 Table of Contents
Table of Contents
- NIST 800-53 vs Other Frameworks: Complete Comparison Guide
- Why Framework Comparisons Matter
- NIST 800-53 Framework Comparison
- Key Framework Differences
- When to Use Each Security Framework
- Framework-by-Framework Comparison
- How to Simplify Multi-Framework Compliance
- NIST 800-53 Framework Comparison FAQs
- Key Takeaways
NIST 800-53 vs Other Frameworks: Complete Comparison Guide
Most security teams use several information security frameworks to protect systems and data. One of the most widely adopted is NIST Special Publication 800-53 Revision 5. Also important are NIST 800-171, ISO 27001, the NIST Cybersecurity Framework (CSF), and the Cybersecurity Maturity Model Certification (CMMC). These frameworks often appear together in regulatory guidance, industry requirements, and security programs. However, because they serve different purposes, practitioners need to understand when and how to use each one.
Many teams start with NIST Special Publication 800-53 Revision 5 when building or improving security programs. But with 1,196 security and privacy controls across 20 families, 800-53 is also one of the most comprehensive framework, and isn’t always the best starting point. In fact, choosing the right framework depends on regulatory requirements, what type of data an organization handles, and the industry. Frameworks also differ in approach: some define controls, while others focus on program structure, governance, or certification.
This guide compares five major cybersecurity frameworks: NIST 800-53, NIST 800-171, ISO 27001, the NIST CSF, and CMMC. It includes a side-by-side comparison table, a decision guide by organization type, and detailed breakdowns that link to deeper framework comparisons. With this resource, organizations can determine whether NIST 800-53 fits their environment and how it works alongside other standards.
Why Framework Comparisons Matter
Understanding how NIST 800-53 relates to other security frameworks helps organizations design better security and compliance programs. Without this clarity, teams risk choosing the wrong framework, overlooking required standards, implementing controls that do not apply, or failing audits when required compliance obligations are missing.
This guide explains how the controls in NIST Special Publication 800-53 relate to other security standards, including NIST 800-171, ISO 27001, NIST CSF, and CMMC. Despite significant overlap, these frameworks differ in scope, structure, and certification options.
Multi-Framework Compliance
Security frameworks are designed to address different layers of security and compliance. Organizations meet multiple security standards at the same time as a result. For example:
- A DoD contractor might need to achieve CMMC certification while implementing NIST 800-171 and understanding how those requirements map to NIST 800-53 controls.
- A cloud provider pursuing FedRAMP authorization must implement 800-53 controls but may also pursue ISO 27001 certification for international customers.
- Universities and research institutions often implement 800-53 for federally funded research systems while considering ISO 27001 or NIST CSF for broader institutional security programs.
Shared Foundations
Fortunately, many of these frameworks share common foundations.
- NIST 800-171 Rev. 3 was derived from the NIST 800-53 Moderate baseline to protect Controlled Unclassified Information (CUI) in non-federal systems. The current Rev. 3 standard contains 97 security requirements across 17 families. CMMC Level 2 assessments currently reference the prior Rev. 2 (110 requirements), with DoD planning to transition to Rev. 3 through future rulemaking.
- NIST Cybersecurity Framework (CSF) was designed to work together with 800-53, organizing risk management activities at a program level, while NIST 800-53 provides the detailed controls used to implement them.
Reduced Complexity
Understanding how these frameworks relate to each other can help organizations map controls across frameworks, reduce duplicated efforts, and build security programs that satisfy multiple requirements at the same time. NIST publishes official crosswalk spreadsheets and mapping tools — including the Cybersecurity and Privacy Reference Tool (CPRT) and the Online Informative References (OLIR) program — that provide bidirectional mappings between 800-53, CSF 2.0, and other NIST publications.
