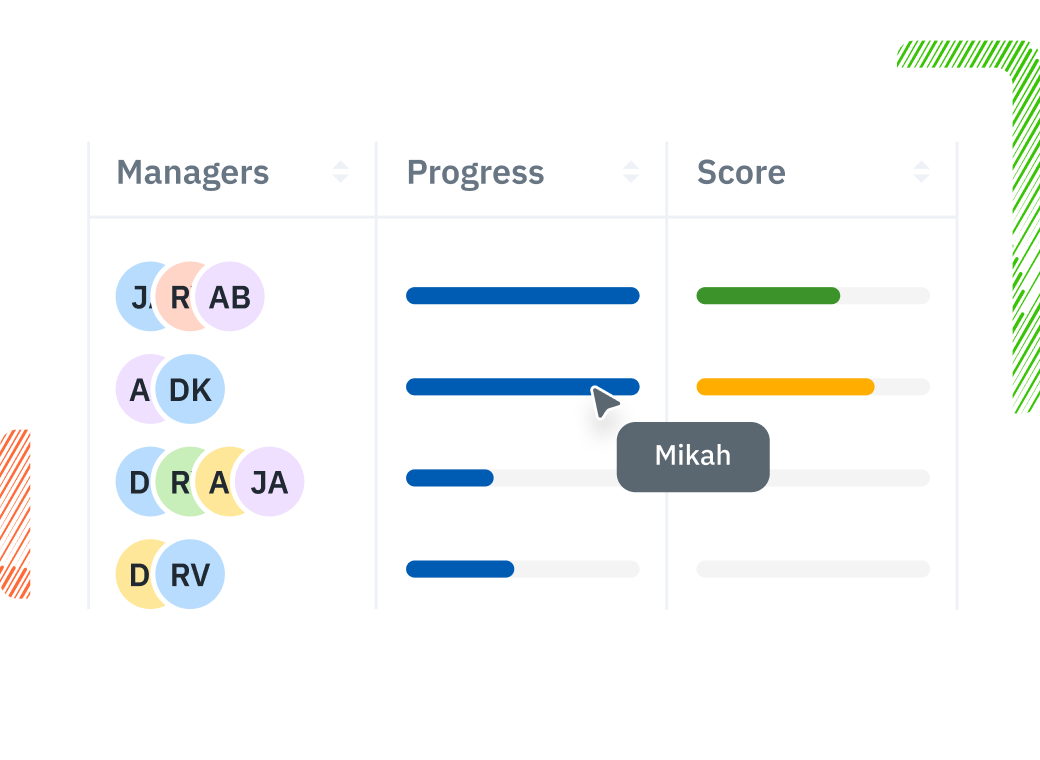
Isora GRC is the collaborative GRC Assessment Platform™ built for security teams to manage both frameworks in one shared workspace. Isora scales with your security program — supporting additional frameworks, vendors, and organizational units without losing consistency.
- Assessment management: Organize assessments by CSF function or 800-53 control family to streamline complex campaigns across both frameworks.
- Prebuilt questionnaires: Send framework-aligned questionnaires to control owners and collect responses and evidence in one place, reducing time spent on assessment tasks.
- Reports and scorecards: Generate scored reports that show CSF maturity and 800-53 control implementation side by side, freeing up time for strategic work.
See how Isora GRC simplifies CSF and 800-53 compliance. Or, explore our NIST 800-53 compliance software and NIST CSF compliance software pages for more product information.
NIST CSF vs 800-53 FAQs
What is the difference between NIST CSF and NIST 800-53?
NIST CSF is a high-level framework that helps organizations structure their cybersecurity program around six functions: Govern, Identify, Protect, Detect, Respond, and Recover. NIST 800-53 is a detailed catalog of 1,196 security and privacy controls across 20 families. CSF defines the outcomes organizations should achieve. NIST 800-53 provides the specific controls used to achieve those outcomes.
Is NIST CSF the same as NIST 800-53?
No. NIST CSF is a voluntary cybersecurity framework. NIST 800-53 is a control catalog required for U.S. federal information systems. CSF provides high-level, outcome-oriented guidance. NIST 800-53 provides specific, implementable controls. The two are complementary and many organizations use both within the same security program.
How does NIST CSF 2.0 map to 800-53?
NIST provides Informative References that connect CSF 2.0 subcategories to specific 800-53 controls. The Protect function maps to Access Control (AC) and System and Communications Protection (SC) families. The Detect function maps to Audit and Accountability (AU) and System and Information Integrity (SI) families. The Cybersecurity and Privacy Reference Tool (CPRT) provides interactive, machine-readable mappings.
Is NIST CSF mandatory?
No. NIST CSF is voluntary. Executive Order 13800 (2017) directed federal agencies to use CSF for managing cybersecurity risk, and CSF is increasingly referenced in regulations, but it carries no compliance mandate for private-sector organizations.
Can NIST CSF replace NIST 800-53?
No. CSF does not specify individual security controls, and 800-53 does not organize a full cybersecurity program. CSF provides the structure for managing cybersecurity risk. NIST 800-53 provides the controls used to implement that structure. Most mature security programs use both together.
Key Takeaways
NIST CSF and NIST 800-53 serve different but complementary roles in cybersecurity programs. CSF organizes risk management through six functions, profiles, and implementation tiers. NIST 800-53 provides 1,196 specific controls across 20 families that organizations implement to protect systems and data. NIST publishes official mappings between the two, making integration straightforward.
Whether the organization is a federal agency required to implement 800-53 under FISMA, a cloud service provider pursuing FedRAMP authorization, or a private company building a cybersecurity program from the ground up, the two publications work together: CSF defines what the security program should achieve, and 800-53 determines what controls to put in place.
Explore more NIST 800-53 framework comparisons in our comparison guide, or request a demo to see how Isora GRC supports both frameworks.
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.


