NIST 800-53 Framework Comparison
The table below compares five major cybersecurity frameworks across scope, control coverage, certification options, and typical use cases.
| Framework | Publication | Category | Scope | Controls / Requirements | Certification | Use Cases | Relationship to 800-53 |
|---|---|---|---|---|---|---|---|
| NIST 800-53 | NIST Special Publication 800-53 Rev. 5. Security and Privacy Controls for Information Systems and Organizations | Controls Framework | Federal information systems and organizations | 1,196 controls 20 families Baselines |
No formal certification. Authority to Operate (ATO) through RMF FedRAMP authorization. |
Federal agencies, FedRAMP cloud providers, higher education with federal data | Is the reference catalog |
| NIST 800-171 | NIST Special Publication 800-171 Rev. 3. Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations | Controls Framework | Controlled Unclassified Information (CUI) in non-federal systems | 97 security requirements 17 families |
No formal certification. CMMC provides a certification pathway. | DoD contractors and subcontractor handling CUI | Derived from the NIST 800-53 Moderate baseline. It adapts a subset of controls for non-federal systems. |
| ISO 27001 | ISO/IEC 27001:2022 | Management Framework | Any organization worldwide | 93 controls in Annex A 4 control themes. Requires implementation of an ISMS. |
Yes. Organizations can obtain third-party certification through accredited auditors. | International organizations and private sector seeking recognized certification | Independent standard with similar control intent to 800-53 but structured differently. |
| NIST CSF | NIST Cybersecurity Framework 2.0 | Maturity Framework | Any organization. Adoption is voluntary. | 6 Functions 22 Categories 106 Subcategories |
No | Organizations building or maturing a cybersecurity program | Complementary. CSF organizes risk management. NIST 800-53 provides the detailed controls to implement. |
| CMMC | Cybersecurity Maturity Model Certification 2.0 | Maturity Framework | DoD contractors and subcontractors | Three maturity levels. Level 2 aligns with NIST 800-171 Rev. 2’s 110 security requirements. (DoD will transition to Rev. 3 through future rulemaking.) |
Yes. Level 2 requires third-party assessment. Level 3 requires government assessment. | DoD contractors bidding on contracts involving CUI | Indirect. CMMC Level 2 aligns with NIST 800-171, which itself was derived from 800-53. |
Key Framework Differences
Although NIST 800-53, NIST 800-171, ISO 27001, NIST CSF, and CMMC all address cybersecurity risk, they differ in two important ways: how compliance is validated and how security requirements are structured. Understanding these differences helps organizations determine when NIST 800-53 is appropriate and when another framework might be the better choice.
Certification vs Authorization
One major difference between frameworks is how organizations demonstrate compliance.
NIST 800-53 does not have a formal certification program. Instead, federal agencies obtain an Authority to Operate (ATO) through the Risk Management Framework (RMF), while cloud service providers obtain FedRAMP authorization. Both processes validate that the required NIST 800-53 controls have been implemented and assessed.
The RMF, defined in NIST SP 800-37 Rev. 2, establishes a seven-step lifecycle for selecting, implementing, assessing, authorizing, and monitoring security controls. Organizations implementing NIST 800-53 typically use this framework to manage the entire security authorization process. OMB Memorandum M-25-04 establishes the FY2025 FISMA reporting metrics aligned with NIST 800-53 and NIST CSF 2.0. For a deeper explanation, see our guide on how NIST 800-53 integrates with the RMF.
In contrast, organizations that require a recognized, globally portable certification often pursue ISO 27001, which offers third-party certification through accredited auditors.
Different Control Structures
Security frameworks also differ in how they define and organize security requirements. Some frameworks provide detailed technical controls, while others focus on higher-level cybersecurity activities or governance structures.
- NIST 800-53 includes 1,196 controls across 20 families, making it the most detailed control catalog. The companion publication SP 800-53B defines three baselines: Low (149 controls), Moderate (287), and High (370).
- ISO 27001 contains 93 Annex A controls organized across four themes, which are broader and less prescriptive. As of November 2025, all ISO 27001 certifications have transitioned to the 2022 edition — the ISO Survey 2024reports 96,709 valid certificates worldwide.
- NIST CSF defines 106 subcategories that operate at a higher strategic level rather than prescribing specific controls.
Because these frameworks operate at different levels, organizations often implement multiple frameworks together. For example, a security program may use NIST 800-53 to implement detailed controls, while using ISO 27001 or the NIST CSF to structure the overall security program.
So which framework is the right choice? In practice, the answer is often more than one.
When to Use Each Security Framework
The framework an organization needs depends on its industry, the type of data it handles, and its regulatory requirements. Some organizations must implement specific frameworks because they are mandated by law, while others adopt frameworks that help structure their security programs or support certification.
Federal Agencies
NIST 800-53 is mandatory under the Federal Information Security Modernization Act (FISMA). Agencies select a control baseline based on FIPS 199 system categorization and implement the corresponding 800-53 controls.
DoD Contractors
Organizations that process Controlled Unclassified Information (CUI) must comply with NIST 800-171. The Department of Defense enforces this requirement through CMMC certification, where Level 2 aligns with 800-171’s security requirements. For programs requiring stronger protections, NIST 800-172 (currently a Final Public Draft as of March 2026) defines enhanced security requirements that build on 800-171.
Cloud Providers for Federal Agencies
To work with U.S. federal systems, cloud services must obtain FedRAMP authorization, which is based on NIST 800-53 controls. FedRAMP’s 20x modernization initiative is currently in a limited Phase 2 pilot; the Rev. 5-based authorization path remains the only active production process. The required baseline (Moderate or High) depends on the sensitivity of the federal data being processed, stored, or transmitted.
International Organizations
Many global organizations pursue ISO 27001 certification because it is a globally recognized international security standard. Organizations that also work with U.S. federal systems may implement NIST 800-53 controls alongside ISO 27001.
Orgs Building a Security Program: Many organizations begin with NIST CSF and ISO 27001. The CSF helps structure cybersecurity activities, while ISO 27001 provides a structured approach for building and managing an Information Security Management System (ISMS). As programs mature, teams implement NIST 800-53 controls for detailed security requirements.
Higher Education Institutions
Universities often rely on NIST 800-53 when managing federally funded research systems or participating in federal programs. The EDUCAUSE Regulated Information Security Compliance (RISC) Community Group provides guidance for institutions navigating CMMC, NIST SP publications, and GLBA requirements. Many institutions also consider ISO 27001 certification or use the NIST CSF to structure broader institutional security governance.
| Organization / Scenario | Primary Framework | Reason | When NIST 800-53 Applies |
|---|---|---|---|
| Federal agency | NIST 800-53 | Required under FISMA | Always required for federal information systems |
| DoD contractor handling CUI | NIST 800-171, CMMC | Protection of Controlled Unclassified Information | Indirectly through 800-171. Enhanced protections in NIST 800-172 |
| Cloud provider serving federal agencies | FedRAMP | Required for federal cloud services | FedRAMP Moderate or High baseline controls |
| Organizations operating internationally | ISO 27001 | International certification standard | When handling U.S. federal data |
| Organizations building a security program | NIST CSF or ISO 27001 | Program structure and governance | Used later for detailed security controls |
| Higher education institutions | NIST 800-53, CSF, ISO 27001 | Federal research and institutional governance | When managing federally funded research systems |
Among these sectors, higher education institutions often face unique pressure: federal research grants may require NIST 800-53 controls, research partnerships can introduce CUI protection requirements (800-171/CMMC), and institutional governance may benefit from ISO 27001 or the NIST CSF.
But this situation is not unique to universities. Teams across many industries operate with multiple security frameworks because different regulations, customers, or certification programs impose different requirements.
The decision guide above can help organizations prioritize which framework to adopt first. When in doubt, begin with NIST CSF to establish program structure and implement NIST 800-53 controls later, as your program matures.
Framework-by-Framework Comparison
The sections below explain how NIST 800-53 compares with related security frameworks. Each comparison highlights who uses the framework, what they do with it, and why it matters.
NIST 800-53 vs 800-171
NIST 800-53 is the full security and privacy control catalog with 1,196 controls across 20 families, originally intended to protect federal information systems. NIST 800-171 Rev. 3 defines 97 security requirements across 17 families for protecting Controlled Unclassified Information (CUI) in non-federal systems.
The two frameworks are closely related. NIST created 800-171 by selecting controls from the NIST 800-53 Moderate baseline and adapting them for contractor environments. Rev. 3’s 97 requirements collectively represent 156 of the 287 moderate-baseline controls from SP 800-53B, as multiple 800-53 controls were merged into single requirements.
In practice, the choice depends on who operates the system and what data it contains:
- Federal agencies implement NIST 800-53 to secure federal information systems.
- DoD contractors and subcontractors handling CUI implement NIST 800-171 to protect that data in contractor-operated environments.
The key difference is how compliance is validated. CMMC Level 2 certification validates 800-171 compliance, creating an enforceable certification path that NIST 800-53 itself does not provide. Note that CMMC Level 2 assessments currently reference 800-171 Rev. 2 (110 requirements in 14 families); DoD will transition to Rev. 3 through future rulemaking.
ISO 27001 vs NIST 800-53
ISO 27001 is an internationally recognized, certifiable information security management system (ISMS) standard with 93 controls in Annex A. Organizations around the world implement ISO 27001 to establish a structured security management program and obtain third-party certification from accredited auditors.
NIST 800-53 is a prescriptive U.S. government control catalog with 1,196 security and privacy controls, designed primarily to secure federal information systems in the United States.
The most visible difference is certification. ISO 27001 offers third-party certification, allowing organizations to demonstrate compliance through audits conducted by accredited certification bodies. The ISO Survey 2024 reports 96,709 valid certificates across organizations in over 180 countries, making it the most widely recognized security certification globally. (The transition deadline from ISO 27001:2013 to the 2022 edition passed on October 31, 2025 — all current certificates are issued against the 2022 standard.)
NIST 800-53 does not have an equivalent certification mechanism. Instead, federal systems demonstrate compliance through authorization processes such as Authority to Operate (ATO) decisions and FedRAMP authorizations.
Another important difference is how the frameworks guide implementation. NIST 800-53 specifies detailed control requirements at defined baseline levels, while ISO 27001 takes a management-system approach that gives organizations more flexibility in how they address each control objective.
Despite these differences, the frameworks share significant overlap. NIST publishes an official SP 800-53 Rev. 5 to ISO 27001 mapping (available in the supplemental materials) that organizations use to map controls and reduce implementation and audit effort when pursuing ISO 27001 certification alongside 800-53 compliance.
NIST CSF vs NIST 800-53
The NIST Cybersecurity Framework (CSF) is a voluntary risk management framework organized into six functions: Govern, Identify, Protect, Detect, Respond, and Recover. These functions further break down into 106 subcategories that help organizations identify, manage, and communicate cybersecurity risk.
NIST 800-53 is a detailed control catalog with 1,196 specific controls for implementation.
The two frameworks are designed to work together rather than compete:
- CSF helps organizations understand and prioritize cybersecurity risks, while NIST 800-53 provides the detailed controls used to address those risks.
- CSF serves as an organizing framework for security programs, helping leadership understand risk posture and set priorities. NIST 800-53 provides the granular, implementation-level controls that translate those priorities into technical and operational safeguards.
- CSF 2.0 Informative References map directly to NIST 800-53 controls through the NIST Cybersecurity and Privacy Reference Tool (CPRT) and a downloadable CSF 2.0 to SP 800-53 crosswalk spreadsheet, making it straightforward to use CSF for program structure and NIST 800-53 for detailed control selection.
The CSF is voluntary and widely used across both public and private sectors, while NIST 800-53 is mandatory for U.S. federal agencies under FISMA. In December 2025, CISA released Cross-Sector Cybersecurity Performance Goals (CPG) 2.0, fully aligned with CSF 2.0’s six functions, providing a prioritized subset of security outcomes for critical infrastructure operators.
CMMC vs NIST 800-53
The Cybersecurity Maturity Model Certification (CMMC) 2.0 is a Department of Defense certification program that validates whether contractors have implemented required cybersecurity controls. Two final rules established the program: 32 CFR Part 170 (effective December 16, 2024) created the CMMC program structure, and a 48 CFR / DFARS rule (effective November 10, 2025) made CMMC contractually enforceable.
CMMC Level 2 currently aligns with NIST 800-171 Rev. 2’s 110 requirements, which are themselves derived from NIST 800-53’s Moderate baseline. This creates a hierarchy: 800-53 is the source catalog, NIST 800-171 is the subset for contractor systems handling CUI, and CMMC acts as the certification mechanism that validates those requirements.
CMMC was created to enforce compliance that was previously self-attested under DFARS 252.204-7012. Phase 1 (self-assessments for Level 1 and Level 2) took effect November 10, 2025. Phase 2, requiring Level 2 C3PAO third-party assessments, begins November 10, 2026. DoD will also transition CMMC assessments from 800-171 Rev. 2 to Rev. 3 (97 requirements, 17 families) through future rulemaking.
CMMC Level 3 introduces additional security requirements based on NIST SP 800-172 (Rev. 3 is currently a Final Public Draft as of March 2026), which extends selected NIST 800-53 controls to address advanced persistent threats in high-sensitivity DoD programs. This creates a direct link back to the original NIST 800-53 control catalog.
How to Simplify Multi-Framework Compliance
Regardless of which framework you adopt or how many you need to manage simultaneously, Isora GRC helps organizations track and report on compliance at scale. Managing multiple frameworks often means repeating the same assessments, collecting the same evidence, and combining reports manually. Isora helps teams manage these frameworks in one place.
Key capabilities include:
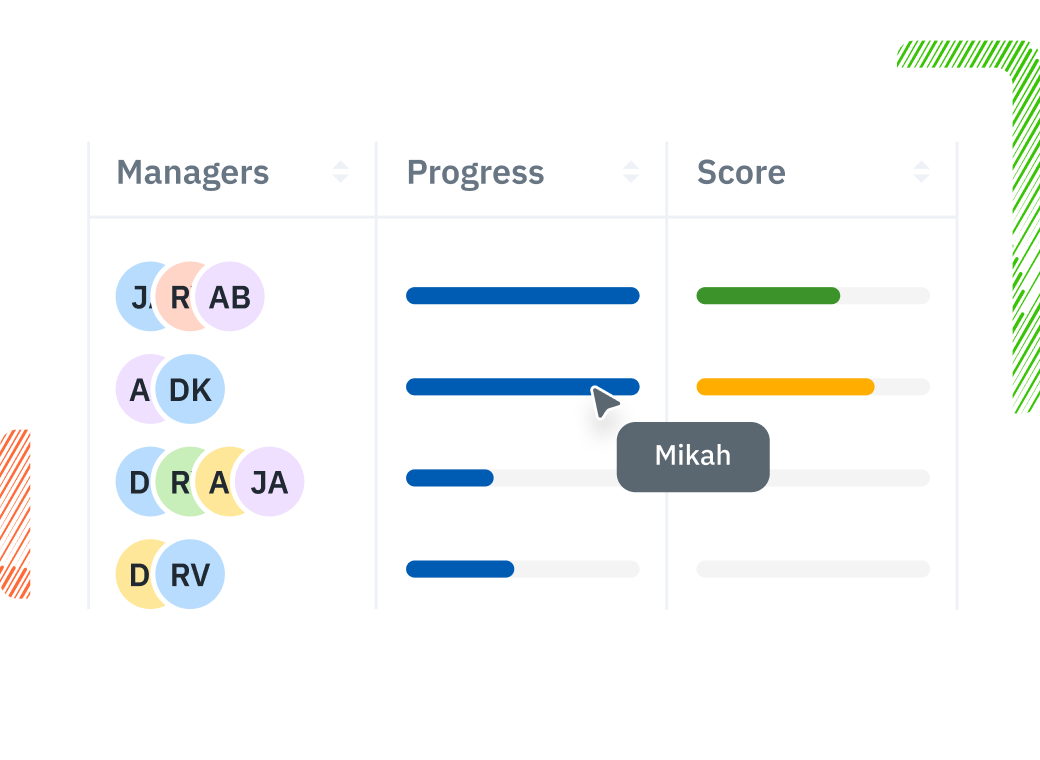
- Assessment Management: Organize assessments by framework and track progress from a single dashboard. When frameworks share requirements, teams can assess them once instead of repeating the same work.
- Prebuilt questionnaires: Send framework-aligned questionnaires to control owners, collect responses, and track completion in real time. Prebuilt questionnaires for common frameworks help teams start assessments quickly.
- Reports & Scorecards: Generate scored reports and visual summaries that show compliance progress across frameworks. Leadership can see risk levels and gaps without manually combining data from multiple sources.
Isora grows with your security program. As organizations adopt new frameworks or expand their environments, teams can continue managing assessments, risks, inventory, and reporting in one connected workspace.
See how Isora GRC streamlines compliance across frameworks like NIST 800-53, NIST CSF, NIST 800-171, and CMMC.
NIST 800-53 Framework Comparison FAQs
What is the difference between NIST 800-53 and 800-171?
NIST 800-53 is the full catalog of 1,196 security and privacy controls used to protect federal information systems. NIST 800-171 Rev. 3 contains 97 security requirements across 17 families, derived from the NIST 800-53 Moderate baseline. It applies to non-federal systems that handle Controlled Unclassified Information (CUI), such as those operated by DoD contractors and subcontractors. (The prior Rev. 2 had 110 requirements in 14 families.)
Is NIST 800-53 the same as NIST CSF?
No. The two frameworks serve different roles. NIST 800-53 is a detailed control catalog with 1,196 specific controls, while the NIST Cybersecurity Framework (CSF) is a voluntary risk management framework organized into six functions: Govern, Identify, Protect, Detect, Respond, and Recover. These functions help organizations understand risk and structure their cybersecurity programs.
The two frameworks are complementary:
- CSF helps organizations prioritize cybersecurity risks.
- NIST 800-53 provides the controls used to address those risks.
Many organizations use CSF for program structure and NIST 800-53 for implementation.
Can you be certified in NIST 800-53?
No, NIST 800-53 does not offer a formal certification program. Instead, federal systems demonstrate compliance through authorization processes:
- Authority to Operate (ATO) decisions under the Risk Management Framework (RMF)
- FedRAMP authorization for cloud services used by federal agencies
Both processes evaluate whether an organization has properly implemented the required NIST 800-53 controls. Organizations that need a third-party certification credential pursue ISO 27001 (96,709 valid certificates worldwide as of 2024) or CMMC.
Which NIST framework should I use?
The right framework depends on your role and regulatory requirements:
- Federal agencies must implement NIST 800-53 under FISMA.
- DoD contractors handling CUI must implement NIST 800-171 and obtain CMMC certification. CMMC Phase 1 (self-assessments) took effect November 2025; Phase 2 (mandatory C3PAO assessments) begins November 2026.
- Organizations building or improving a security program often start with the NIST Cybersecurity Framework (CSF).
Many organizations need multiple frameworks simultaneously. For example, a cloud provider serving federal agencies needs FedRAMP authorization (based on NIST 800-53) while also potentially pursuing ISO 27001 certification for international customers.
How does CMMC relate to NIST 800-53?
CMMC 2.0 is a Department of Defense certification program that validates contractor compliance with NIST 800-171, which is itself derived from NIST 800-53’s Moderate baseline. CMMC Level 2 currently maps to 800-171 Rev. 2’s 110 requirements (DoD will transition to Rev. 3 through future rulemaking). CMMC Level 3 adds enhanced security requirements based on NIST SP 800-172, which extends selected NIST 800-53 controls to defend against advanced persistent threats in high-sensitivity DoD programs. As of early 2026, CMMC Phase 1 (self-assessments) is in force, with Phase 2 (mandatory C3PAO assessments) beginning November 2026.
Do I need both NIST 800-53 and ISO 27001?
It depends on your regulatory requirements and business goals. Organizations that handle U.S. federal information must implement NIST-based controls such as NIST 800-53 or FedRAMP, while those seeking internationally recognized certification pursue ISO 27001. If you operate globally and serve federal agencies, you may need both, although organizations can map shared requirements to reduce duplicate work.
Key Takeaways
NIST 800-53 is the most comprehensive control catalog in the NIST ecosystem, but it is one piece of a larger compliance landscape. Understanding how it relates to other frameworks like NIST 800-171, ISO 27001, NIST CSF, and CMMC helps you choose the right approach for your security program.
Most teams end up working with more than one. Because these standards share significant control overlap (and NIST publishes official crosswalk tools like the CPRT to map between them) understanding their relationships makes it easier to reduce duplicate work and meet multiple requirements simultaneously.
Use the decision guide above to determine which frameworks apply to your organization, then explore our growing collection of comparison guides for a deeper look at how they work together.
Ready to manage multi-framework compliance? See how Isora GRC can help.
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.


















